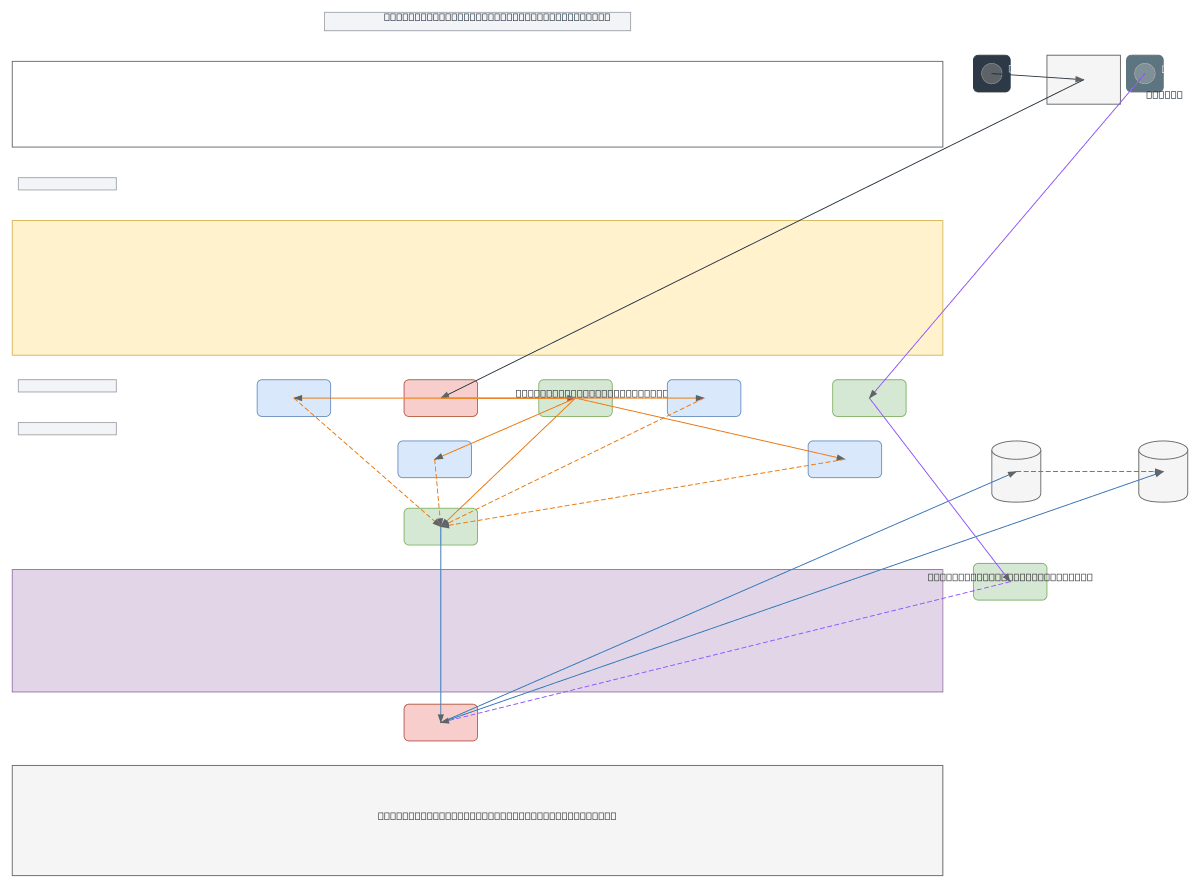
FurLink Web Application Network Architecture
About This Architecture
FurLink's three-tier network architecture separates public-facing web services from protected backend databases using DMZ and internal firewall segmentation across VLAN 10, VLAN 20, and VLAN 99. Public users connect via HTTPS through a perimeter firewall to a load balancer distributing traffic across four PHP application servers, which route database queries through an internal firewall to primary and replica MySQL servers. The design implements defense-in-depth with dual firewalls, VPN-gated management access, and clear network boundaries that enforce least-privilege communication between tiers. Fork this diagram on Diagrams.so to customize IP ranges, add additional VLANs, or adapt the topology for your organization's security and availability requirements. This architecture exemplifies the three-tier DMZ pattern commonly used in regulated environments requiring strict network segmentation and audit trails.
People also ask
How do you design a secure three-tier network architecture with firewall segmentation and database replication?
This diagram shows a proven three-tier DMZ pattern: a perimeter firewall protects the public web tier (VLAN 10) with a load balancer distributing traffic to four PHP servers, an internal firewall isolates the backend tier (VLAN 20) with primary and replica MySQL databases, and a separate management VLAN (VLAN 99) with VPN gateway controls admin access. This design enforces least-privilege communic
- Domain:
- Networking
- Audience:
- Network architects designing secure multi-tier web application infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.