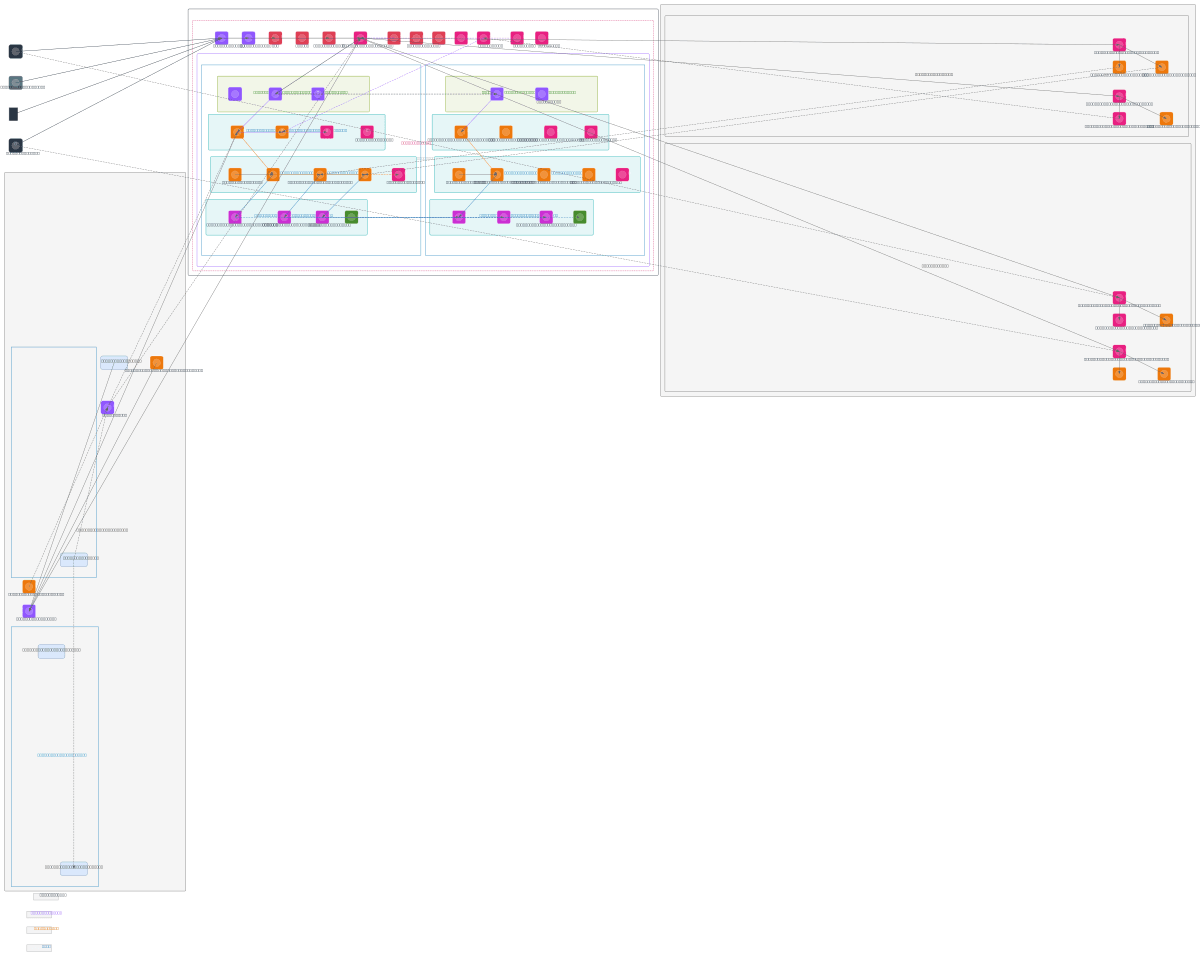
TO-BE API Governance and Middleware Architecture
About This Architecture
Multi-AZ API governance and middleware architecture on AWS using Route 53, CloudFront, WAF, and API Gateway to manage traffic from B2C, B2B, and partner systems. Request flow routes through Cognito authentication, API Gateway REST/HTTP endpoints, and AppSync GraphQL, then to ECS Fargate middleware, Lambda event handlers, and Step Functions orchestration across two availability zones. Application tier runs EC2 t3.large instances and ECS microservices with SQS queues, while data tier spans RDS Aurora (primary/standby), DynamoDB Global Tables, ElastiCache Redis, and S3 data lake with backup. Security is enforced via WAF, Shield, IAM, Secrets Manager, KMS, and CloudTrail audit logging across the VPC (10.0.0.0/16) spanning us-east-1a and us-east-1b. Fork this diagram on Diagrams.so to customize subnets, add additional Lambda functions, adjust instance types, or integrate with your governance policies and compliance requirements.
People also ask
How do I design a scalable, highly available API governance architecture on AWS with multi-AZ failover and middleware orchestration?
This diagram shows a production API governance platform spanning two AWS availability zones (us-east-1a and us-east-1b) with Route 53 DNS, CloudFront CDN, WAF, and API Gateway routing requests to ECS Fargate middleware, Lambda event handlers, and Step Functions orchestration. Data consistency is maintained via RDS Aurora primary/standby, DynamoDB Global Tables, and ElastiCache Redis replicas, whil
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing multi-tier API governance and middleware platforms
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.