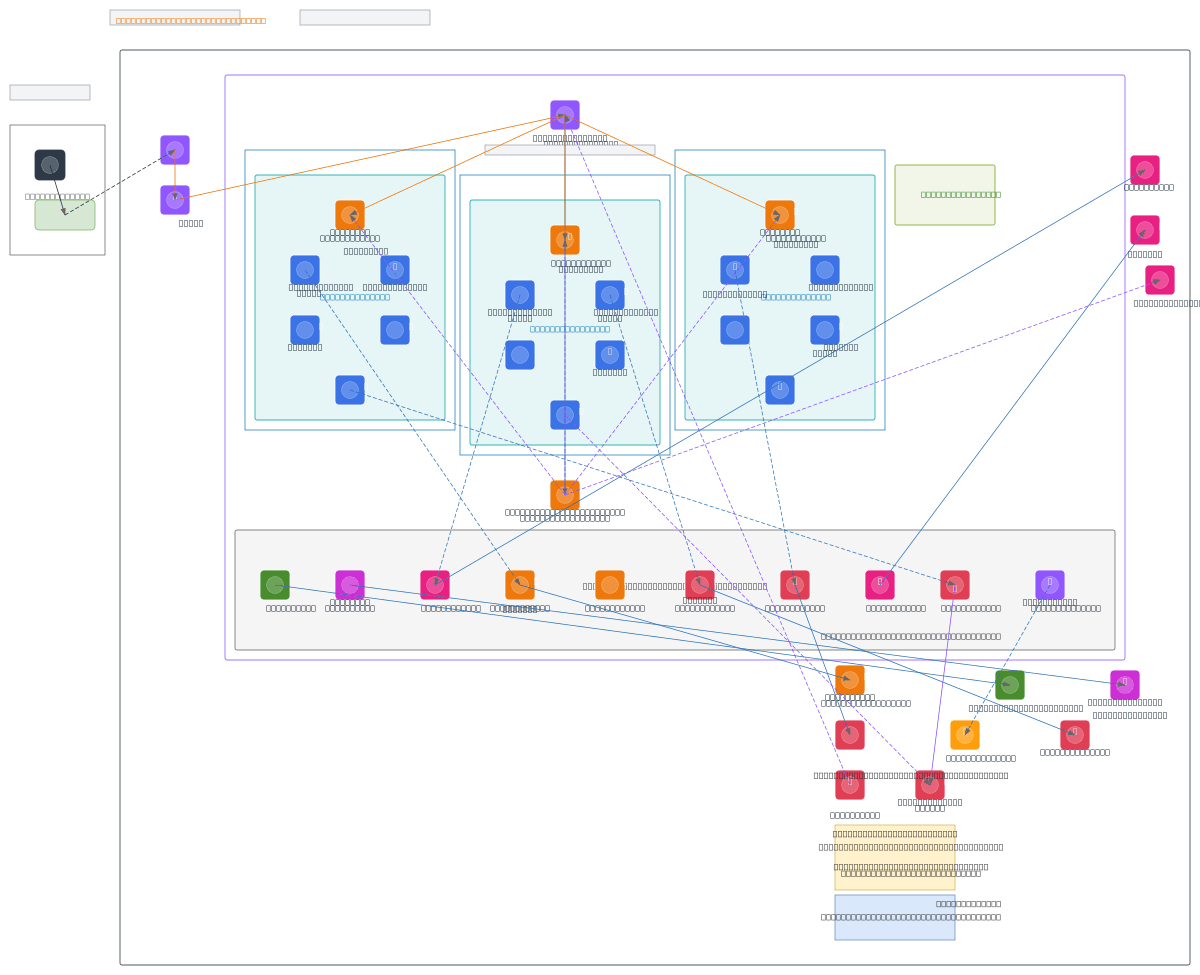
PitiaA - Private EKS Platform (eu-west-1)
About This Architecture
PitiaA is a private EKS platform in AWS eu-west-1 combining a three-AZ managed Kubernetes cluster with on-premises hybrid connectivity via Transit Gateway and Site-to-Site VPN. The architecture routes corporate users through an on-prem VPN gateway to an internal ALB (HTTPS/ACM) fronting EKS nodes across eu-west-1a, eu-west-1b, and eu-west-1c private subnets, with PitiaA agent pods, CoreDNS, AWS LB Controller, and IRSA ServiceAccounts managing workload identity. VPC endpoints for S3, DynamoDB, ECR, SQS, SSM, STS, Bedrock, and Textract enable private AWS service access without internet egress, while Terraform remote state and locks persist in S3 and DynamoDB. This design enforces zero-trust networking—no public node IPs, internal ALB only, and restrictive security groups—ideal for regulated workloads requiring compliance isolation and on-premises integration. Fork this diagram on Diagrams.so to customize subnets, add additional AZs, or adapt VPC endpoint configurations for your hybrid cloud strategy. The architecture demonstrates AWS best practices for private EKS: managed node groups, IRSA for least-privilege pod authentication, and PrivateLink for secure AWS service consumption.
People also ask
How do you design a private EKS cluster with on-premises connectivity and zero-trust security for regulated workloads?
PitiaA demonstrates a three-AZ private EKS architecture in AWS eu-west-1 that integrates on-premises networks via Transit Gateway and Site-to-Site VPN, routes traffic through an internal ALB with ACM TLS, and isolates workloads in private subnets with no public node IPs. VPC endpoints for ECR, S3, DynamoDB, SQS, and other AWS services enable private service access, while IRSA ServiceAccounts enfor
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing private EKS platforms with hybrid connectivity
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.