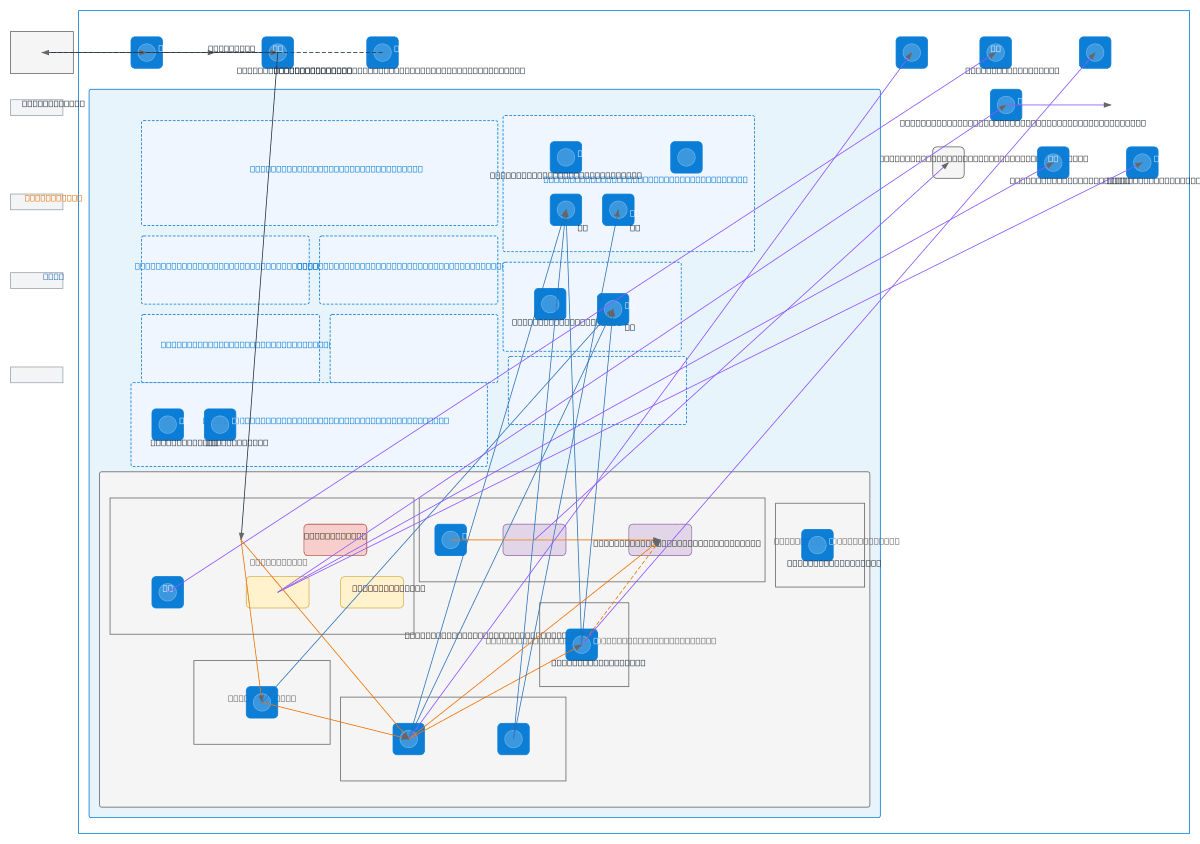
Single-Tenant Healthcare Platform - Azure Network
About This Architecture
Single-tenant healthcare platform on Azure with defense-in-depth network segmentation across six isolated subnets, each enforcing deny-by-default NSGs. Traffic flows from Internet through DDoS Protection Standard and Load Balancer to Envoy Gateway with Coraza WAF, then to frontend, backend, clinical services, and payments AKS pools running Cilium CNI with Hubble observability. Backend APIs orchestrate requests to MySQL and PostgreSQL Flexible Servers via Private Endpoints, Redis cache, and RabbitMQ messaging, while Dagster workers and KEDA-scaled jobs process async workloads; payments pods run in highest-isolation tainted namespace with dedicated Key Vault. Azure Monitor, Log Analytics, Application Insights, and Managed Grafana provide unified observability across compute, network, and data tiers. Fork this diagram to customize subnet ranges, add ExpressRoute for on-premises connectivity, or adjust HPA thresholds for your clinical workload patterns. The architecture demonstrates healthcare compliance best practices: network isolation, encryption at rest and in transit via cert-manager, external secrets management, and audit logging across all layers.
People also ask
How do I design a secure, compliant healthcare platform on Azure with network isolation and observability?
This diagram shows a defense-in-depth Azure healthcare architecture using AKS with Cilium CNI, six isolated subnets with deny-by-default NSGs, DDoS Protection Standard, and Envoy Gateway with Coraza WAF for threat protection. Payments pods run in highest-isolation tainted namespaces with dedicated Key Vault, while unified observability via Log Analytics, Application Insights, and Managed Grafana e
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing secure, multi-tenant healthcare platforms
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.