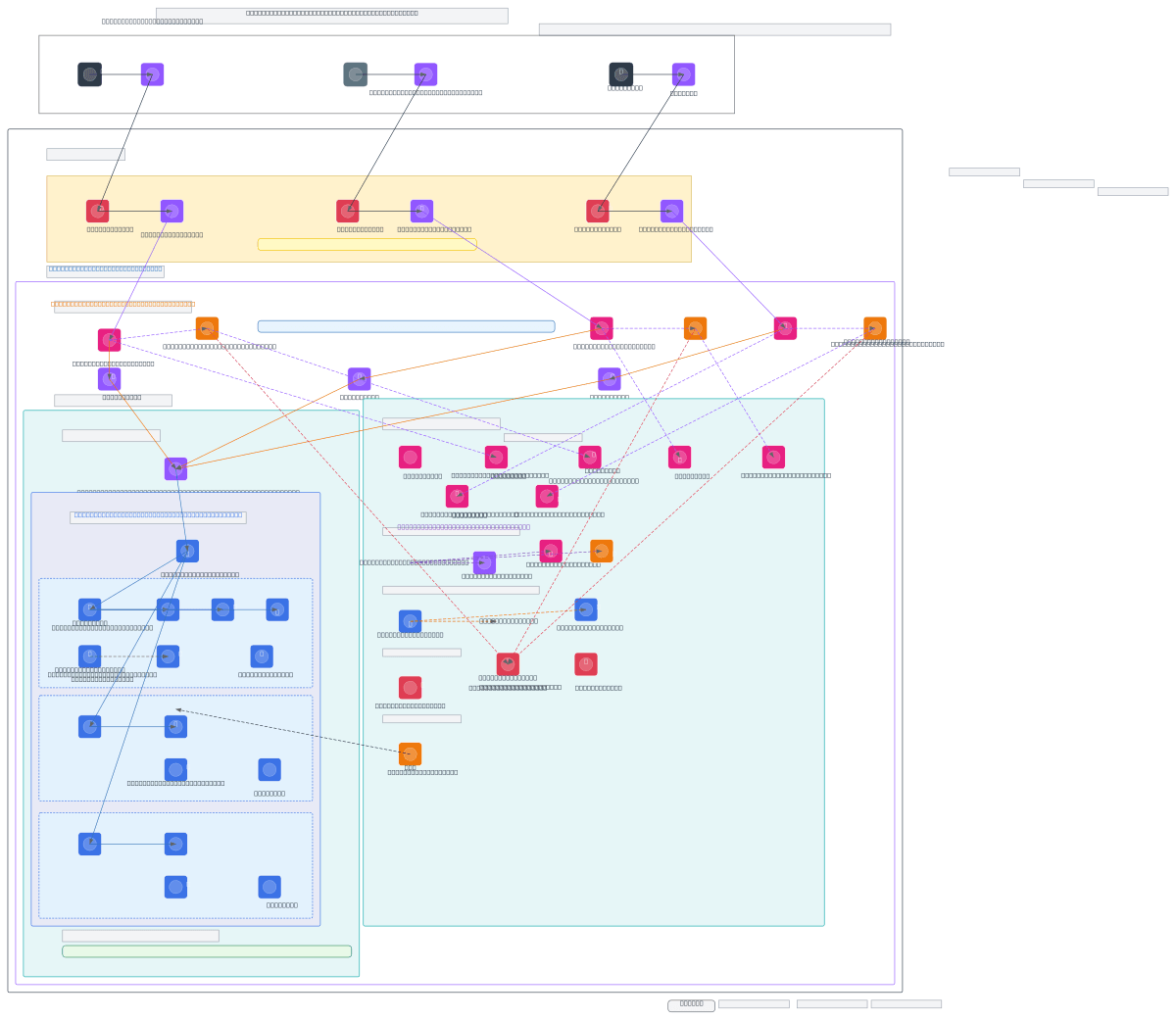
Featbank Multi-Pipeline AWS EKS Platform - DEV
About This Architecture
Featbank's multi-pipeline AWS EKS platform demonstrates a production-grade DEV environment architecture spanning CloudFront edge protection, API Gateway authorization, and Kubernetes Gateway API routing across three isolated pipelines. Traffic flows from Route53 through CloudFront + WAF edge layers, where X-CloudFront-Secret headers are injected, then validated by Lambda Authorizers before VPC Link integration routes requests to a shared ALB and EKS cluster. Three independent pipelines—API microservices (ms-auth, ms-core, ms-audit), ArgoCD GitOps, and SigNoz observability—run in separate Kubernetes namespaces with HTTPRoute-based hostname routing and ClusterIP service discovery. This architecture demonstrates defense-in-depth security (CloudFront headers, Lambda validation, ALB routing), infrastructure-as-code via Terraform modules, and centralized monitoring through CloudWatch Logs and Metrics. Fork and customize this diagram on Diagrams.so to adapt the multi-pipeline pattern for your own EKS deployments, adjust CIDR ranges, or add additional observability layers.
People also ask
How do you design a multi-pipeline AWS EKS architecture with CloudFront edge protection, API Gateway authorization, and Kubernetes Gateway API routing?
This diagram shows a three-tier security model: CloudFront + WAF inject X-CloudFront-Secret headers at the edge, Lambda Authorizers validate them at the API Gateway layer, and Kubernetes Gateway API HTTPRoutes route by hostname to isolated namespaces (API microservices, ArgoCD, SigNoz). VPC Links provide private integration between API Gateway and the shared ALB, eliminating internet exposure whil
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing multi-pipeline EKS platforms with GitOps and observability
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.