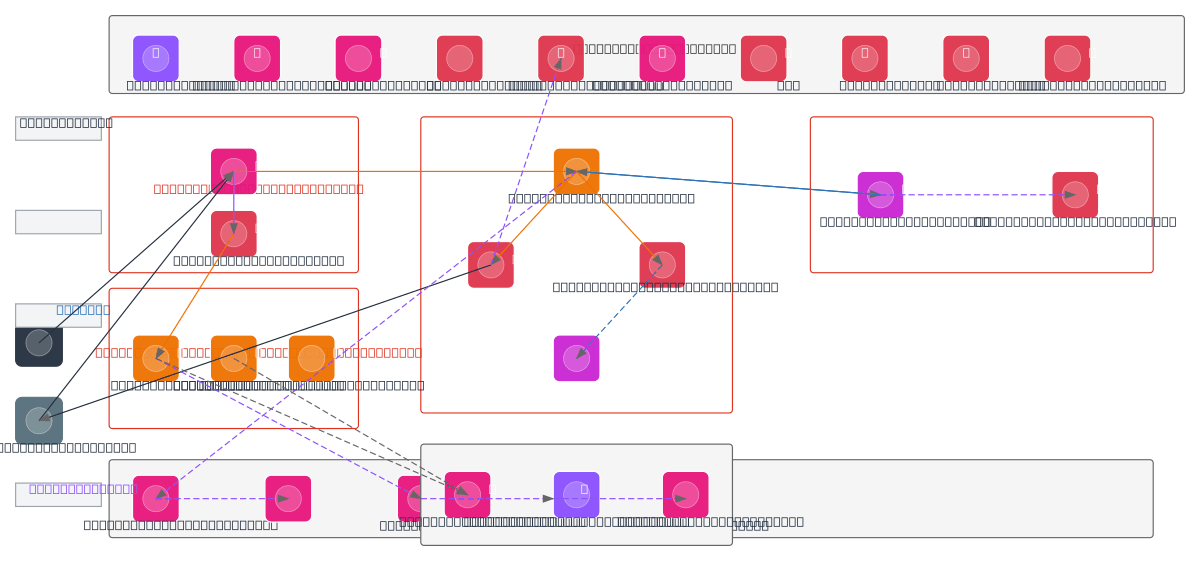
Secure JWT Authentication Architecture - AWS
About This Architecture
Secure JWT authentication architecture on AWS integrates API Gateway, Cognito, and a custom Auth Service to validate tokens and manage access across microservices. Users authenticate via Browser or Mobile Client, receiving JWT access and refresh tokens from the JWT Generator, with tokens verified by Cognito and stored in ElastiCache for fast validation. Auth events flow asynchronously through EventBridge to SNS for notifications and SQS for audit processing, while protected backend services (User Service and Resource Service) communicate through App Mesh with sidecar proxies for service discovery and observability. Shared infrastructure including Secrets Manager, KMS, WAF, Shield, CloudTrail, and CloudWatch provides encryption, DDoS protection, audit logging, and monitoring across all layers. Fork this diagram on Diagrams.so to customize token expiration policies, add additional bounded contexts, or integrate with your existing AWS security posture.
People also ask
How do I implement secure JWT authentication across AWS microservices with token validation, refresh token management, and audit logging?
This diagram shows a complete JWT auth flow: users authenticate via API Gateway and Auth Service, receiving access and refresh tokens from JWT Generator; tokens are validated by Cognito and cached in ElastiCache for performance. Auth events trigger async audit processing through EventBridge to SQS and Lambda, storing logs in S3, while KMS encrypts tokens and Secrets Manager secures database creden
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure microservices with JWT authentication
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.