IoT OTA Simulation with Attack Injection and
About This Architecture
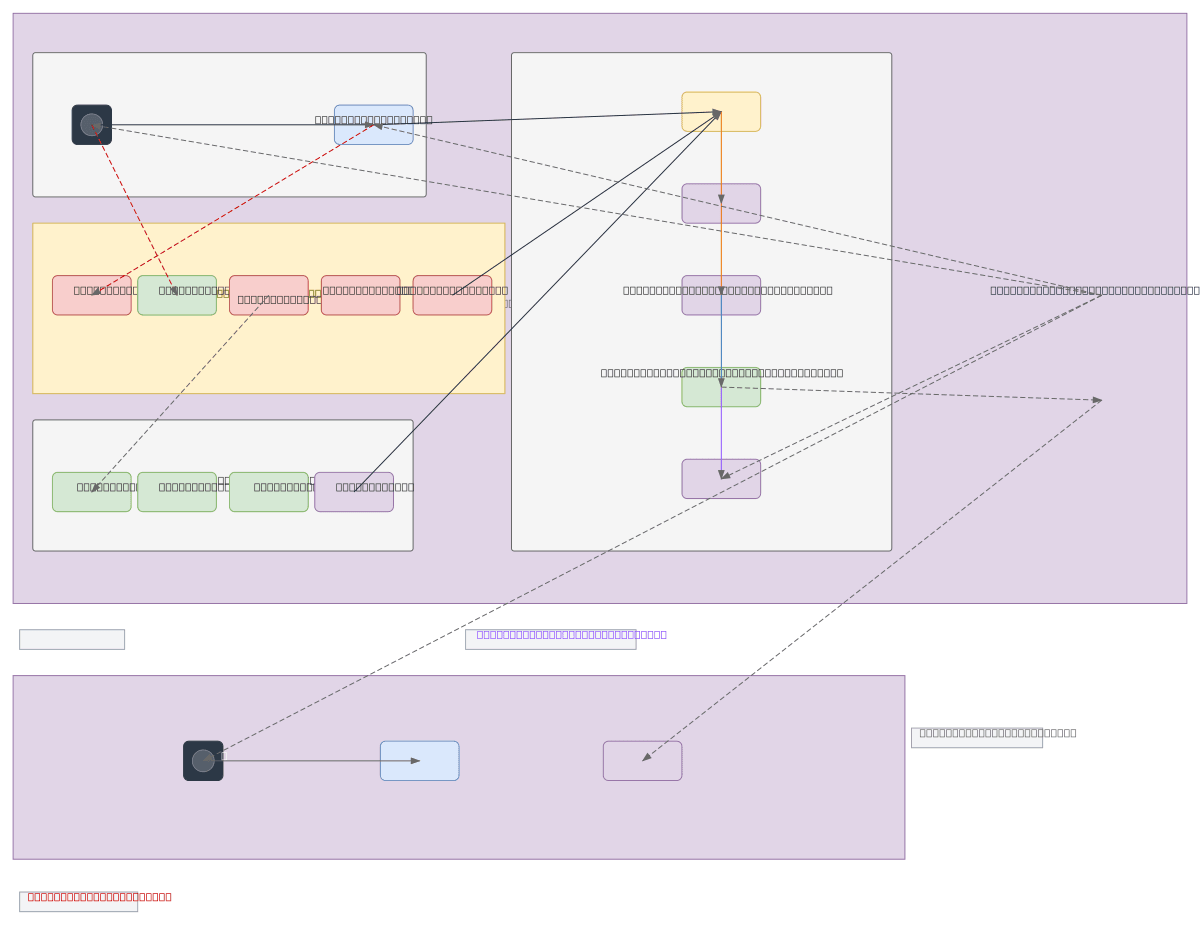
IoT OTA simulation with integrated attack injection and ML-based threat detection across four operational tiers. The architecture chains a Python IoT client and Flask OTA server through multiple attack vectors—DDoS via Scapy, reconnaissance via nmap, MITM via mitmproxy, and Python-based intrusion and backdoor payloads—while background traffic layers (ARP, ICMP, DNS, MQTT) provide realistic network noise. tshark captures loopback traffic, segments 120 sessions, extracts 38 features, and feeds a pre-trained XGBoost model to evaluate detection accuracy. This end-to-end pipeline demonstrates how to generate labeled security datasets and validate anomaly detection in IoT environments without risking production systems.
People also ask
How do I build a complete IoT intrusion detection system with attack simulation and machine learning evaluation?
This diagram shows a four-tier architecture: a simulation layer with Python IoT client and Flask OTA server, an attack injection layer deploying DDoS, reconnaissance, MITM, and backdoor payloads, a background traffic layer adding realistic network noise, and a capture-and-ML pipeline using tshark to record traffic, segment 120 sessions, extract 38 features, and evaluate a pre-trained XGBoost model
- Domain:
- Security
- Audience:
- security engineers and ML practitioners building IoT intrusion detection systems
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.