NatWest AWS ECS Fargate Banking Architecture
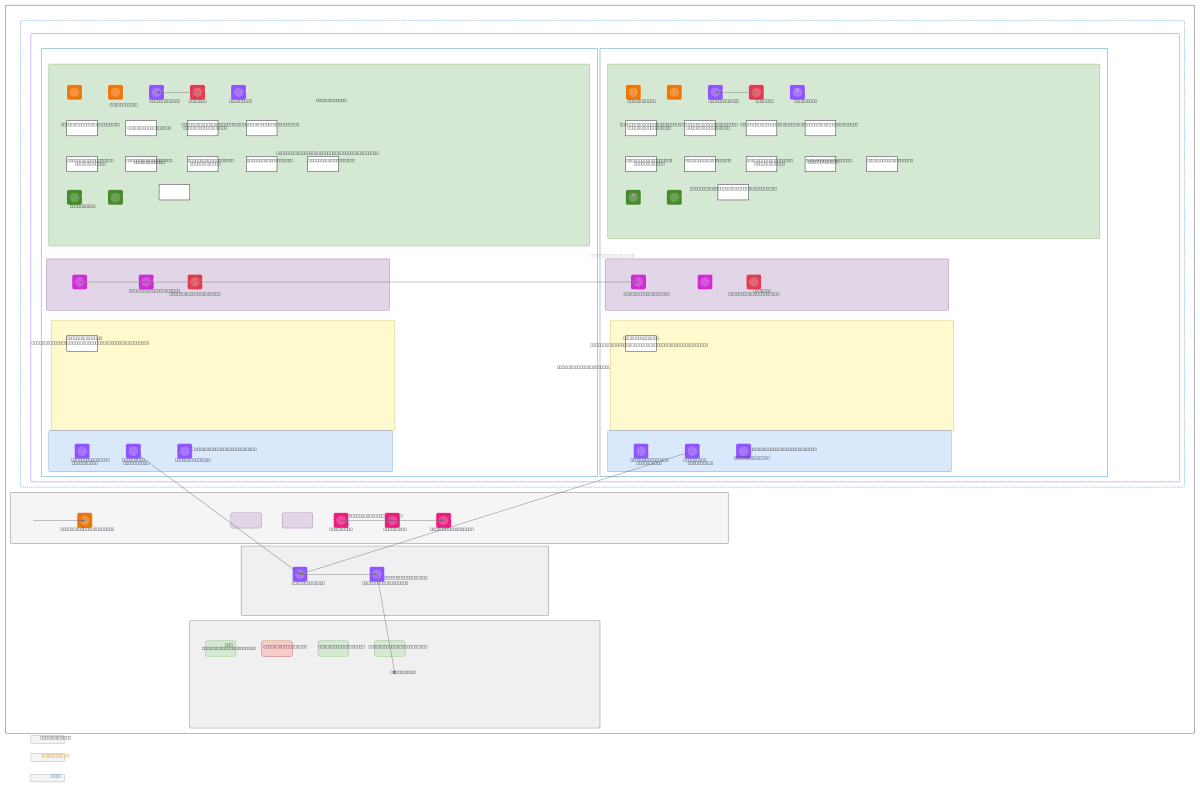
About This Architecture
Multi-AZ ECS Fargate architecture spanning eu-west-2 with dual availability zones, blending On-Demand and Spot instances across high-resource and standard services. Traffic flows through API Gateway and Route 53 to an Internal ALB protected by AWS WAF, routing to five target groups via Cloud Map service discovery. Data persists in Aurora PostgreSQL Serverless v2 with primary-secondary replication, EBS, and EFS, while secrets, encryption keys, and audit trails are centrally managed via Secrets Manager, KMS, and CloudTrail. VPC endpoints for ECR, SQS, SNS, CloudWatch Logs, and Systems Manager ensure private, secure service access without internet exposure. Fork this diagram to customize subnets, scaling policies, or add Transit Gateway and Cloud WAN attachments for hybrid banking workloads.
People also ask
How do I design a secure, multi-AZ ECS Fargate architecture for banking workloads with private VPC endpoints and Aurora PostgreSQL?
This diagram shows a banking-grade ECS Fargate setup spanning two availability zones in eu-west-2, using On-Demand instances for critical services and Spot for standard workloads to optimize costs. Aurora PostgreSQL Serverless v2 handles data with primary-secondary replication, while VPC endpoints for ECR, SQS, SNS, and CloudWatch Logs keep traffic private. AWS WAF protects the Internal ALB, KMS e
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing multi-AZ banking infrastructure on ECS Fargate
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.