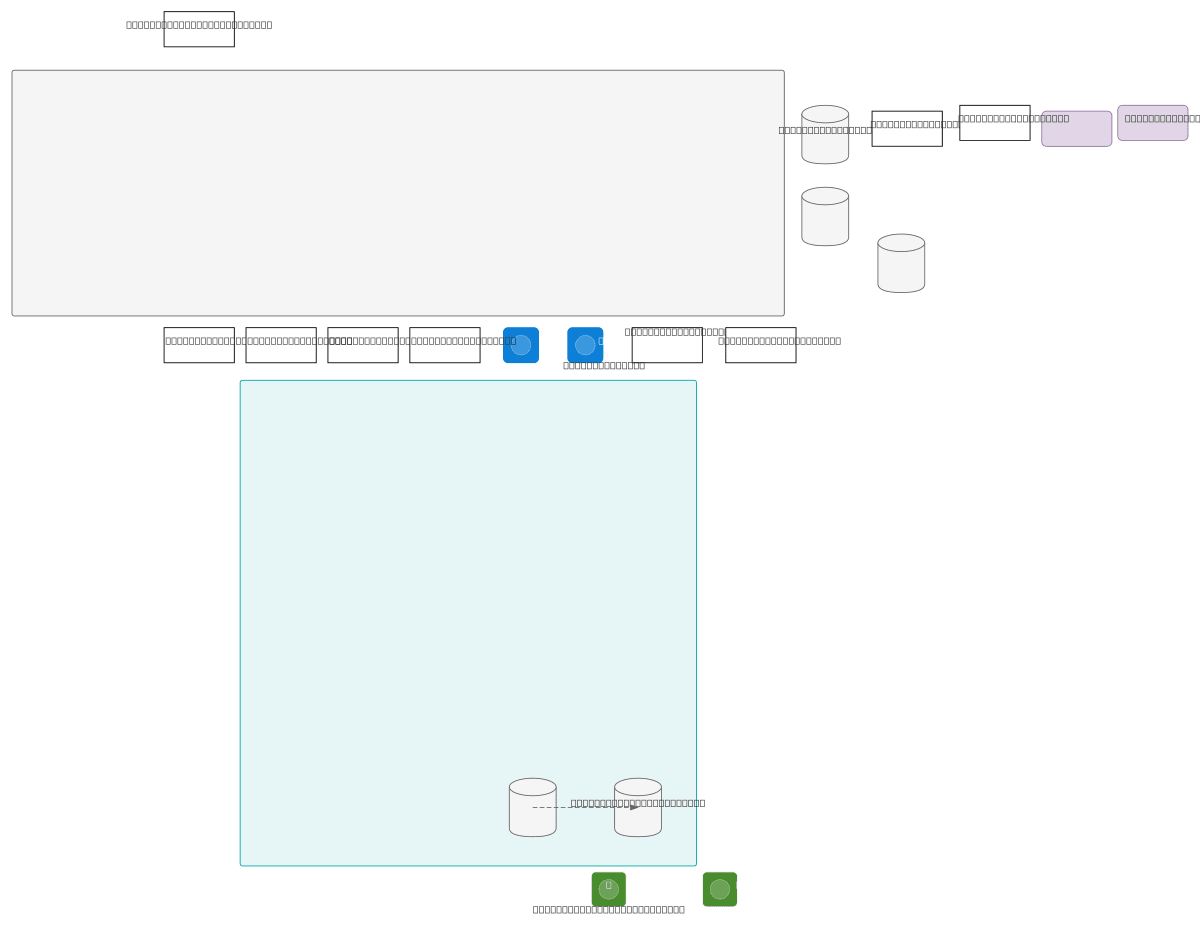
Steganography System DFD Level 1
About This Architecture
Data Flow Diagram Level 1 for a steganography system that encrypts sensitive data, embeds it into images using steganographic techniques, and detects hidden content via machine learning. User input flows through encryption and metadata storage before embedding into carrier images, which are then stored and analyzed by ML-based detection. This architecture demonstrates secure information hiding with automated detection and audit logging, critical for covert communications and forensic analysis workflows. Fork and customize this DFD on Diagrams.so to model your own steganography pipeline, adjust detection algorithms, or integrate additional data stores.
People also ask
How does a steganography system embed encrypted data into images and detect hidden content?
This DFD Level 1 diagram shows the complete flow: user data is encrypted, combined with metadata, embedded into carrier images via steganography, stored, and then analyzed by ML-based detection to identify and log hidden content. The system maintains audit trails and returns detection results to users.
- Domain:
- Security
- Audience:
- security architects and information hiding specialists designing steganography systems
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.