Enterprise IAM - Directory to Application Access
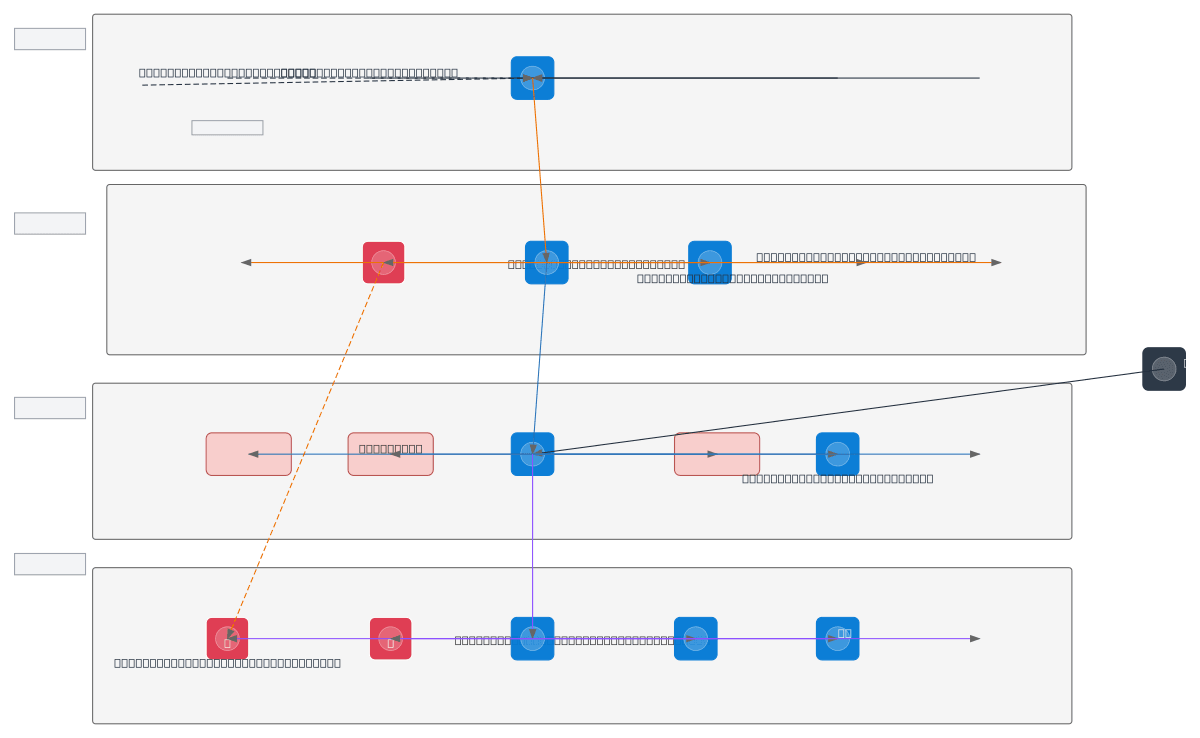
About This Architecture
Enterprise IAM architecture integrating Microsoft Entra ID with on-premises Active Directory servers, AD Connect Health, and Azure AD Domain Services for unified identity management. Identity flows from Directory Services through IDM Core Engine, which orchestrates user provisioning, roles management, demand workflows, and device asset tracking before reaching the Authentication Layer. SSO Solution enforces SAML 2.0, OAuth 2.0, OpenID Connect, MFA, and Conditional Access policies, routing authenticated users through a Policy Engine that applies RBAC and ABAC rules to Enterprise Applications and SaaS platforms. This architecture demonstrates hybrid identity governance, reducing access provisioning delays and enforcing least-privilege across on-premises and cloud workloads. Fork and customize this diagram on Diagrams.so to model your organization's directory topology, add custom policy engines, or extend to multi-cloud scenarios.
People also ask
How do I design an enterprise IAM architecture that integrates on-premises Active Directory with cloud identity management and enforces role-based and attribute-based access control?
This diagram shows a complete enterprise IAM flow: on-premises Active Directory servers sync to Microsoft Entra ID via AD Connect Health and Azure AD Domain Services. The IDM Core Engine manages user provisioning, roles, and device assets, feeding into an SSO Solution that enforces SAML 2.0, OAuth 2.0, OpenID Connect, MFA, and Conditional Access. A Policy Engine applies RBAC and ABAC rules before
- Domain:
- Iam
- Audience:
- Enterprise identity architects designing zero-trust directory and access governance solutions
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.