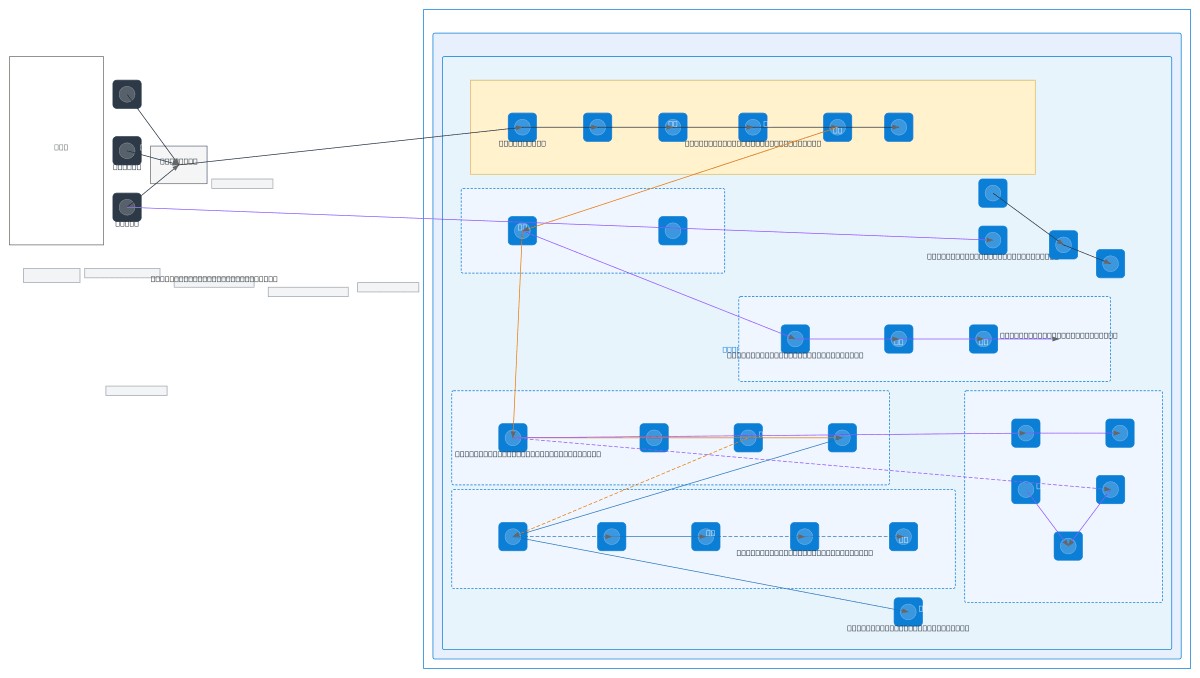
Secure Azure Online Banking Architecture
About This Architecture
Secure Azure online banking architecture with multi-layered network segmentation across six subnets: DMZ perimeter with WAF and DDoS protection, frontend Flask UI, identity and MFA services, .NET Core backend APIs, SQL databases with read replicas, and security operations with Key Vault and Sentinel. Data flows from internet-facing Azure Front Door through Application Gateway and NSG rules into isolated application tiers, with Service Bus queuing transactions and Private Link securing database endpoints. This architecture demonstrates defense-in-depth, role-based access control (RBAC), and compliance best practices critical for regulated financial workloads. Fork and customize this diagram on Diagrams.so to adapt subnets, add additional App Services, or integrate with your Azure governance policies.
People also ask
How do I design a secure Azure banking architecture with network segmentation, MFA, and compliance monitoring?
This diagram shows a production banking architecture spanning six subnets: DMZ with WAF and DDoS, Flask frontend, Azure AD with MFA, .NET Core APIs, SQL databases with read replicas, and security operations with Key Vault and Sentinel. Private Link secures database endpoints, Service Bus queues transactions, and RBAC enforces least-privilege access for customers, tellers, and admins.
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing secure banking and financial services infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.