Password Reset Process Flowchart
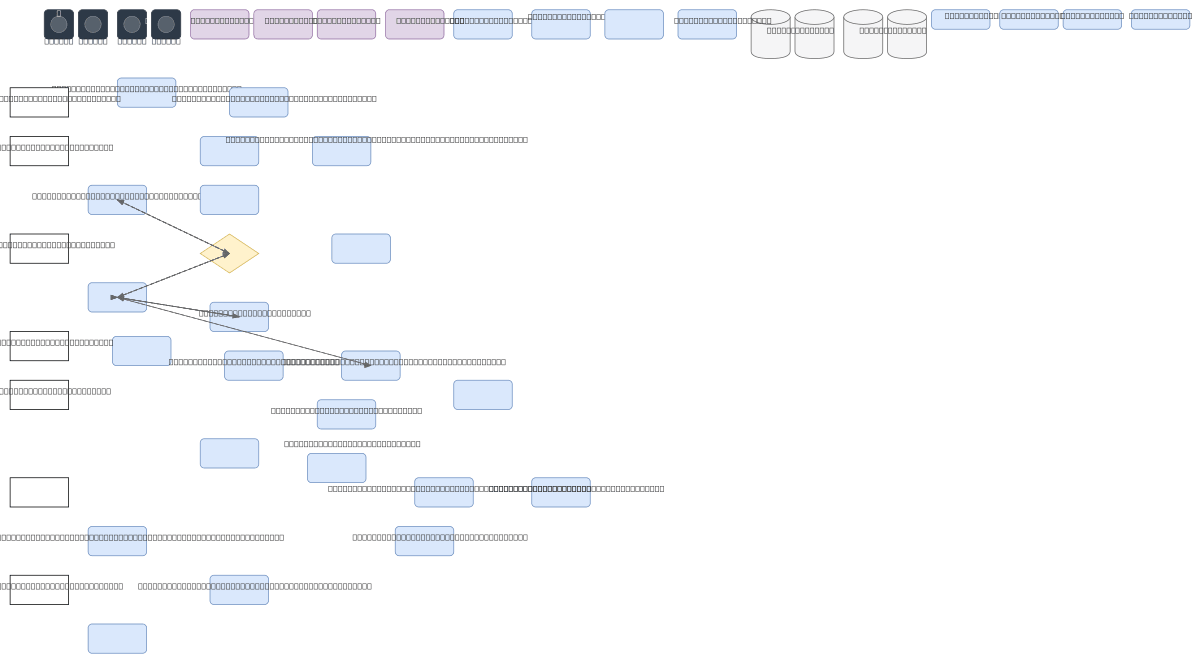
About This Architecture
Secure password reset process flow on OCI with email validation, time-limited token generation, and password strength enforcement. The workflow validates user email existence, generates a unique reset token stored in the database, sends a secure reset link via email, and validates token expiry and password strength before updating credentials. This architecture demonstrates defense-in-depth principles: email verification prevents account enumeration, time-limited tokens reduce brute-force risk, and password strength checks enforce security policy. Fork this diagram on Diagrams.so to customize token expiry duration, integrate with OCI Identity and Access Management, or adapt for multi-factor authentication flows. Consider adding rate limiting on email submission and token validation endpoints to mitigate abuse.
People also ask
How should I design a secure password reset flow that prevents account enumeration and token abuse?
This diagram shows a secure password reset pattern: validate email existence without revealing whether accounts exist, generate unique time-limited tokens stored server-side, send reset links via email, and enforce password strength before updating credentials. This approach prevents enumeration attacks, limits token replay risk, and ensures only legitimate users with email access can reset passwo
- Domain:
- Security
- Audience:
- Security architects and identity management engineers designing secure password reset flows on OCI
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.