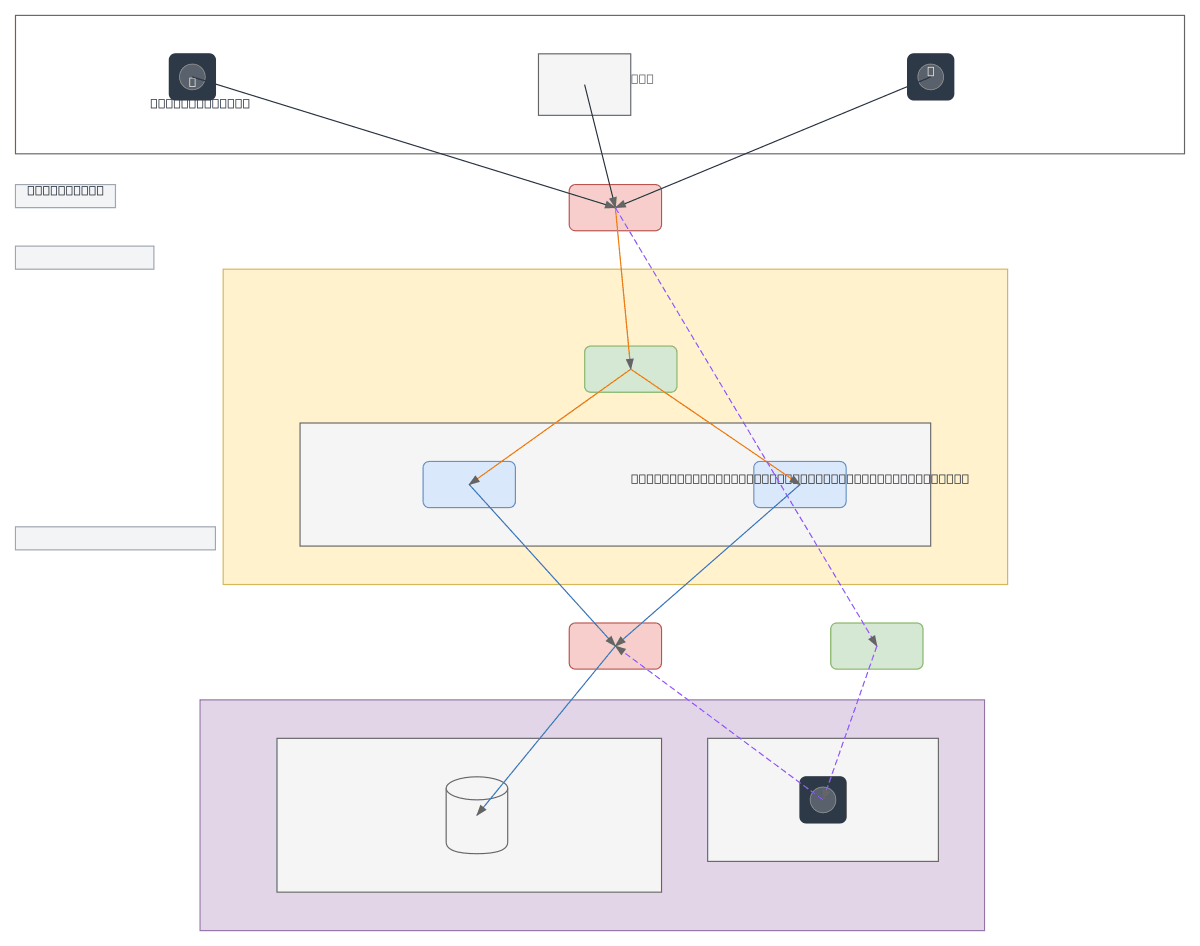
FurLink Web Application Network Architecture
About This Architecture
FurLink's three-tier network architecture separates public-facing web services from sensitive backend databases using perimeter and internal firewalls across distinct VLANs. Internet traffic from foster carers and general users flows through a perimeter firewall to a load balancer, which distributes requests across two redundant FurLink PHP application servers in the DMZ (VLAN 10). Backend database access is isolated in VLAN 20, reachable only through an internal firewall, with a dedicated VPN gateway (VLAN 30) for secure administrative access. This design enforces defense-in-depth by segmenting trust boundaries, limiting lateral movement, and protecting the MySQL database from direct internet exposure. Fork this diagram on Diagrams.so to customize IP ranges, add additional tiers, or adapt the firewall rules for your organization's security policies. The architecture demonstrates best practices for healthcare or social-service applications handling sensitive user data.
People also ask
How should I design a secure network architecture for a web application that separates public users from sensitive backend databases?
FurLink's architecture uses a perimeter firewall to protect the DMZ (VLAN 10) containing load-balanced web servers, an internal firewall to isolate the database tier (VLAN 20), and a VPN gateway (VLAN 30) for administrative access. This multi-layer approach enforces least-privilege access and prevents direct internet exposure to databases.
- Domain:
- Networking
- Audience:
- Network architects designing secure multi-tier web application infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.