Projet X-Wing — Architecture IT/OT Securisee
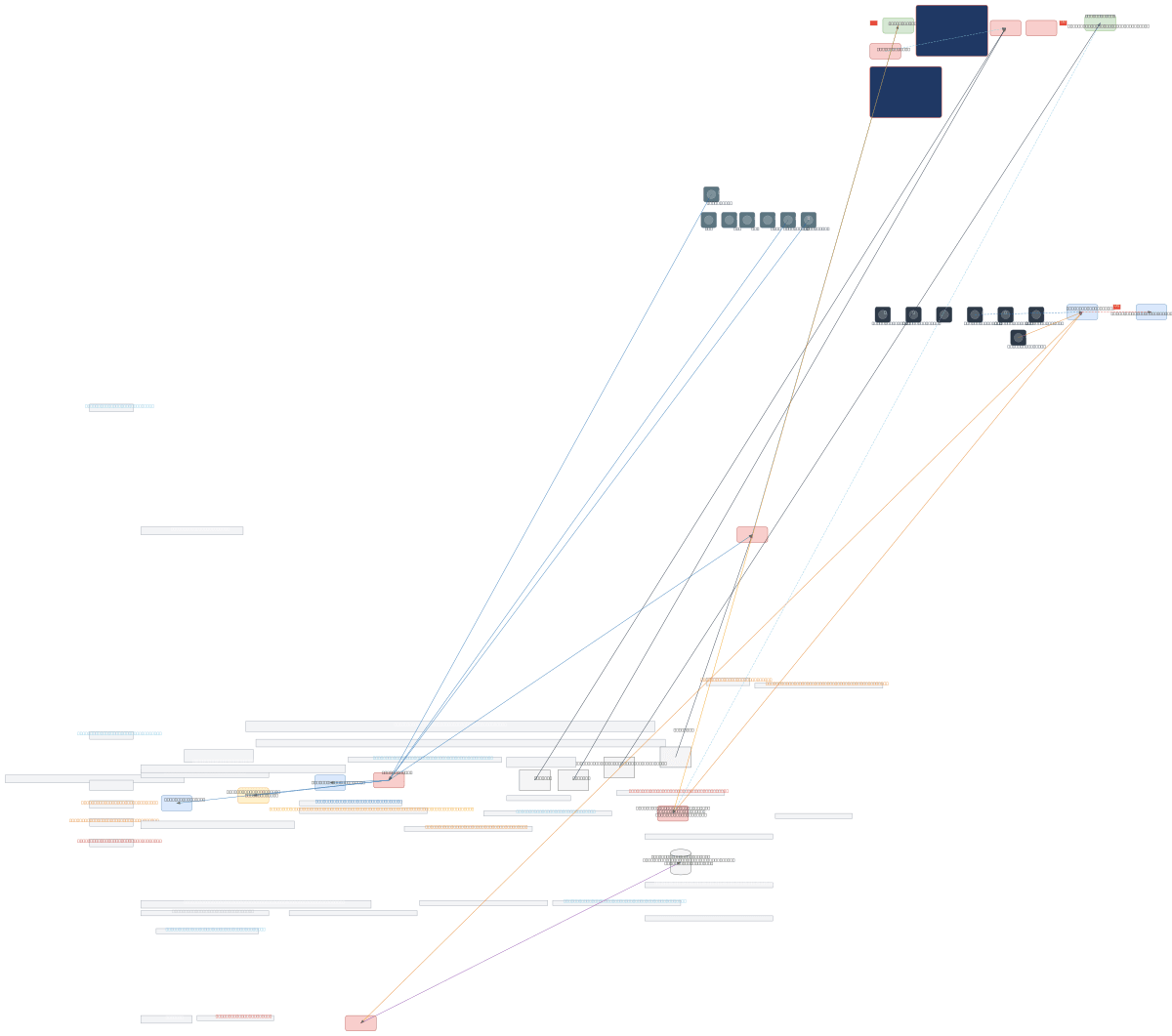
About This Architecture
Project X-Wing implements a Purdue-model industrial network architecture with strict IT/OT segmentation across five hierarchical levels, enforcing zero-trust access controls and deny-by-default filtering at every boundary. Data flows from Internet through dual-redundant firewalls (FW1 HA cluster) into the enterprise IT zone (SIE), then through an industrial DMZ (FW2) to production systems (SII) running 3D printers and SCADA supervision, with blockchain-based immutable traceability for aerospace and medical device compliance. The design combines Active/Passive firewall failover, ZTNA gateways with MFA, bastion hosts with session logging, and micro-segmentation via FW4 to enforce least-privilege access and exhaustive audit trails across all zones. This architecture demonstrates ISA/IEC 62443 hardening practices critical for high-availability industrial environments handling regulated manufacturing. Fork this diagram on Diagrams.so to customize firewall rules, add site-specific VLANs, or integrate your own OT protocols and compliance frameworks.
People also ask
How do you design an ISA/IEC 62443-compliant industrial network that separates IT and OT zones while maintaining high availability and audit compliance?
Project X-Wing uses the Purdue model to segment five hierarchical levels (Internet, IT/SIE, DMZ, production/SII, and field devices) with dual-redundant firewall clusters, zero-trust ZTNA gateways requiring MFA, and deny-by-default rules. Blockchain-based traceability logs all production events immutably, meeting aerospace (EN 9100) and medical (ISO 13485) compliance while bastion hosts and micro-s
- Domain:
- Security
- Audience:
- Industrial security architects designing ISA/IEC 62443-compliant OT/IT networks with zero-trust segmentation
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.