IoT TinyML IDS with Federated Learning and
About This Architecture
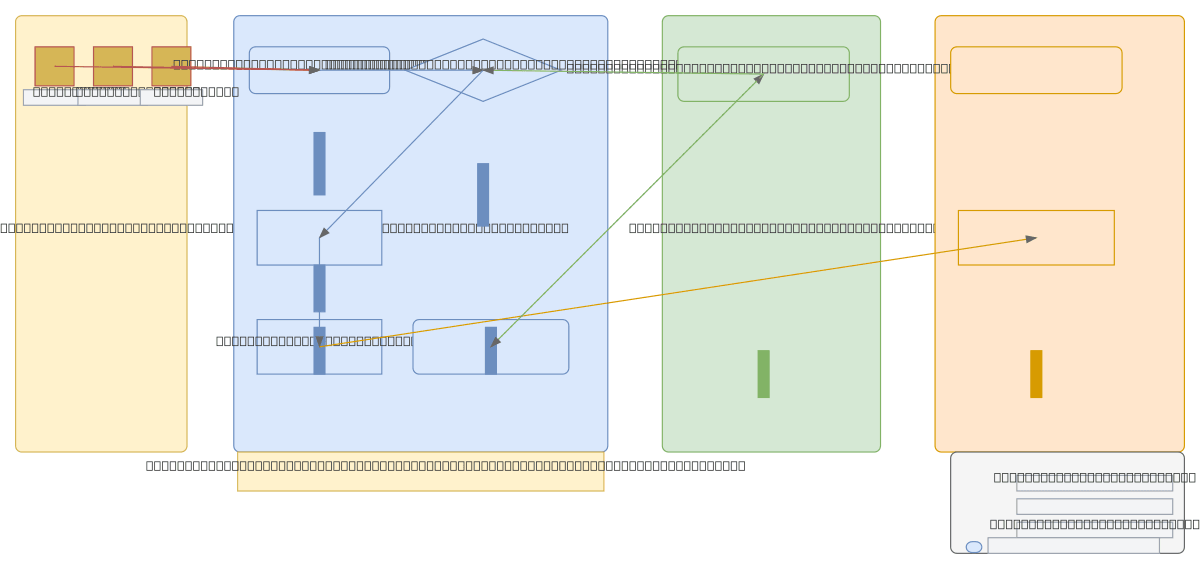
Privacy-preserving IoT intrusion detection system combining TinyML inference on edge devices with federated learning and blockchain tamper-evidence. Raw sensor data from smart cameras, thermostats, and sensor nodes flows through feature extraction and TensorFlow Lite quantized models on a Raspberry Pi 4 gateway, generating local alerts logged to JSON. Flower federated learning framework trains model weights across distributed edge nodes without centralizing raw data, while Merkle tree hashing and Ethereum smart contracts anchor detection logs to an immutable ledger. This architecture demonstrates zero-trust IoT security: raw data never leaves the edge, only model weights and cryptographic proofs traverse the cloud and blockchain layers. Fork and customize this diagram on Diagrams.so to adapt threat models, add additional sensor types, or integrate with AWS IoT Core and SageMaker for production deployments.
People also ask
How can I build a privacy-preserving intrusion detection system for IoT devices that keeps raw data on the edge while using federated learning?
This diagram shows a complete IoT IDS architecture where raw sensor data stays on Raspberry Pi gateways running TensorFlow Lite models, while only model weights are shared via Flower federated learning and detection logs are anchored to Ethereum via Merkle trees. This approach eliminates centralized data collection, satisfies privacy regulations, and enables collaborative threat detection across d
- Domain:
- Ml Pipeline
- Audience:
- IoT security architects and ML engineers building privacy-preserving intrusion detection systems
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.