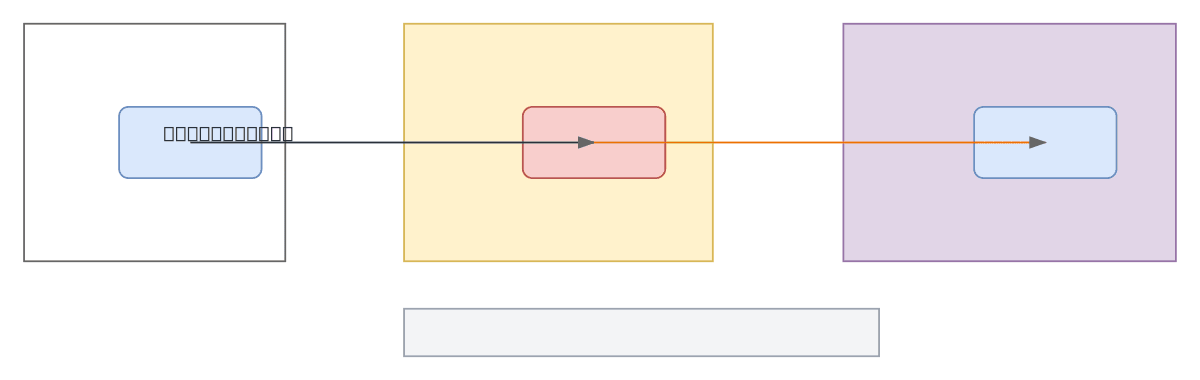
SFTP via TH Firewall - Updated Flow
About This Architecture
SFTP via TH Firewall architecture secures file transfers between an Application in the DMZ and ITMX (TH Regulator) on the LAN through a TH Firewall gateway. Traffic flows from Application to TH Firewall, then to ITMX, with SFTP protocol and GPG key exchange encryption protecting data in transit. This design isolates regulatory systems on a separate network segment while enforcing centralized access control and encryption at the firewall boundary. Fork this diagram on Diagrams.so to customize firewall rules, add redundancy, or integrate additional regulatory endpoints. The architecture demonstrates defense-in-depth by combining network segmentation (DMZ/LAN separation) with protocol-level encryption (GPG keys) for compliance-critical file exchange.
People also ask
How do I securely transfer files between an application and a regulatory system using SFTP and a firewall gateway?
This diagram shows SFTP traffic routed through a TH Firewall from an Application in the DMZ to ITMX (TH Regulator) on the LAN, with GPG key exchange encryption protecting the transfer. The architecture enforces network segmentation and centralized access control at the firewall boundary, meeting compliance requirements for regulatory file exchange.
- Domain:
- Networking
- Audience:
- network architects designing secure file transfer infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.