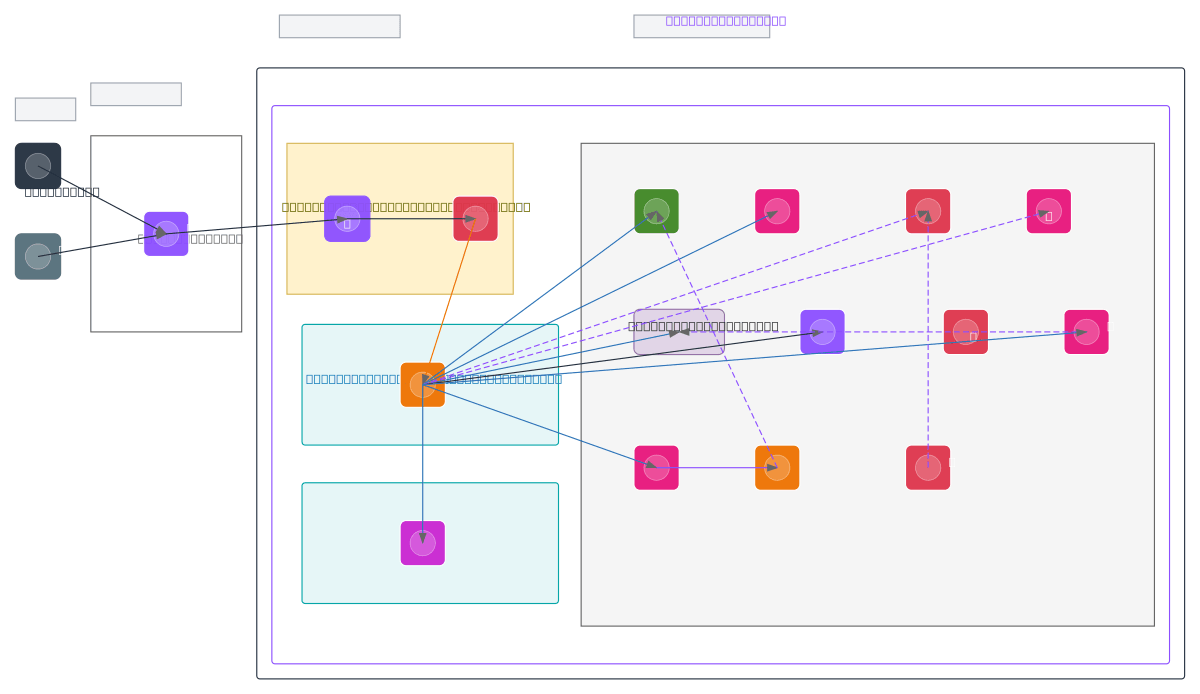
Prometrica — AWS Linux VPS Architecture
About This Architecture
Prometrica's AWS Linux VPS architecture combines a hardened EC2 instance running NestJS API with a multi-layer security perimeter including Route 53, ACM, WAF, and public/private subnet isolation across a 10.0.0.0/16 VPC. The t3.medium EC2 instance in the private app subnet connects to RDS PostgreSQL for persistence, S3 for file storage, SES for email, and SQS for asynchronous job processing, with Lambda handling report generation. Secrets Manager and KMS provide encryption and credential management, while CloudWatch monitors application health and SNS routes notifications to Twilio for SMS and voice alerts. This architecture demonstrates defense-in-depth with DMZ isolation, managed service integration, and event-driven workflows ideal for candidate management platforms requiring compliance and scalability. Fork this diagram on Diagrams.so to customize subnets, add auto-scaling groups, or integrate additional AWS services like DynamoDB or ElastiCache.
People also ask
How do I design a secure AWS VPS architecture with NestJS API, RDS database, and asynchronous job processing using SQS and Lambda?
Prometrica's architecture isolates the NestJS API in a private app subnet behind WAF and Internet Gateway, connects to RDS PostgreSQL in a separate data subnet, and decouples long-running tasks via SQS triggering Lambda for report generation. Secrets Manager and KMS encrypt credentials, while CloudWatch and SNS provide monitoring and alerting to Twilio.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure, scalable VPS-based applications with managed services
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.