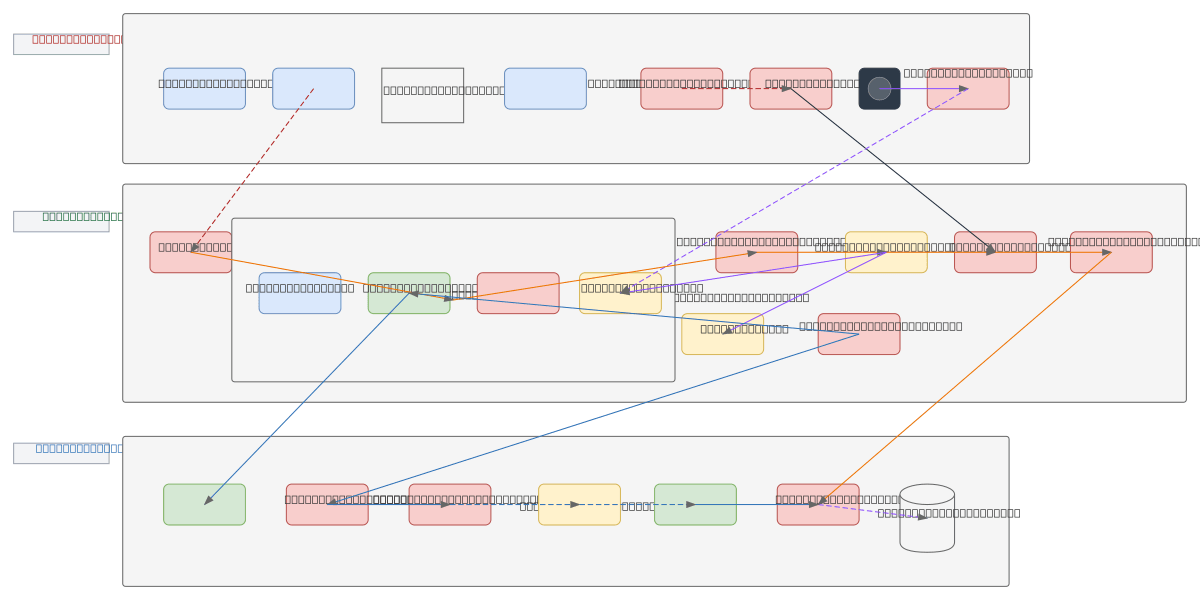
TEE/TDX Trusted Execution Protection Architecture
About This Architecture
Intel TDX and TEE trusted execution protection architecture isolates sensitive workloads in encrypted, hardware-protected domains isolated from the host OS, hypervisor, and untrusted applications. Data flows from untrusted sources through WAF/firewall into the TDX Module, where the Trusted Domain executes code in Secure Memory (TDMR) protected by the Memory Encryption Engine, with integrity measurements and attestation reports validated by remote verifiers. The architecture enforces least-privilege access through guardrail policies, seals sensitive data using TPM-backed key management, and maintains immutable audit logs for compliance and forensic analysis. Fork this diagram on Diagrams.so to customize threat models, add cloud-specific attestation services, or integrate with your zero-trust security framework. This pattern is essential for regulated workloads handling PII, financial data, or cryptographic keys in untrusted cloud environments.
People also ask
How does Intel TDX protect sensitive workloads from host OS and hypervisor attacks in cloud environments?
Intel TDX isolates trusted application code and data in encrypted Secure Memory (TDMR) protected by the Memory Encryption Engine, preventing host OS and hypervisor access. Remote attestation validates integrity through the Attestation Service, while TPM-backed key management seals sensitive data and immutable audit logs ensure compliance and forensic traceability.
- Domain:
- Security
- Audience:
- Security architects designing confidential computing and trusted execution environments
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.