Zero Trust Network Access (ZTNA)
About This Architecture
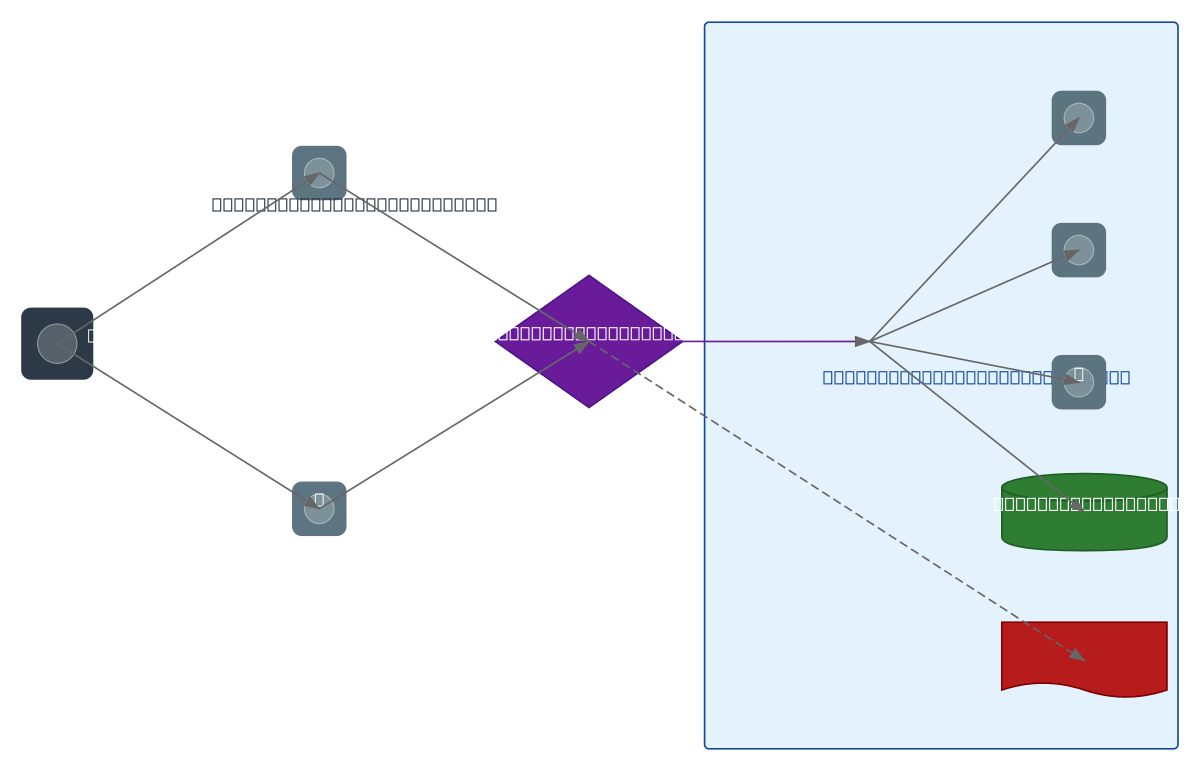
Zero trust network access model where a remote user authenticates via an Identity Provider (SSO/MFA) and Device Trust verification, passes through a context-aware Policy Engine, and connects over an encrypted mTLS tunnel to micro-segmented applications with full audit logging.
Architecture prompt
Zero trust network access model where a remote user authenticates via an Identity Provider (SSO/MFA) and Device Trust verification, passes through a context-aware Policy Engine, and connects over an encrypted mTLS tunnel to micro-segmented applications with full audit logging.
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.