Zero Trust Architecture
About This Architecture
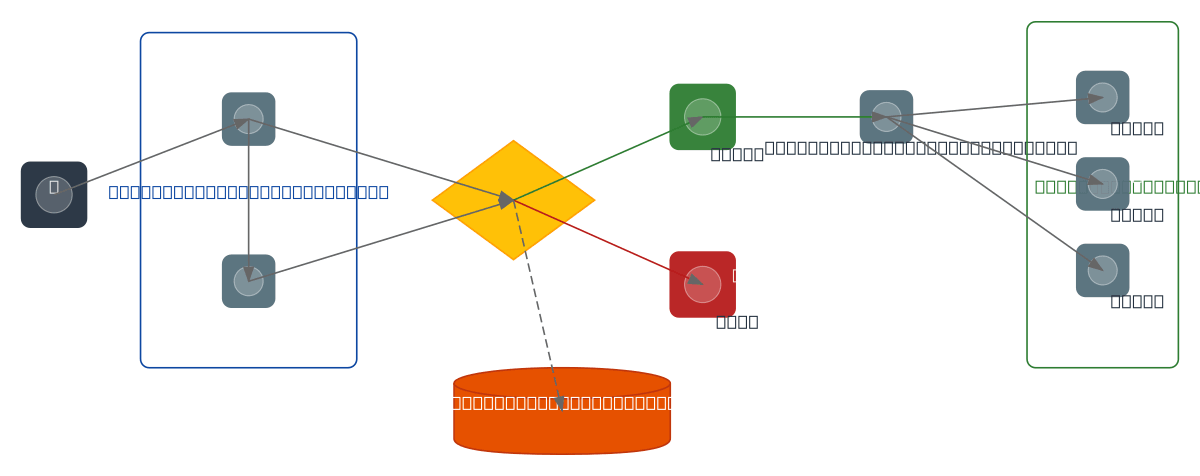
Zero Trust security model where every user goes through identity verification and device trust checks before a context-aware policy engine grants micro-segmented access to protected applications, with all decisions logged to an immutable audit log.
Architecture prompt
Zero Trust security model where every user goes through identity verification and device trust checks before a context-aware policy engine grants micro-segmented access to protected applications, with all decisions logged to an immutable audit log.
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.