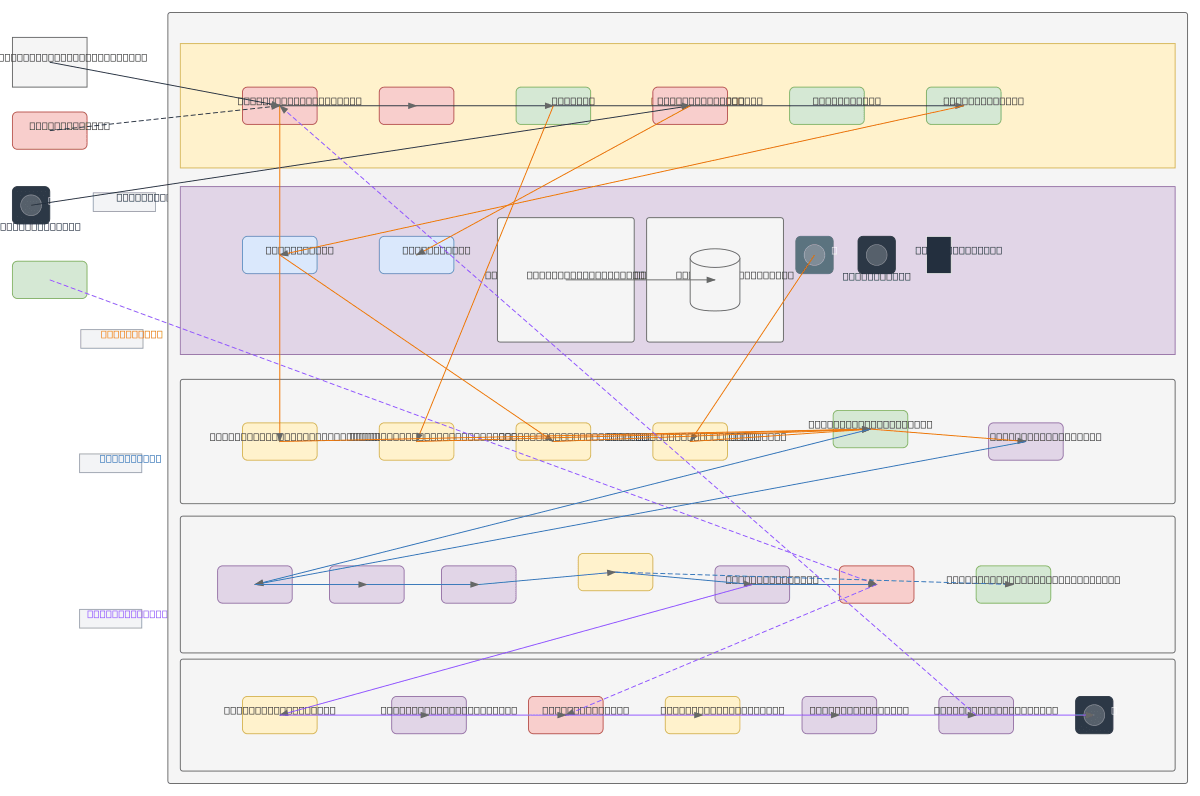
Enterprise SOC Architecture - Full Stack
About This Architecture
Enterprise SOC architecture integrating perimeter defense, centralized log collection, and SIEM processing into a full-stack security operations platform. Traffic from external users and threat actors flows through Firewall, WAF, and IDS/IPS before reaching internal assets, while logs from all security layers feed into a Log Server, Event Bus, and multi-stage SIEM pipeline including Parsing, Normalization, and Correlation engines. The SIEM Core generates alerts routed to SOC Console/SOAR for Incident Investigation and Threat Hunting, with results feeding Monitoring Dashboard, Reporting Engine, and Response Playbooks executed by SOC Analysts. This architecture demonstrates defense-in-depth with centralized visibility, enabling rapid threat detection and coordinated incident response across the enterprise.
People also ask
What does a complete enterprise SOC architecture look like from perimeter defense to incident response?
This diagram shows a multi-layered SOC architecture where external traffic passes through Firewall, WAF, and IDS/IPS before reaching internal assets. Logs from all security layers flow to a central Log Server, then through a SIEM pipeline with Parsing, Normalization, and Correlation engines that feed the SIEM Core and Alert Generator. Alerts route to SOC Console/SOAR for Incident Investigation and
- Domain:
- Security
- Audience:
- Security architects and SOC directors designing enterprise threat detection and response infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.