PitiaA AWS Private API - VPN to EKS Architecture
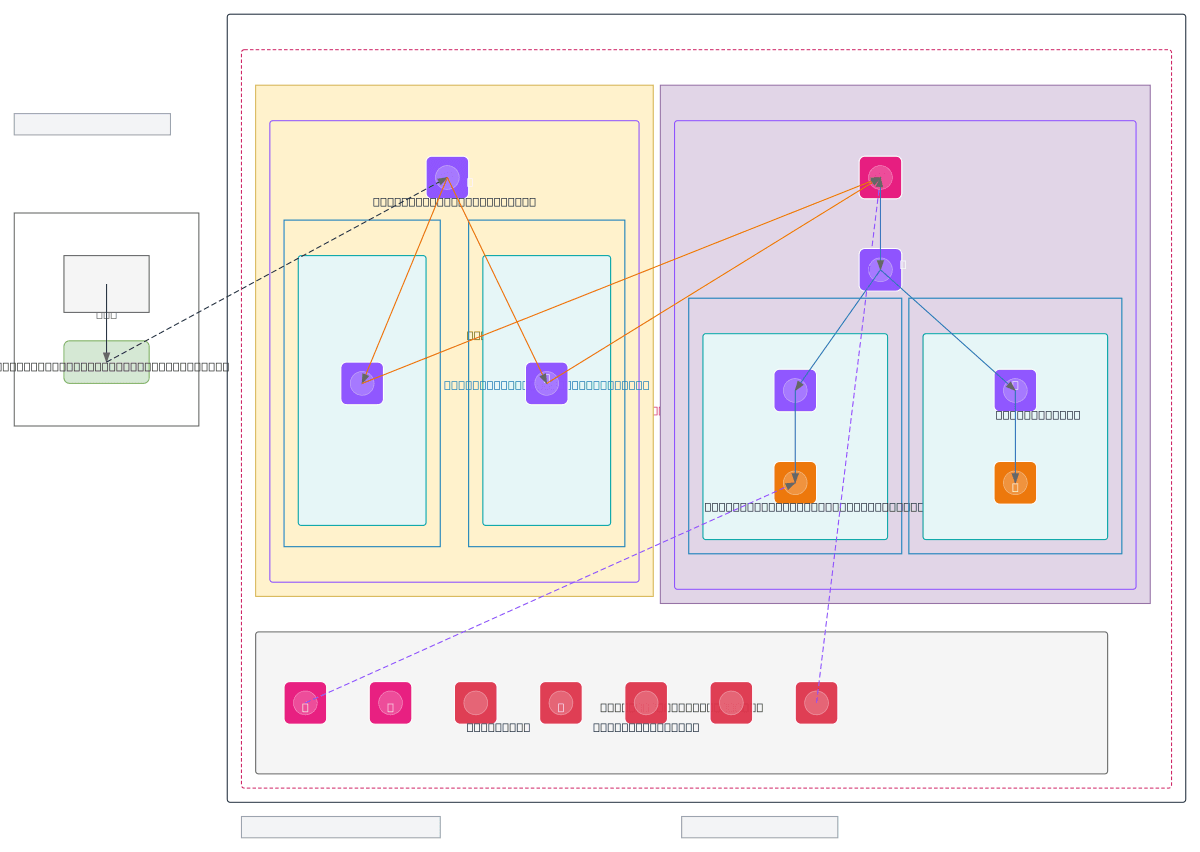
About This Architecture
Hybrid VPN architecture connecting on-premises Gobierno de Canarias infrastructure to a private EKS cluster via AWS Site-to-Site VPN and VPC Interface Endpoints. Traffic flows from the on-prem router through a Virtual Private Gateway into a DMZ Ingress VPC, then via VPC Link to a private API Gateway endpoint that routes requests to Internal ALBs fronting EKS node groups across two availability zones. The design enforces zero-trust principles with WAF protection, resource-based policies limiting API Gateway access to the Ingress VPC, and comprehensive observability through CloudWatch, CloudTrail, and GuardDuty. Fork this diagram to customize CIDR blocks, add additional VPCs, or integrate with your own hybrid network topology. The three-layer architecture (Access, Distribution, Core) provides clear blast radius isolation and simplifies troubleshooting across on-prem and AWS boundaries.
People also ask
How do I securely connect on-premises infrastructure to a private EKS cluster using AWS VPN and API Gateway?
This diagram shows a three-layer hybrid architecture: on-premises traffic enters via Site-to-Site VPN through a Virtual Private Gateway into a DMZ Ingress VPC, then routes through VPC Interface Endpoints to a private API Gateway protected by WAF and resource policies. The API Gateway uses VPC Link to reach Internal ALBs fronting EKS node groups across multiple availability zones, with CloudWatch,
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure hybrid connectivity to EKS clusters
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.