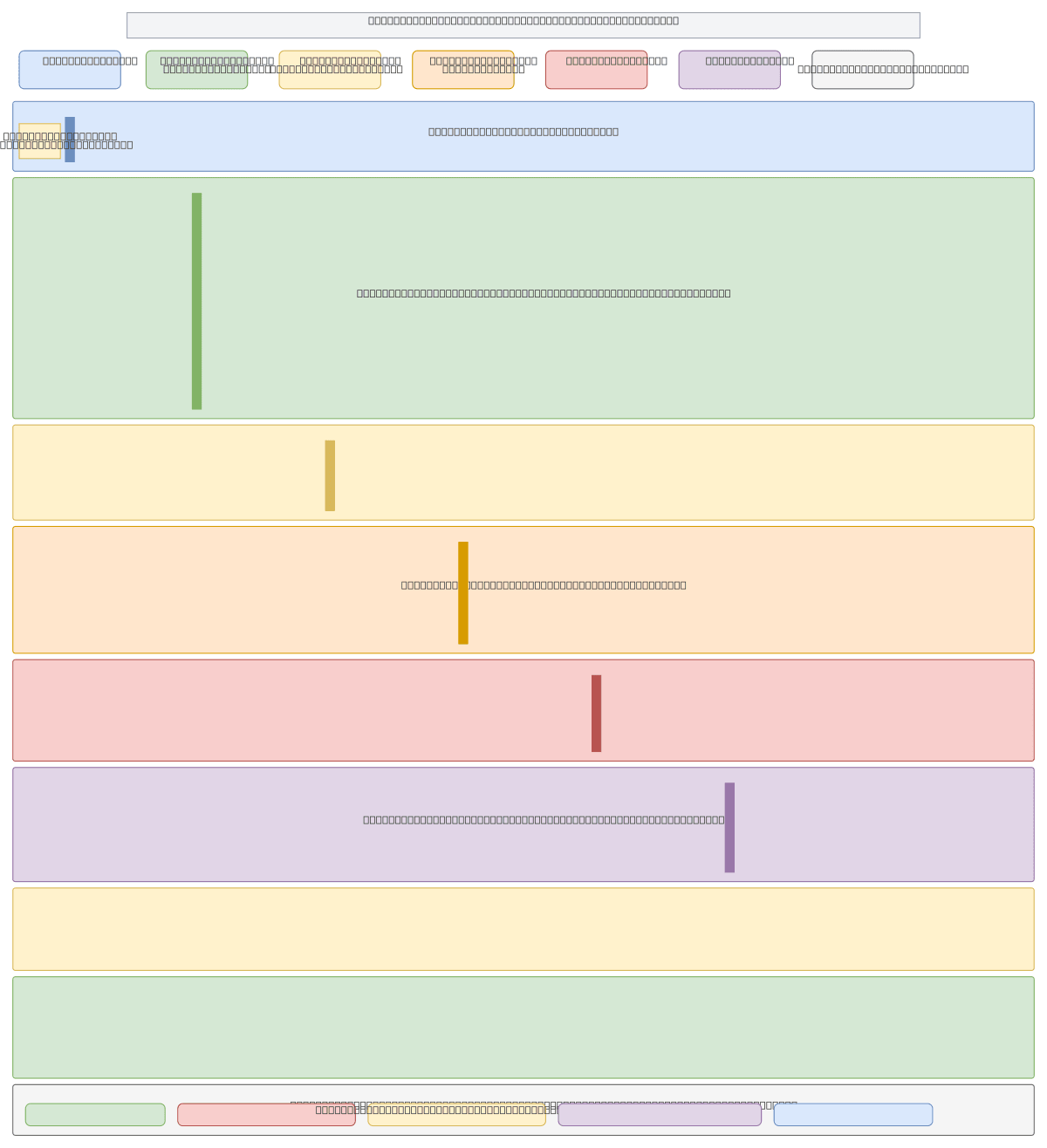
End-to-End Agent Orchestration Flow
About This Architecture
End-to-end agent orchestration flow integrating Microsoft Entra ID, Azure Logic Apps, and Microsoft Foundry with zero-trust authentication and human-in-the-loop approval gates. Requests flow from Teams, APIs, events, or schedules through Entra ID identity verification, then to Logic Apps for orchestration, Microsoft Foundry task agents, and external systems like SAP, ServiceNow, and Salesforce via MCP and REST protocols. Human approvers in Teams or email validate critical decisions before final execution, while Defender, Purview, and OpenTelemetry provide continuous governance, threat detection, and end-to-end observability across all phases. This architecture demonstrates enterprise-grade agent governance with per-agent metrics, token usage tracking, and correlation ID propagation for full auditability and cost attribution.
People also ask
How do I orchestrate multi-agent workflows on Azure with zero-trust security and human approval gates?
This diagram shows a 9-phase orchestration flow starting with Entra ID zero-trust authentication, routing through Azure Logic Apps, invoking Microsoft Foundry agents, connecting to external systems (SAP, ServiceNow, Salesforce), and including optional human approval in Teams before execution. Defender, Purview, and OpenTelemetry provide continuous threat detection, data governance, and end-to-end
- Domain:
- Cloud Multi
- Audience:
- Enterprise cloud architects designing multi-agent orchestration systems on Azure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.