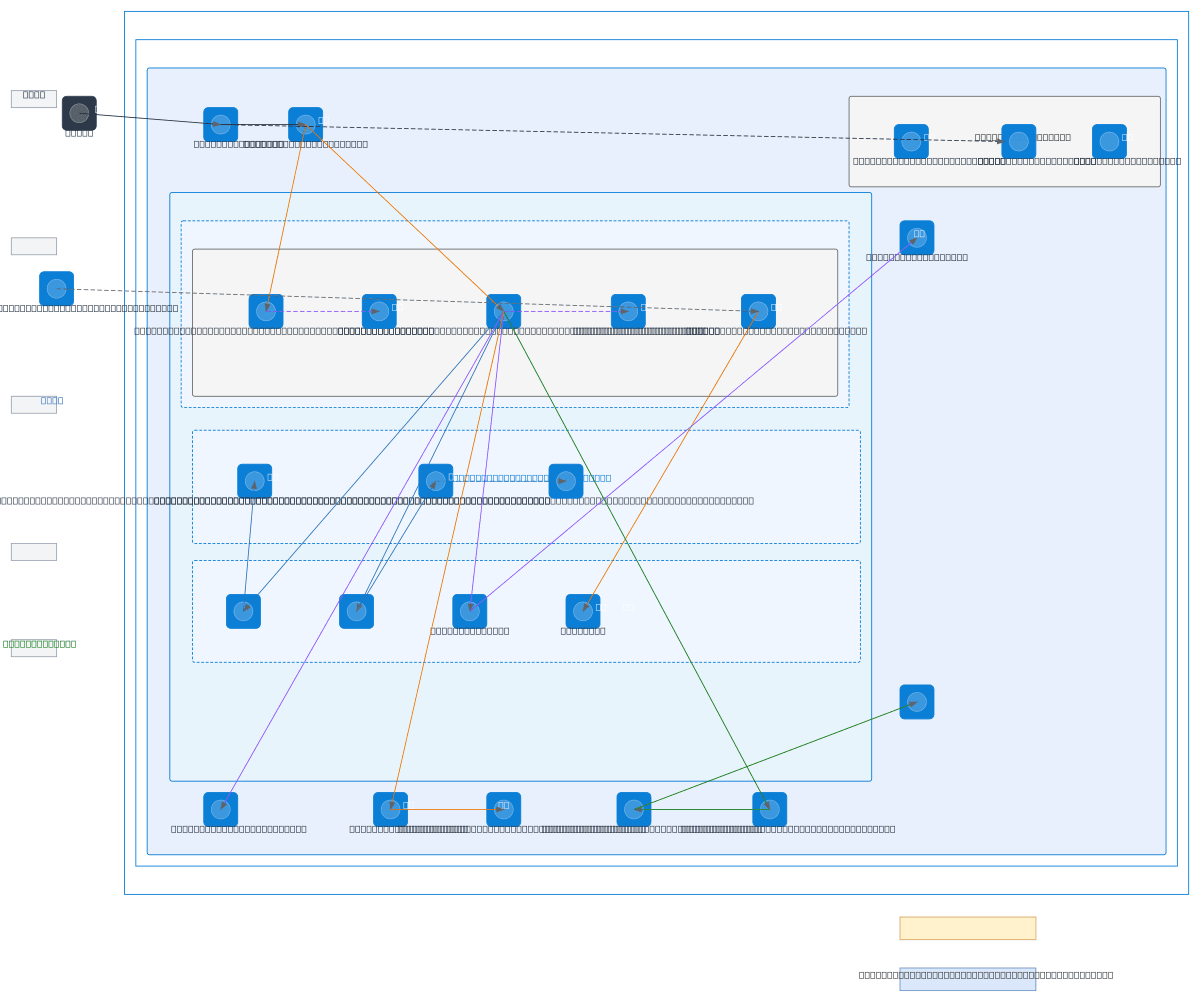
DELABO Azure Production Architecture
About This Architecture
DELABO's Azure production architecture combines Azure Front Door with WAF (OWASP 3.2) to protect an Angular SPA and Spring Boot backend running on Container Apps with auto-scaling (1-3 and 2-10 replicas respectively). The backend accesses PostgreSQL Flexible Server, Storage Account blobs, and Key Vault through private endpoints in isolated subnets, with all identities managed via Managed Identity and Entra External ID. Observability spans Log Analytics, Application Insights, and Azure Monitor alerts, while GitLab CI/CD integrates via Workload Identity Federation for zero-secret deployments. This architecture demonstrates defense-in-depth: perimeter security via WAF, network isolation via private endpoints and VNet segmentation (10.0.0.0/16), identity-first access control, and comprehensive monitoring across dev, staging, and production subscriptions. Fork and customize this diagram on Diagrams.so to adapt the subnet ranges, replica counts, or storage redundancy (GRS vs LRS) for your own multi-tier Azure applications.
People also ask
How do I design a secure, production Azure architecture with Container Apps, private endpoints, and Managed Identity?
DELABO's architecture uses Azure Front Door + WAF (OWASP 3.2) for perimeter security, Container Apps for auto-scaling workloads, private endpoints to isolate PostgreSQL, Storage, and Key Vault access, and Managed Identity for zero-secret authentication. Multi-subnet VNet segmentation and zone-redundant PostgreSQL HA ensure resilience and compliance.
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing secure, scalable production workloads on Container Apps
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.