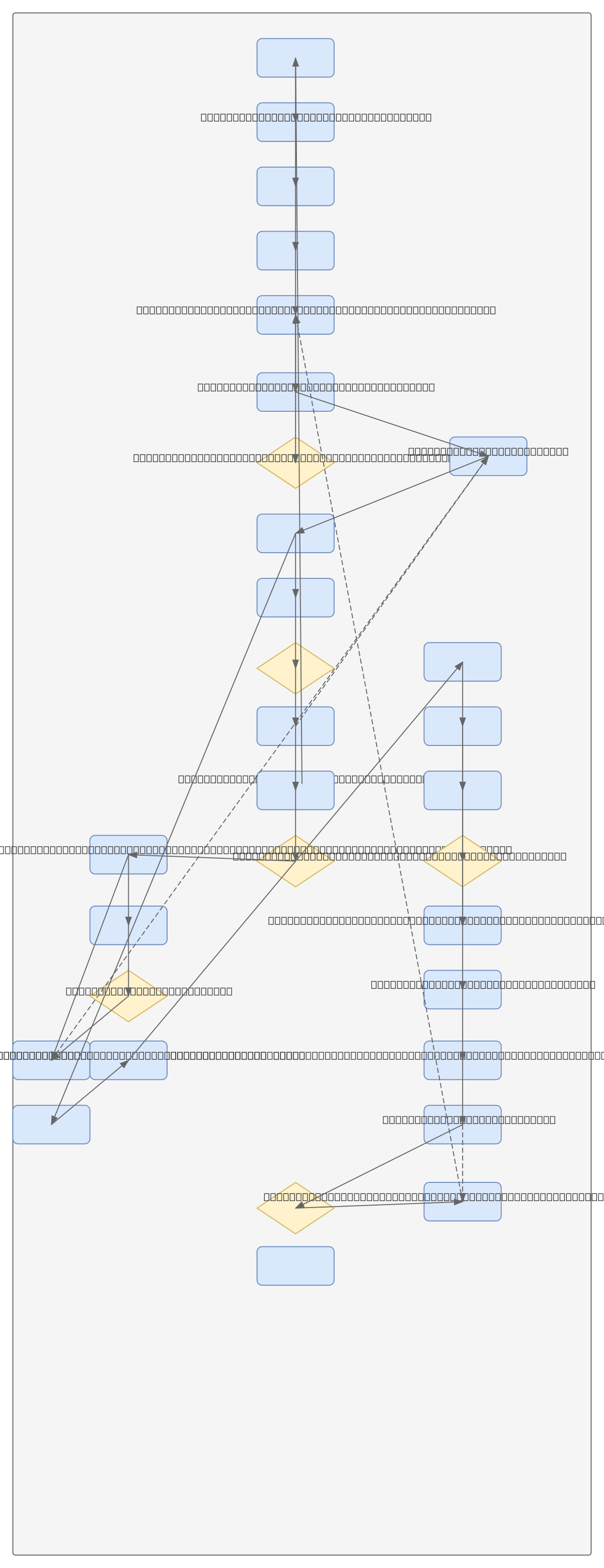
Local IDS - Raspberry Pi Activity Flow
About This Architecture
Local IDS on Raspberry Pi uses a six-phase activity flow to detect network anomalies in real time without cloud dependencies. Live traffic capture via tcpdump feeds rotating 5MB .pcap chunks into concurrent file scanning, packet grouping by device ID, and sliding-window feature engineering that computes conn_count, bytes_sum, pkt_count, and avg_pkt_size. A quantized TFLite model runs inference on extracted features, generating anomaly scores that trigger JSON alerts logged with TimedRotatingFileHandler for midnight archival. This architecture demonstrates edge-based threat detection with minimal RAM footprint, race-condition safety, and autonomous operation ideal for IoT gateways and network monitoring appliances.
People also ask
How do you build a real-time intrusion detection system on a Raspberry Pi with minimal latency and memory overhead?
This diagram shows a six-phase IDS pipeline: tcpdump captures live traffic into rotating 5MB .pcap chunks, Scapy reads completed files and groups packets by device ID, a sliding-window feature extractor computes network metrics (conn_count, bytes_sum, pkt_count, avg_pkt_size), and a quantized TFLite model detects anomalies. JSON alerts are logged with automatic midnight rotation, enabling autonomo
- Domain:
- Security
- Audience:
- embedded systems security engineers deploying intrusion detection on resource-constrained devices
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.