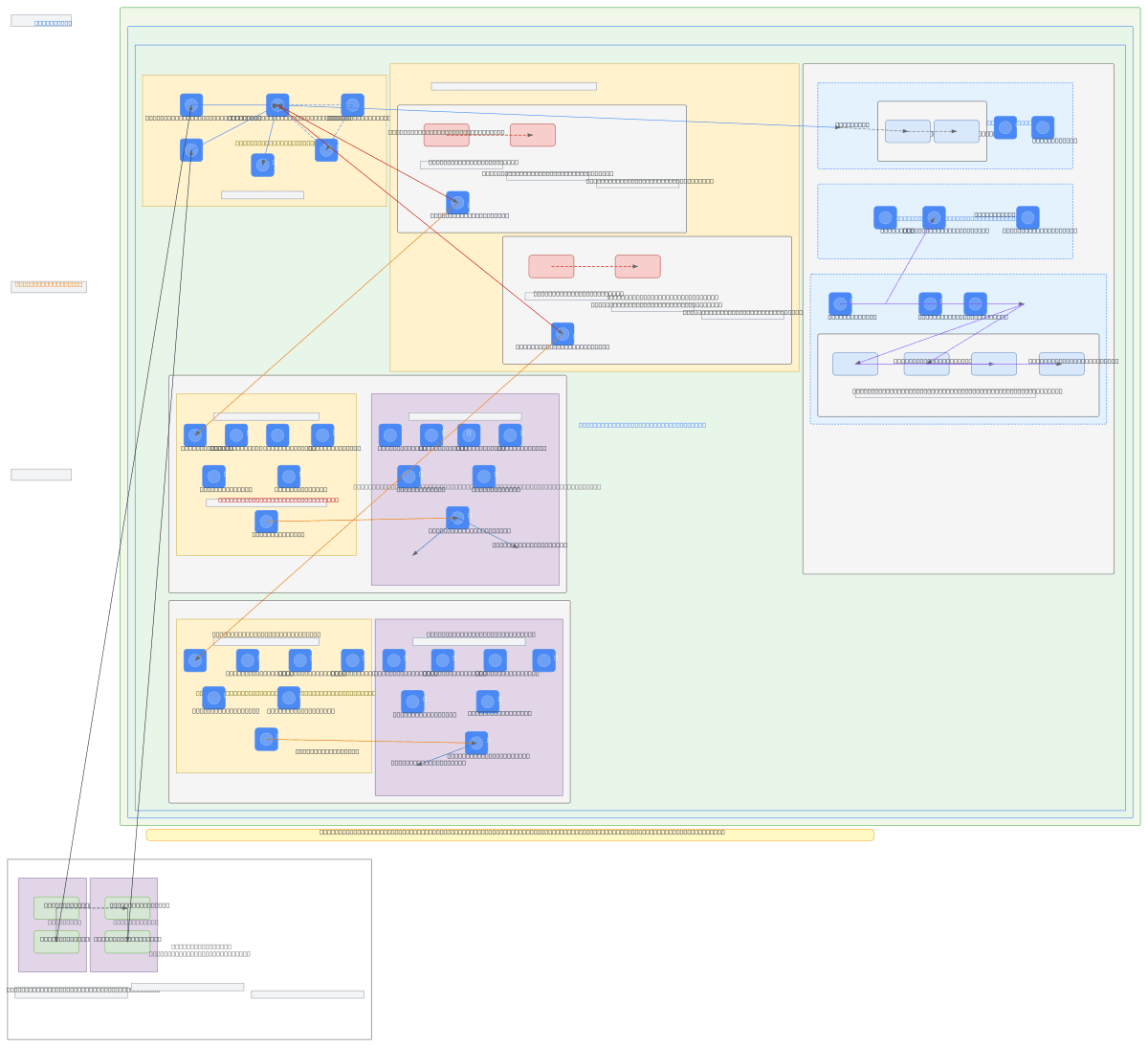
GCP Enterprise Hybrid Cloud Landing Zone LLD
About This Architecture
GCP Enterprise Hybrid Cloud Landing Zone with dual-region Dedicated Interconnect from Madrid and Barcelona on-premises datacenters, featuring Network Connectivity Center hub-and-spoke topology with HA VPN overlay and BGP dynamic routing. Traffic from six production and non-production DMZ and mid-tier Shared VPCs flows through active-active Palo Alto VM-Series firewall pairs in a dedicated Security Inspection Zone, with Cloud Armor WAF and Cloud CDN protecting external ingress. Shared Services Zone provides centralized DNS (Cloud DNS + Infoblox active-active), Cloud NAT, Cloud IAM, Cloud KMS, and Security Command Center for compliance and observability across the 10.0.0.0/8 enterprise network. This architecture demonstrates Google Cloud best practices for zero-trust security, multi-region resilience, and least-privilege access in regulated environments. Fork this diagram on Diagrams.so to customize VPC CIDR ranges, add additional regions, or integrate with your existing Terraform modules and GitOps workflows.
People also ask
How do I design a GCP landing zone that securely connects on-premises datacenters with production and non-production workloads using Dedicated Interconnect and centralized firewall inspection?
This diagram shows a production-grade GCP landing zone with Madrid and Barcelona on-premises datacenters connected via Dedicated Interconnect and HA VPN overlay to a Network Connectivity Center hub in europe-southwest1. All traffic from six production and non-production DMZ and mid-tier Shared VPCs flows through active-active Palo Alto VM-Series firewall pairs in a Security Inspection Zone, enforc
- Domain:
- Cloud Multi
- Audience:
- GCP enterprise architects designing hybrid cloud landing zones with on-premises connectivity
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.