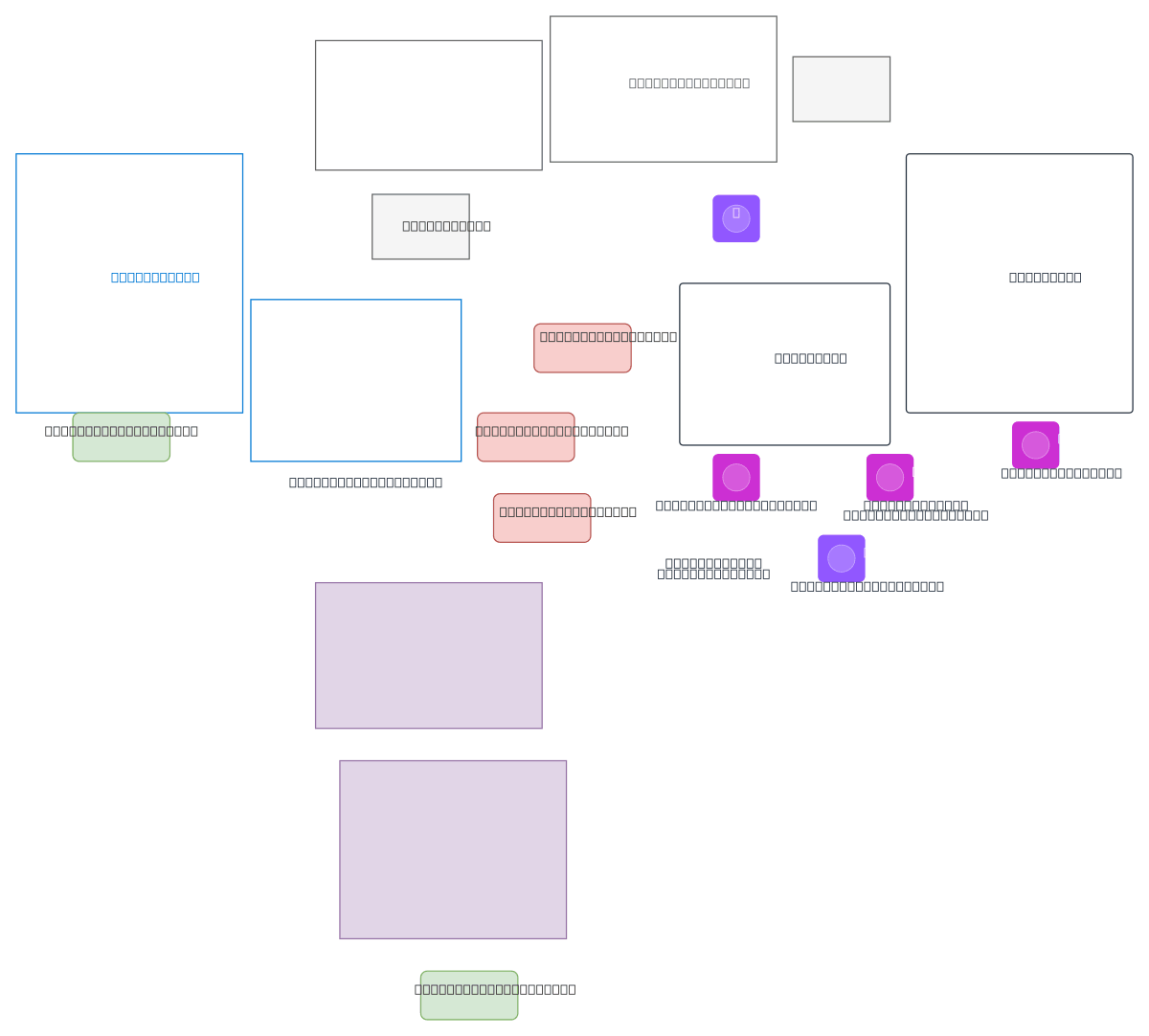
SASE Cross-Cloud Lakeflow to AWS Databases
About This Architecture
Secure Databricks Lakeflow data replication from Azure to AWS databases using Cato SASE as a unified inspection and enforcement backbone. Traffic flows from Azure Databricks through Cato Socket, Cato PoP, and Cato Cloud Routing Fabric to an IPsec-compliant gateway protecting PostgreSQL and MySQL in AWS, with NSGs and security groups enforcing deny-by-default policies. This architecture eliminates direct internet exposure, centralizes policy enforcement across cloud boundaries, and ensures only authenticated Lakeflow CDC traffic reaches databases via encrypted IPsec tunnels. Fork and customize this diagram on Diagrams.so to model your own multi-cloud data governance topology with SASE overlay networks. The design demonstrates zero-trust principles by blocking all unapproved routes and requiring cryptographic verification at every hop.
People also ask
How do I securely replicate Databricks data from Azure to AWS databases while enforcing zero-trust policies across cloud boundaries?
Use a SASE overlay like Cato to create a unified inspection and enforcement backbone. Route Databricks Lakeflow through Cato Socket in Azure, then through Cato PoP and Cloud Routing Fabric to an IPsec-compliant gateway protecting AWS databases. Enforce deny-by-default NSG and security group rules, allowing only authenticated CDC traffic over encrypted IPsec tunnels.
- Domain:
- Cloud Multi
- Audience:
- Security architects designing zero-trust cross-cloud data pipelines
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.