diagram (3)
About This Architecture
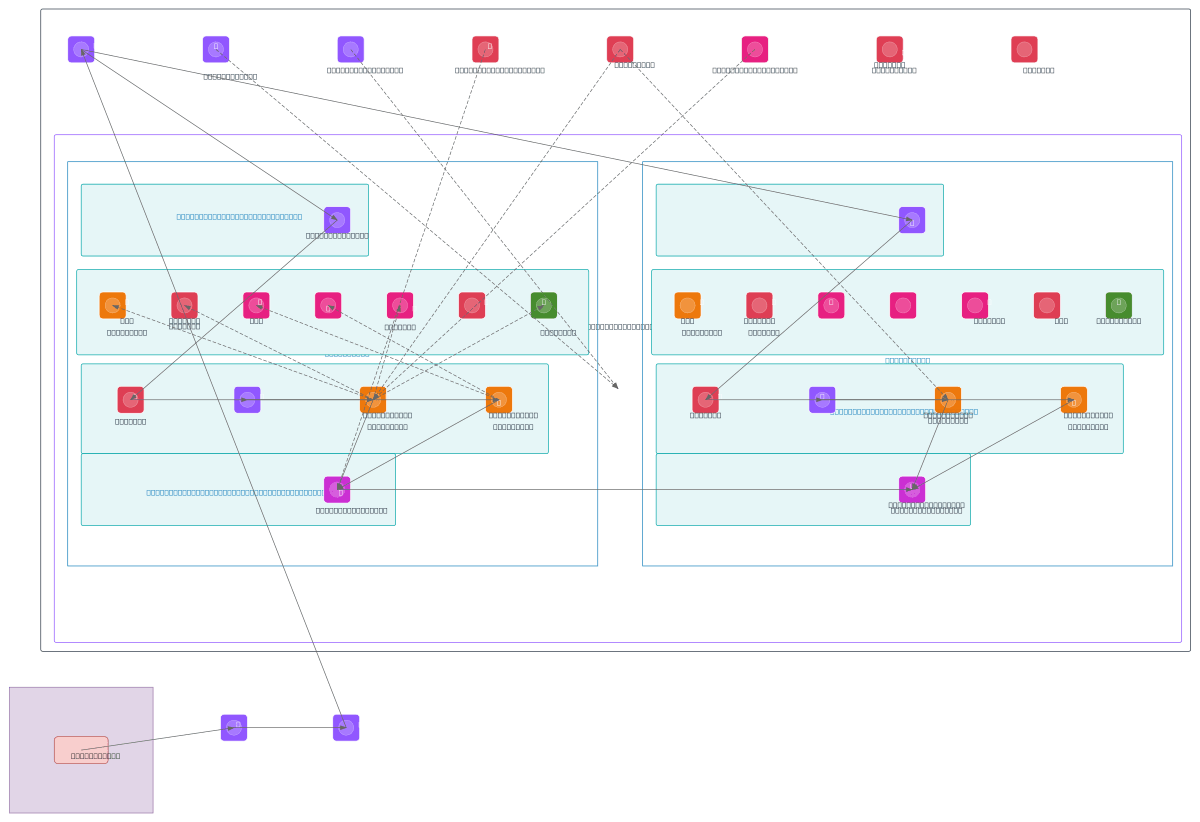
Multi-AZ AWS VPC with Transit Gateway hybrid connectivity, featuring IPAM-managed IP addressing across isolated subnets for transit, application, and database tiers. ECS Fargate services in application subnets route through AWS WAF and internal ALB, accessing Aurora PostgreSQL with read replicas, ECR, Secrets Manager, and VPC endpoints for S3 and other services. IAM roles enforce least-privilege access to ECS tasks, while KMS encrypts data at rest and CloudWatch monitors all workloads. AWS Direct Connect and Cloud WAN establish secure on-premises connectivity through Transit Gateway, with Route 53 Resolver providing hybrid DNS resolution. Fork this diagram on Diagrams.so to customize subnets, add additional services, or adapt for your multi-region strategy. This architecture demonstrates AWS best practices for zero-trust networking, encryption, and least-privilege IAM in production environments.
People also ask
How do I design a secure multi-AZ AWS VPC with hybrid on-premises connectivity and least-privilege IAM for ECS Fargate services?
This diagram shows a production-grade AWS architecture using Transit Gateway to connect on-premises networks via AWS Direct Connect, IPAM for centralized IP management across isolated subnets, and ECS Fargate services protected by AWS WAF and internal ALB. IAM roles enforce least-privilege access, KMS encrypts Aurora PostgreSQL data, and CloudWatch monitors all workloads—demonstrating AWS security
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure, multi-AZ enterprise applications with hybrid connectivity
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.