diagram (1)
About This Architecture
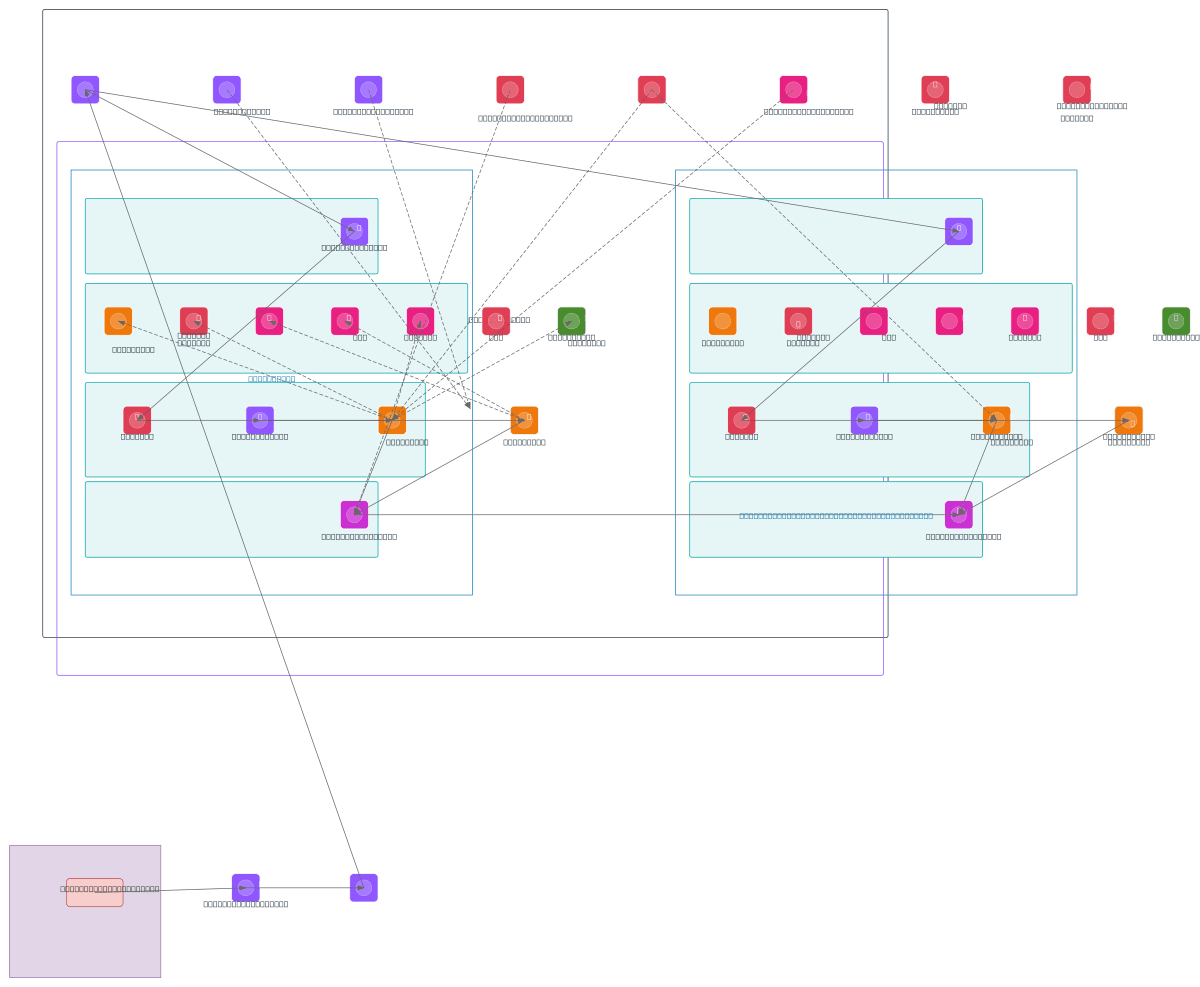
Multi-AZ VPC architecture in eu-west-2 with IPAM-managed IP addressing, Transit Gateway connectivity, and isolated database subnets across availability zones. Traffic flows from Transit Gateway through AWS WAF and Internal ALB to ECS Fargate services in application subnets, with encrypted Aurora PostgreSQL in isolated database subnets. IAM task roles enforce least privilege, KMS encrypts data at rest, and VPC endpoints for ECR, Secrets Manager, S3, SQS, SNS, and CloudWatch eliminate internet exposure. Fork this diagram on Diagrams.so to customize subnets, add NAT gateways, or extend Transit Gateway attachments for hybrid connectivity. This pattern demonstrates AWS best practices for production workloads requiring defense-in-depth, compliance-ready isolation, and zero-trust network segmentation.
People also ask
How do I design a secure multi-AZ VPC architecture on AWS with ECS Fargate, Aurora, and VPC endpoints?
This diagram shows a production-grade multi-AZ VPC in eu-west-2 using IPAM for IP management, Transit Gateway for hybrid connectivity, and isolated subnets for transit, application, and database tiers. ECS Fargate services access encrypted Aurora PostgreSQL through private subnets, while AWS WAF, security groups, NACLs, KMS encryption, and least-privilege IAM roles enforce defense-in-depth securit
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure, multi-AZ VPC architectures with ECS Fargate
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.