diagram (4) (1)
About This Architecture
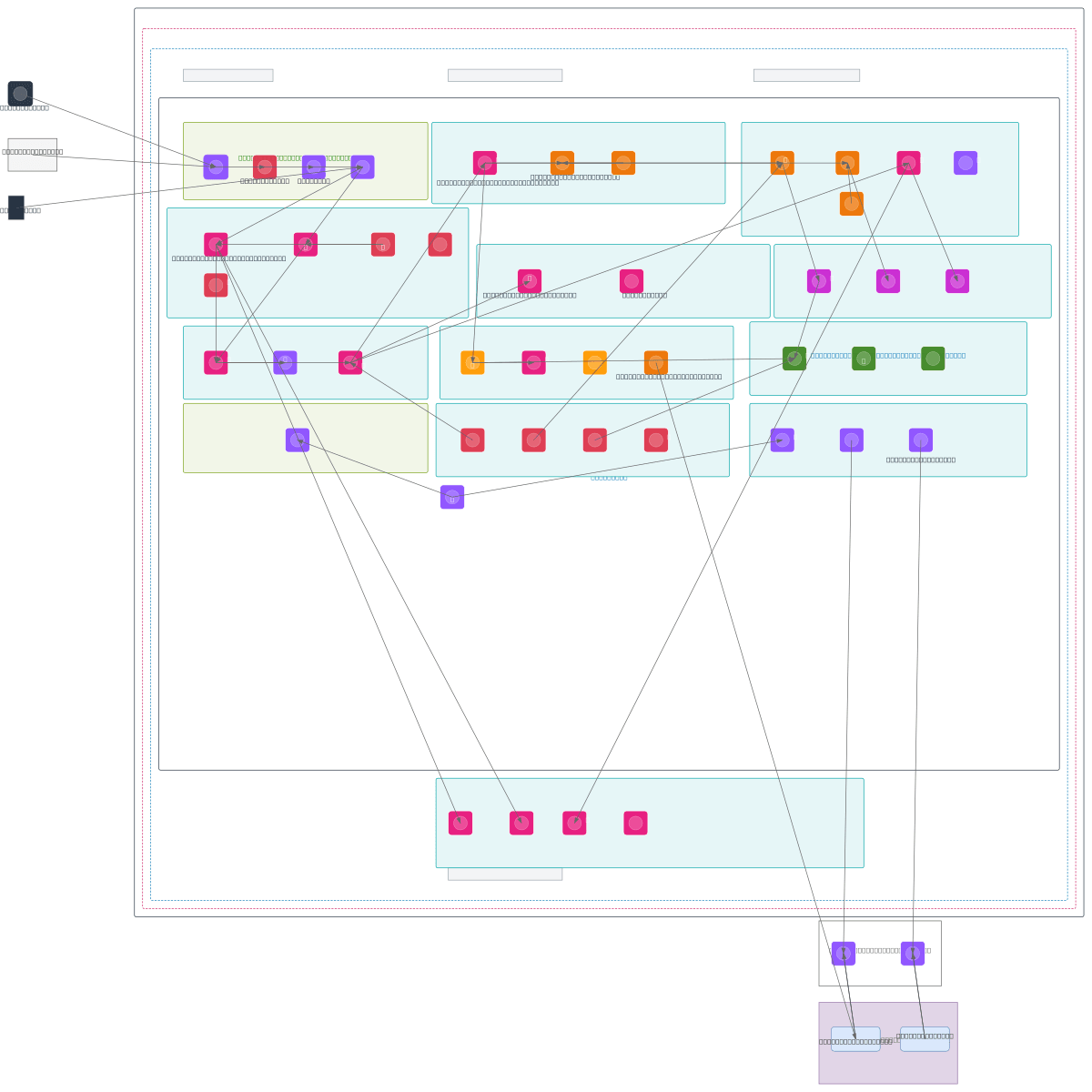
Enterprise banking platform spanning experience, process, system, and backend layers across three AWS VPCs with hybrid on-premise connectivity via Transit Gateway and Direct Connect. Internet Users and Partner Systems reach public APIs through Route 53, CloudFront CDN, WAF, and API Gateway with OAuth2/mTLS authentication, while internal teams access private APIs via VPC Endpoints and IAM. Process layer orchestrates workflows using Step Functions, ECS/EKS containers, EventBridge event bus, and async SQS queues; batch ETL runs on Glue and EMR with DataSync bridging hybrid data transfer. System layer exposes microservices via EKS with KEDA autoscaling, backed by RDS Aurora, DynamoDB, ElastiCache, S3 data lake, and EFS shared storage, all secured with KMS encryption, Secrets Manager, and GuardDuty threat detection. Cross-account observability via CloudWatch, X-Ray, and CloudTrail provides governance and audit trails for compliance-heavy financial workloads. Fork this diagram to customize VPC CIDR blocks, add additional regions, or adjust API Gateway throttling and WAF rules for your organization's scale and threat model.
People also ask
How do I design a secure, scalable AWS architecture for an enterprise banking platform with public APIs, internal microservices, hybrid on-premise connectivity, and audit compliance?
This diagram shows a three-VPC AWS design separating experience (API Gateway, CloudFront, WAF), process (Step Functions, ECS/EKS, EventBridge), and system layers (Lambda, EKS, RDS Aurora, DynamoDB). Hybrid connectivity via Transit Gateway and Direct Connect bridges on-premise systems; cross-account CloudWatch, X-Ray, and CloudTrail provide governance and audit trails required for financial complia
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing multi-tier enterprise banking platforms
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.