infrastructure
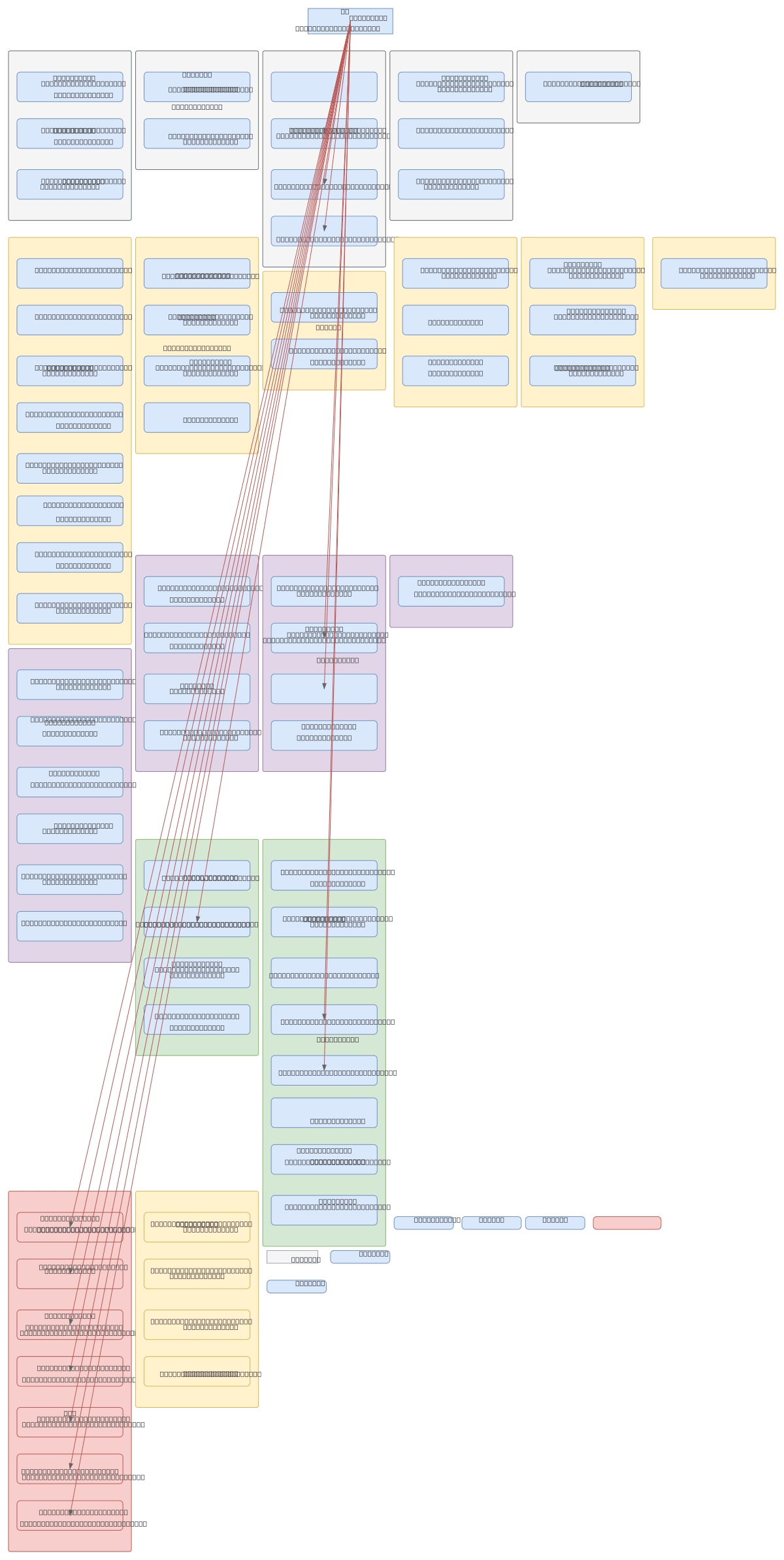
About This Architecture
Multi-tier hybrid infrastructure spanning Active Directory, file servers, application servers, and monitoring systems across segmented LANs and DMZ zones. Traffic flows from the Internet through DMZ-hosted management tools (OPMANAGERPLUSWIN, Monitoring, GLPI) to internal LAN segments (INFRA, PROD, TEST, LAN-iE, LAN-iPro, LAN-LocPro) where domain controllers, development servers, and business applications reside. This architecture demonstrates defense-in-depth with isolated backup domains, role-based server groupings (DSI-Supervision, DSI-Tests, DSI-Deploiement, DEV-iE, DEV-iPro, ADV, SUP-iE, SUP-iPro, CSL-iE, DEMOS-iE, DEMOS-iPro), and centralized monitoring via ManageEngine and GLPI. The design prioritizes network segmentation, backup isolation, and operational visibility across development, test, and production workloads. Fork this diagram on Diagrams.so to customize IP ranges, add firewall rules, or adapt for your organization's security policies.
People also ask
How should I design a hybrid on-premises network with Active Directory, DMZ, and segmented LANs for development, test, and production workloads?
This diagram shows a multi-segment hybrid infrastructure with domain controllers (SV-IR-DC01/02/03) in the INFRA LAN, DMZ-hosted management tools (OPMANAGERPLUSWIN, Monitoring, GLPI) for external access, and isolated LAN segments (PROD, TEST, LAN-iE, LAN-iPro) for application servers and development environments. Each segment maintains separate backup domains and role-based server groupings (DSI-S
- Domain:
- Networking
- Audience:
- Infrastructure architects and network administrators managing hybrid on-premises data center environments
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.