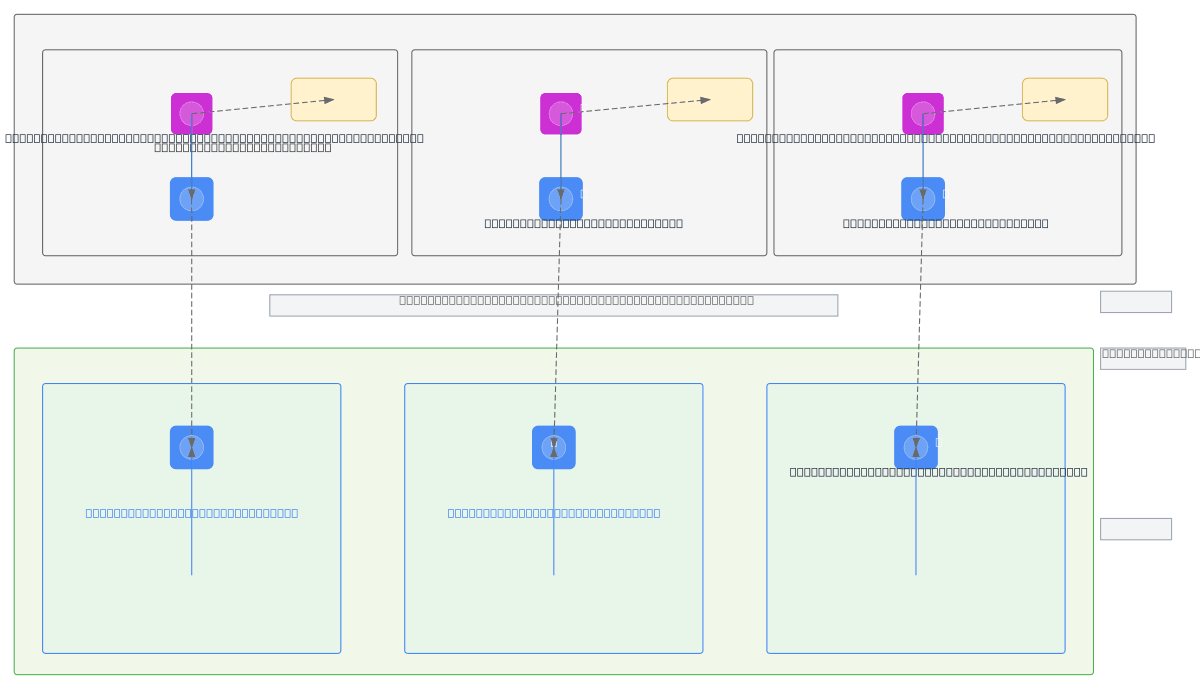
MongoDB Atlas PSC to GCP - Quanta Exchange
About This Architecture
Multi-environment MongoDB Atlas to GKE connectivity using GCP Private Service Connect (PSC) isolates database traffic across dev, UAT, and production workloads. Three MongoDB Atlas M10 replica set clusters in us-central1 expose PSC Service Attachments that route through PSC Forwarding Rules and Endpoints into isolated GCP Runtime VPCs (quantax-dev-vpc, quantax-uat-vpc, quantax-prod-vpc), eliminating public internet exposure. GKE clusters running EP3 workloads consume these private endpoints at fixed IPs (10.10.1.5, 10.20.1.5, 10.30.1.5) for secure, low-latency database access. This architecture enforces network segmentation and least-privilege access while maintaining Atlas-managed infrastructure, reducing operational overhead and blast radius per environment. Fork this diagram on Diagrams.so to customize VPC CIDR ranges, add firewall rules, or extend to additional regions and clusters.
People also ask
How do I securely connect MongoDB Atlas to GKE clusters in GCP without exposing databases to the public internet?
Use GCP Private Service Connect (PSC) to create private endpoints from MongoDB Atlas Service Attachments into isolated GCP Runtime VPCs. Each environment (dev, UAT, prod) gets its own PSC Forwarding Rule and fixed endpoint IP, allowing GKE clusters to reach MongoDB Atlas M10 replica sets over private, low-latency connections while maintaining network segmentation and Atlas-managed infrastructure.
- Domain:
- Cloud Gcp
- Audience:
- GCP cloud architects designing private connectivity between MongoDB Atlas and GKE clusters
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.