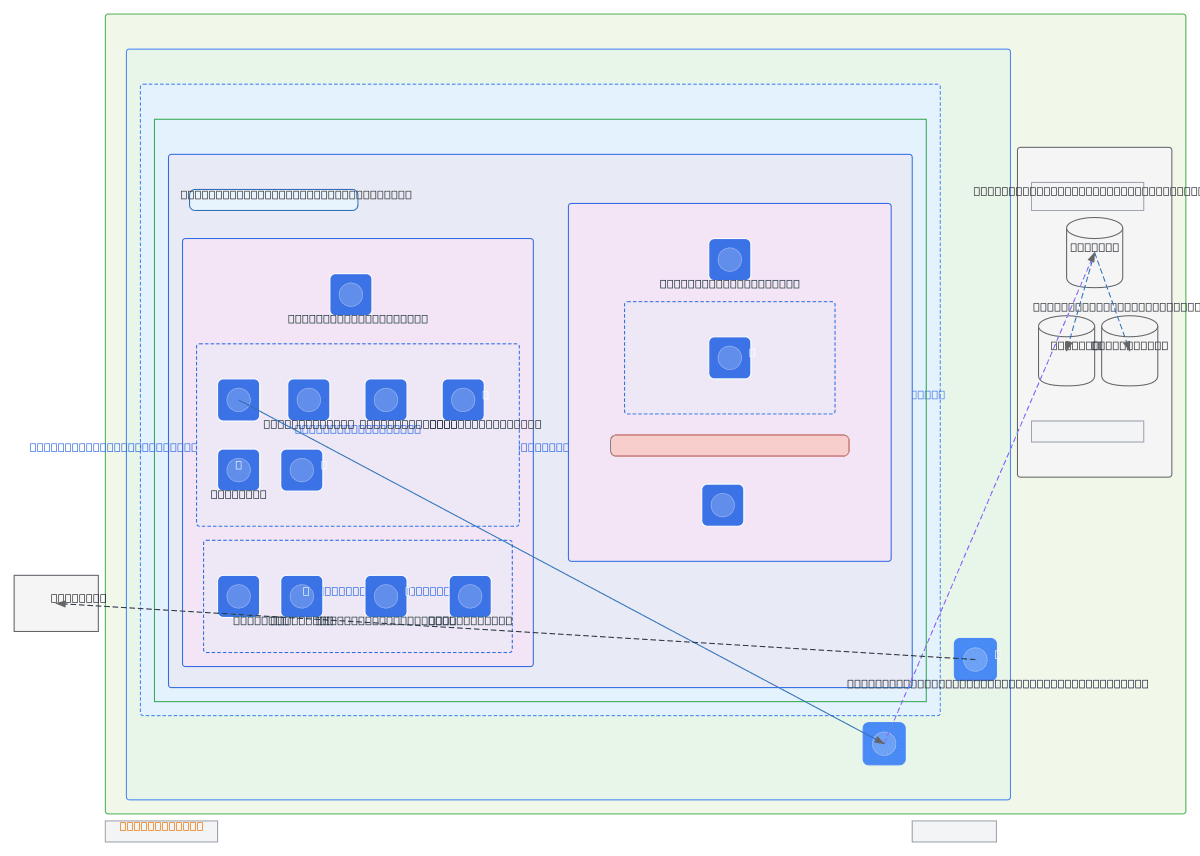
DEV Cluster Topology - ep3-quantax-dev
About This Architecture
GKE cluster ep3-quantax-dev running on GCP with segregated node pools for application and Redpanda workloads, using private endpoints and Cloud NAT for secure egress-only networking. The topology spans a VPC with separate node and pod CIDR ranges, featuring a default node pool for Kilkenny services and a dedicated Redpanda pool with hard NO_SCHEDULE taints to isolate stateful brokers. MongoDB Atlas integrates via Private Service Connect, eliminating public IP exposure while maintaining high availability through a 3-node replica set. This architecture demonstrates production-grade isolation patterns suitable for development environments requiring multi-tenant workload separation and external database connectivity without internet-facing endpoints.
People also ask
How do you design a GKE cluster with isolated node pools for Redpanda brokers and secure MongoDB Atlas connectivity without public IPs?
This diagram shows ep3-quantax-dev using separate node pools with taints (PREFER_NO_SCHEDULE for default, hard NO_SCHEDULE for Redpanda) to isolate workloads, Private Service Connect for MongoDB Atlas replica set access, and Cloud NAT for egress-only internet connectivity. Control plane and nodes remain private with no public endpoints.
- Domain:
- Kubernetes
- Audience:
- Kubernetes platform engineers managing GKE clusters in development environments
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.