Enterprise Network Security Architecture
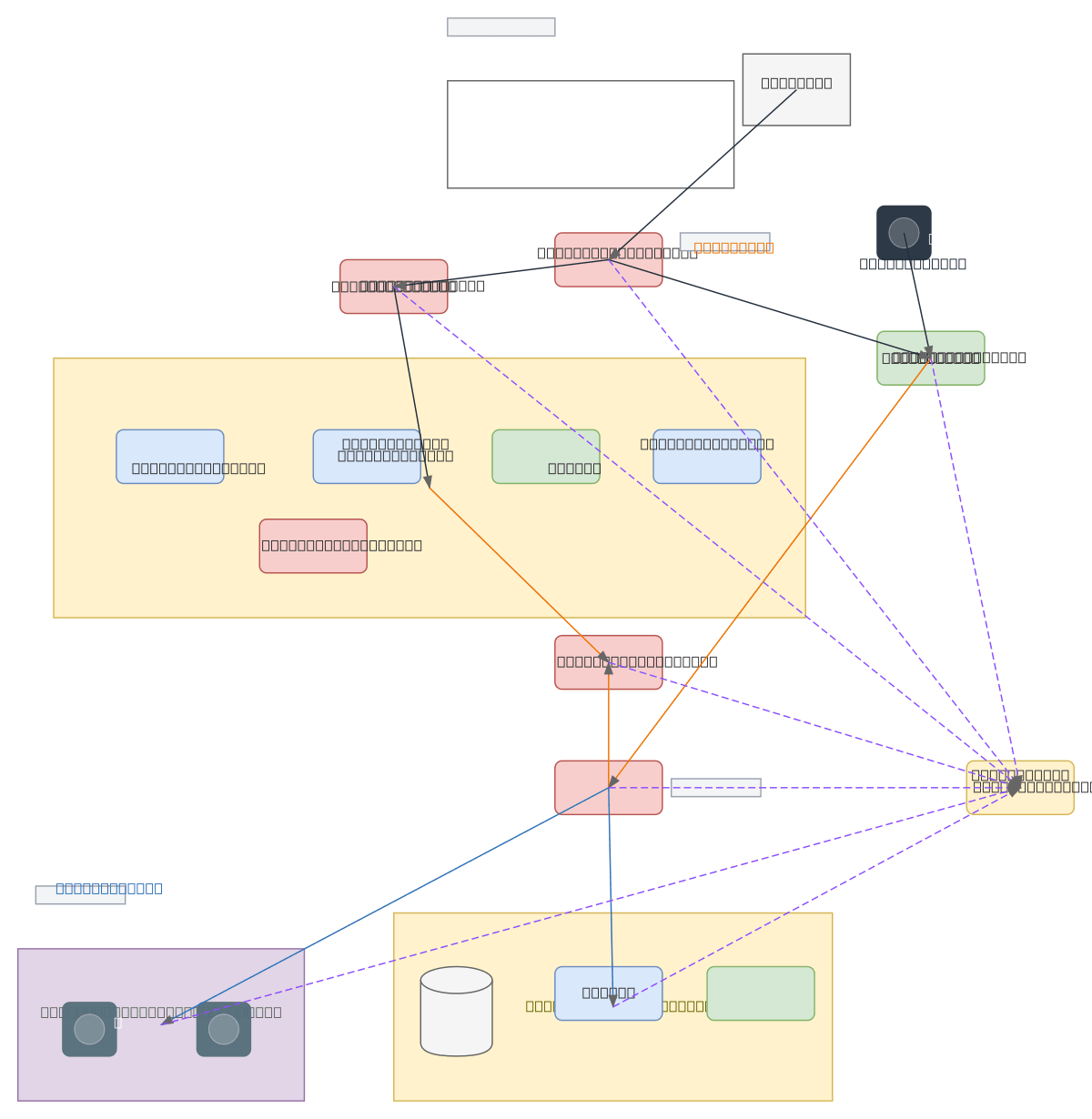
About This Architecture
Enterprise network security architecture with perimeter firewall, DMZ segmentation, and dual IDS/IPS sensors monitoring internet-to-DMZ and lateral movement traffic. Traffic flows from Internet through Perimeter Firewall and IDS/IPS Sensor (Internet-DMZ) into the DMZ hosting Web Server, Email Server, DNS/Proxy Server, and Public Services Server, while Remote Users connect via VPN Gateway to Internal Firewall. Internal network splits into User LAN (VLAN 10) with workstations and Secure Server Network (VLAN 20) containing Database Server, Financial Systems Server, and File Server, with IDS/IPS Sensor (Lateral Movement) monitoring inter-zone traffic. This multi-layered approach with centralized SIEM System log aggregation enforces defense-in-depth, preventing lateral movement and detecting threats at multiple checkpoints. Security architects can fork this diagram to customize firewall rules, add additional VLANs, or integrate with specific SIEM platforms like Splunk or ELK Stack.
People also ask
How should I design an enterprise network security architecture with DMZ segmentation and threat detection?
This diagram shows a defense-in-depth architecture using perimeter firewall, DMZ isolation, dual IDS/IPS sensors (Internet-DMZ and Lateral Movement), VLAN segmentation (User LAN VLAN 10 and Secure Server Network VLAN 20), VPN gateway for remote access, and centralized SIEM log aggregation. All traffic flows through firewalls and sensors before reaching internal networks, preventing lateral movemen
- Domain:
- Security
- Audience:
- Security architects designing zero-trust enterprise networks
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.