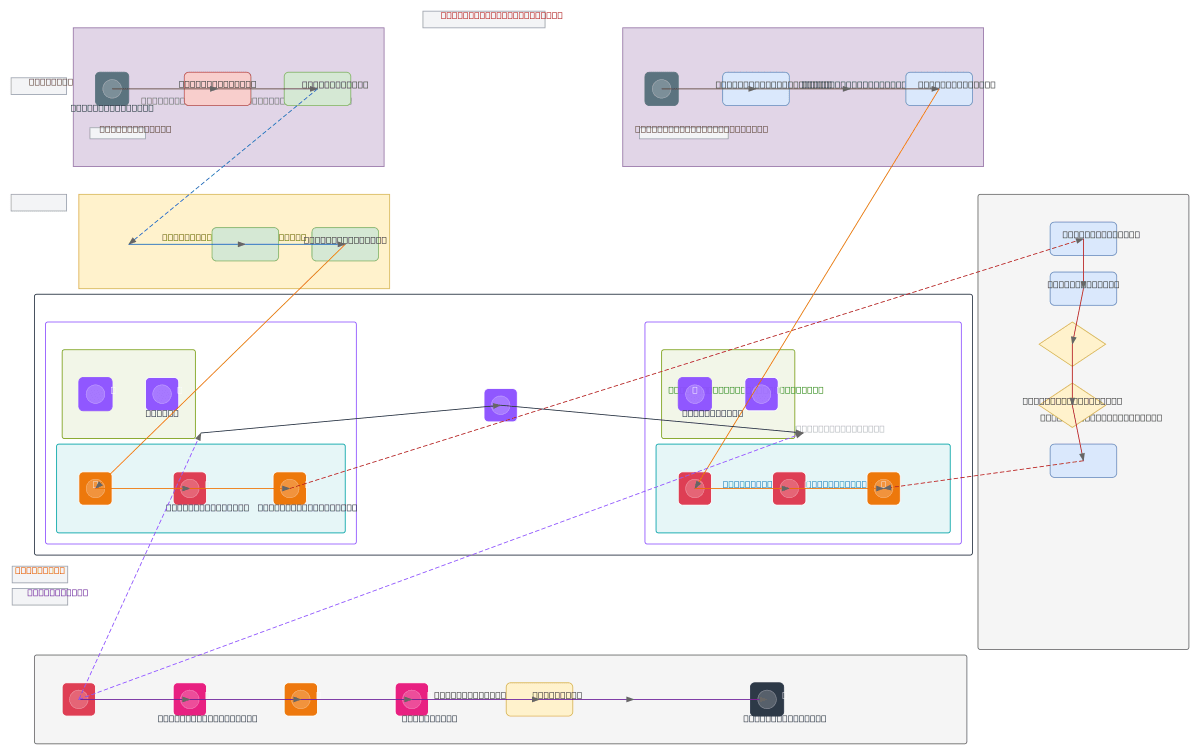
Korean Fintech Dual CI/CD Pipeline - AWS Seoul
About This Architecture
Dual CI/CD pipeline architecture for Korean fintech workloads spanning on-premise and AWS Seoul (ap-northeast-2), enforcing five-stage promotion gates with code review, SAST scanning, security approval, and 4-eyes sign-off before production deployment. Dev and Prod VPCs (10.10.0.0/16 and 10.20.0.0/16) connect via Transit Gateway, with Dev workstations accessing GitHub SaaS through VPN and Ops teams using Amazon Workspaces to trigger GitHub Enterprise Server builds. AWS CodeBuild, CodePipeline, Inspector, and GuardDuty provide automated security scanning and compliance enforcement, while an alarm chain integrates GuardDuty findings through EventBridge, Lambda, SNS, PagerDuty, and Slack for 24/7 incident response. This architecture demonstrates defense-in-depth for financial services: network segmentation (VLAN 10/20), identity federation (OIDC), least-privilege CI runners, and real-time threat detection. Fork and customize this diagram on Diagrams.so to adapt promotion gates, add additional approval workflows, or integrate with your own incident management tools.
People also ask
How do I build a compliant CI/CD pipeline for fintech on AWS Seoul with on-premise integration and automated security gates?
This diagram shows a dual-pipeline architecture using AWS CodePipeline with five mandatory stages: code review, SAST via SonarQube, security approval, 4-eyes sign-off, and production build. On-premise Dev and Ops teams connect via VPN and Amazon Workspaces to GitHub Enterprise, while AWS GuardDuty continuously monitors both Dev and Prod VPCs, routing findings through EventBridge and Lambda to Page
- Domain:
- Devops Cicd
- Audience:
- DevOps engineers and platform architects implementing regulated CI/CD pipelines in AWS Seoul region with on-premise hybr
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.