IoT Secure Hybrid RNG Architecture
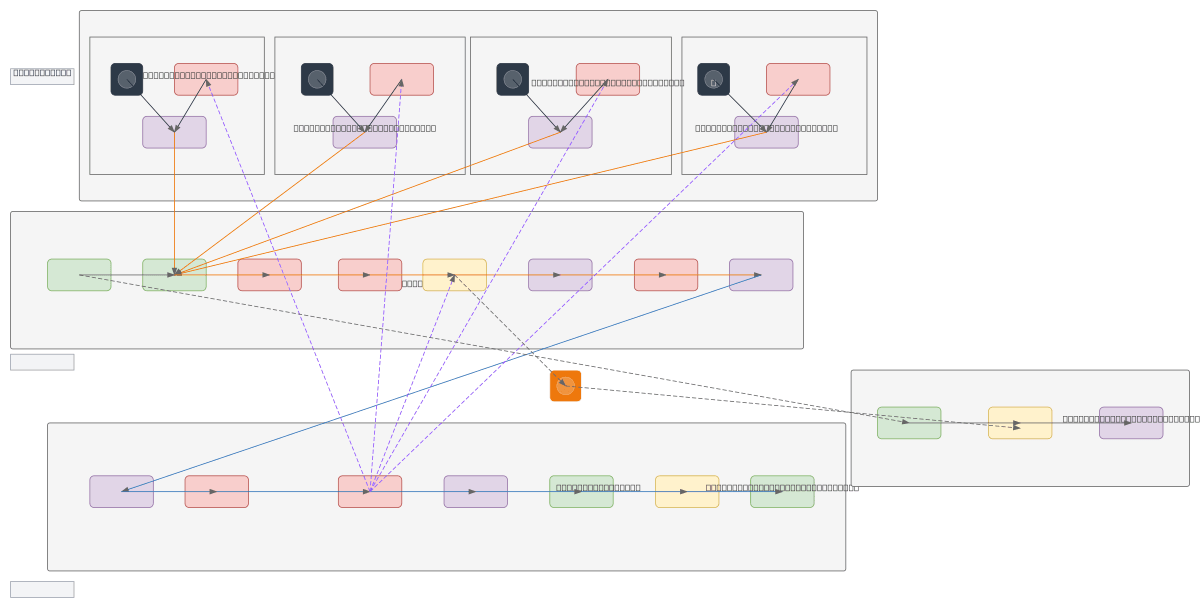
About This Architecture
Hybrid RNG architecture combining device-level entropy sources (ADC noise, ring oscillators, power jitter, thermal noise) with PRNG and SHA-256 hashing across IoT, edge, and cloud tiers. Multiple sensor devices, industrial controllers, and smart meters feed entropy into distributed Hybrid RNG instances that communicate via TLS/MQTT to an Edge Gateway with aggregated entropy pooling and mTLS authentication. Edge Firewall, RNG Aggregator, and Edge API Gateway enforce defense-in-depth before data reaches Cloud API Gateway, Cloud Auth/IAM, and Centralized KMS for secure key distribution and audit logging. Fork this diagram to customize entropy source types, adjust TLS cipher suites, or integrate with your KMS provider.
People also ask
How do you design a secure IoT architecture that combines multiple entropy sources with hybrid RNG across device, edge, and cloud layers?
This diagram shows a three-tier approach: IoT devices (temperature sensors, controllers, smart meters) generate entropy via ADC noise, ring oscillators, power jitter, and thermal noise, each feeding Hybrid RNG instances using PRNG and SHA-256. Edge Gateway aggregates entropy through an RNG Aggregator, enforces mTLS authentication, and routes encrypted traffic via TLS/MQTT and VPN to Cloud KMS for
- Domain:
- Security
- Audience:
- Security architects designing IoT cryptographic infrastructure with hybrid entropy sources
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.