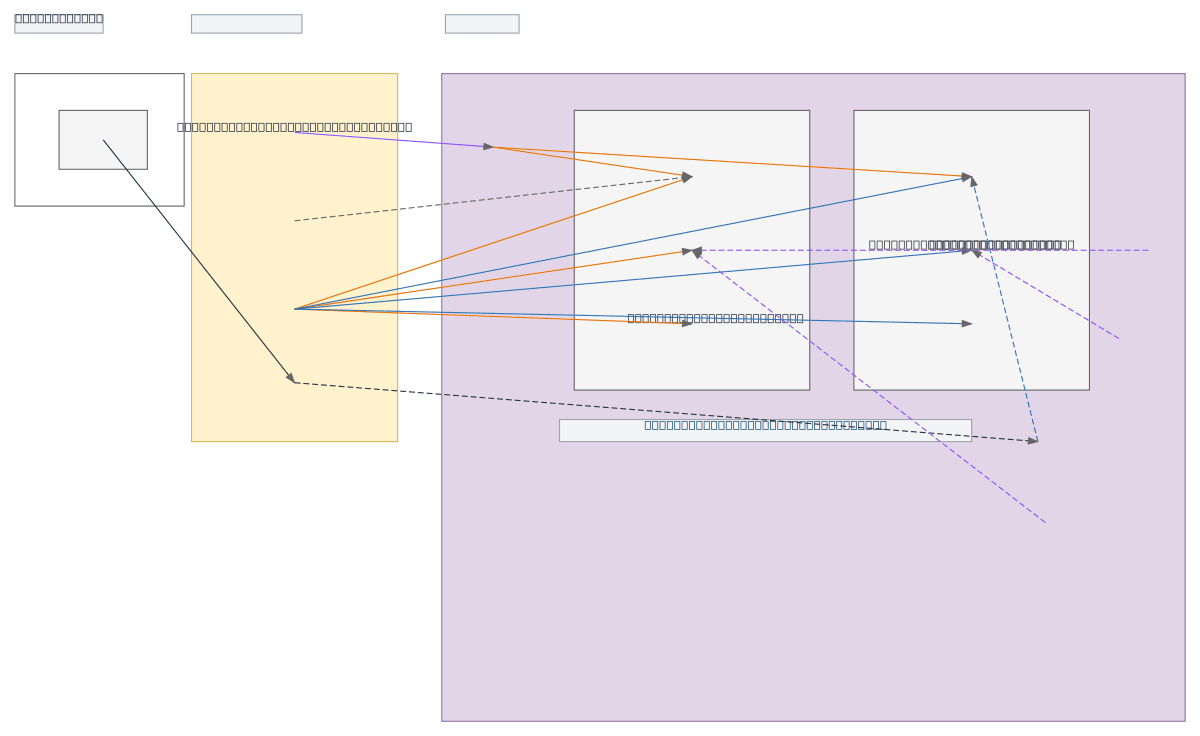
OpenShift 4.20.13 on vSphere - Network Diagram
About This Architecture
OpenShift 4.20.13 on vSphere with network segmentation across control plane and compute VLANs, load-balanced API/Ingress endpoints, and DMZ-isolated auxiliary services. Traffic flows from Red Hat Registry through a firewall to an OCI-hosted internal registry, with DNS/DHCP/NTP services supporting three master nodes and three worker nodes orchestrated by vCenter. This architecture demonstrates enterprise-grade network isolation, high availability via load balancing, and secure image distribution for production Kubernetes workloads. Fork and customize this diagram to match your vSphere cluster topology, VLAN assignments, and registry endpoints. The bootstrap node pattern ensures repeatable, automated cluster initialization across your infrastructure.
People also ask
How do you design a production OpenShift 4.20.13 network on vSphere with proper VLAN segmentation and load balancing?
This diagram shows OpenShift 4.20.13 deployed across vSphere with three master nodes in a control plane VLAN and three worker nodes in a compute VLAN, both behind a load balancer handling API and Ingress traffic. Network isolation is enforced via firewall rules, auxiliary services run in a DMZ, and container images are pulled from an OCI-hosted internal registry, ensuring secure, scalable Kubernet
- Domain:
- Kubernetes
- Audience:
- OpenShift platform engineers deploying Red Hat OpenShift 4.20.13 on vSphere infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.