Reverse Bastion - Remote Support Architecture
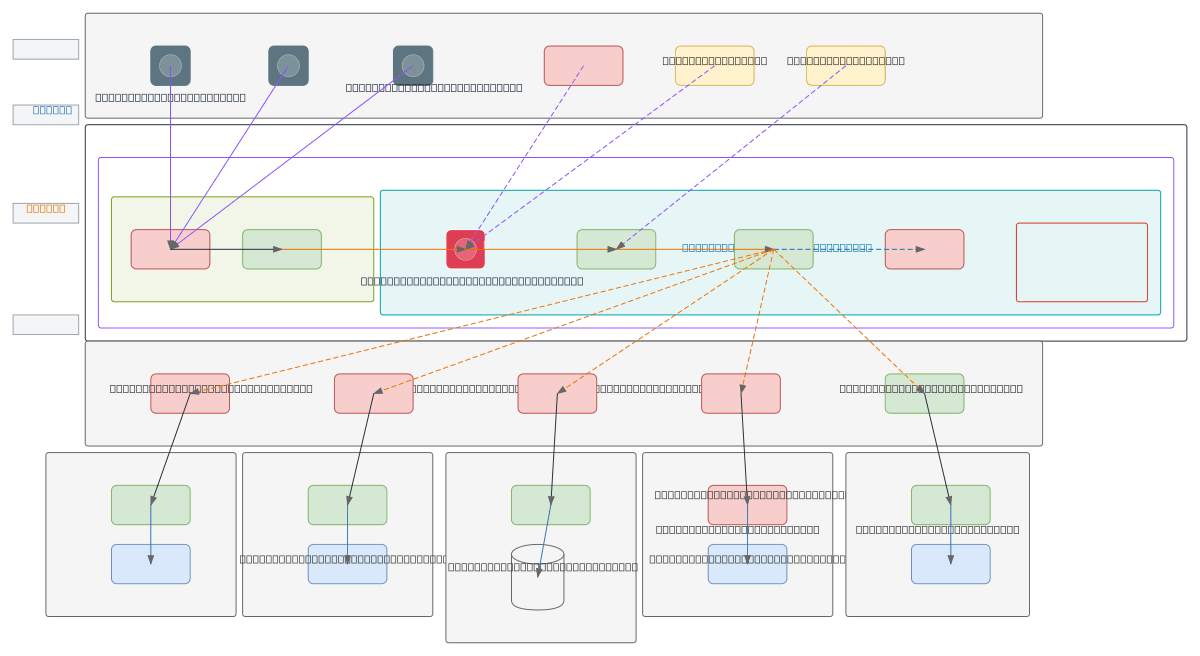
About This Architecture
Reverse bastion architecture enables secure remote support by inverting traditional inbound access—customers initiate outbound tunnels to a central bastion host rather than exposing infrastructure to inbound connections. The bastion, deployed as an EC2 instance with Apache Guacamole gateway in a private subnet behind WAF and NLB, brokers multi-protocol sessions (SSH, RDP, VNC) while Secrets Manager stores credentials and MFA/SSO enforces identity verification. Multiple tunnel agents (Reverse SSH, WireGuard, Frp/Ngrok) from customer sites establish persistent outbound connections, eliminating firewall rules for inbound access and reducing attack surface. This pattern solves the compliance and security challenge of granting remote access without opening inbound ports, implementing least-privilege access with full session audit logging and SIEM integration. Fork this diagram on Diagrams.so to customize tunnel protocols, add additional identity providers, or adapt the VPC topology for your multi-tenant support environment.
People also ask
How do I implement secure remote support without exposing inbound ports to my infrastructure?
A reverse bastion architecture inverts traditional access by having customer sites initiate outbound tunnels to a central AWS bastion host running Apache Guacamole. This diagram shows how to broker SSH, RDP, and VNC sessions through a private EC2 instance with Secrets Manager credentials, MFA/SSO identity verification, and full SIEM audit logging—eliminating inbound firewall rules while maintainin
- Domain:
- Security
- Audience:
- Security architects and DevOps engineers implementing zero-trust remote support infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.