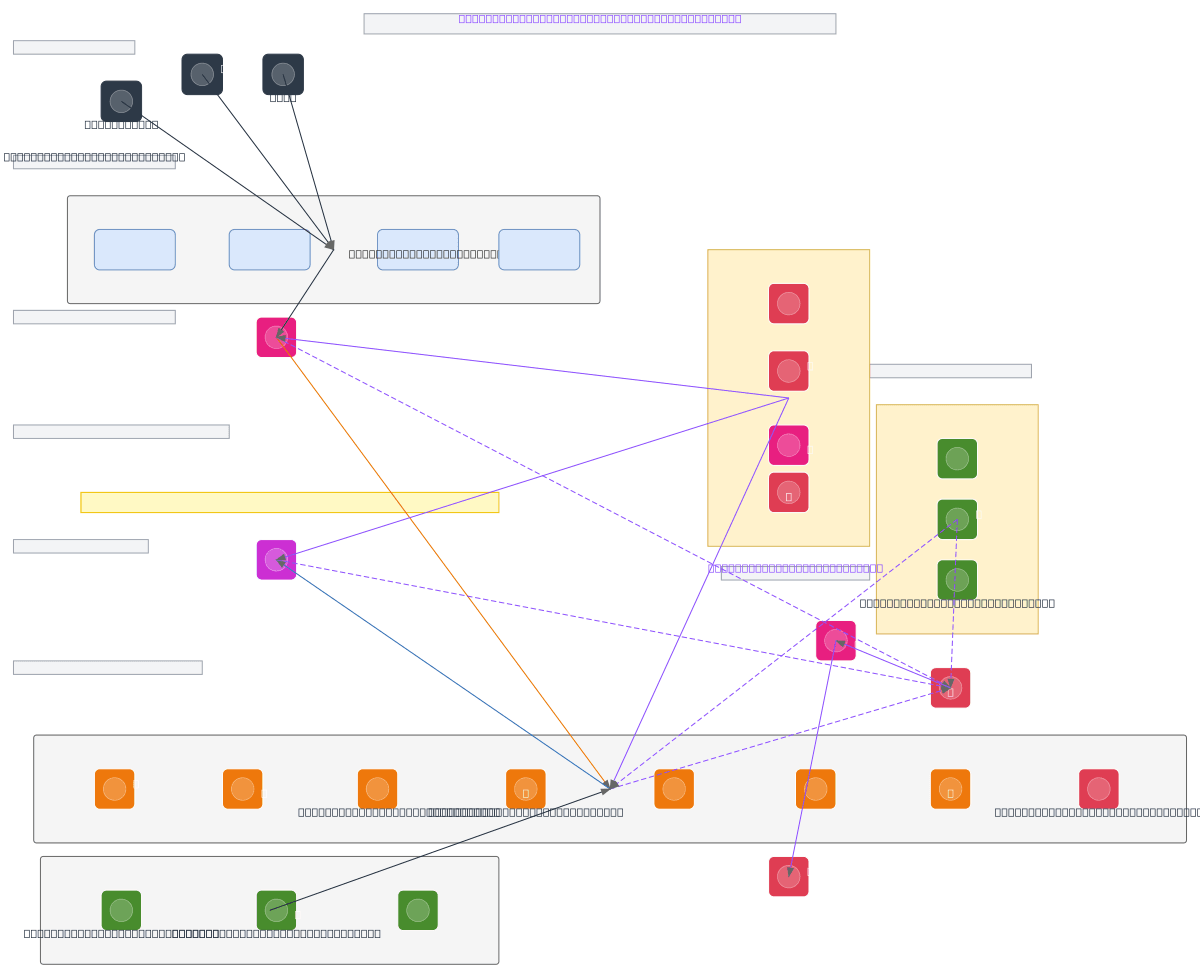
Defense-Grade DevSecOps Enterprise Architecture
About This Architecture
Defense-grade DevSecOps enterprise architecture implements zero-trust principles across seven layers, from user personas through air-gapped offline modules, enforcing mTLS, JWT authentication, and RBAC at every boundary. Data flows from external SBOM and CVE sources through normalization, vulnerability mapping, and risk classification services into an encrypted PostgreSQL backend, with frontend dashboards exposing risk, inventory, and governance views to super admins, managers, and users. This architecture solves critical supply-chain security challenges by correlating component provenance, SBOM ingestion, and vulnerability feeds while maintaining strict access control and audit trails. Fork this diagram on Diagrams.so to customize threat models, add provider-specific WAF rules, or integrate your organization's KMS and secrets management. The air-gapped module design ensures offline SBOM and CVE import for high-security environments where internet connectivity is restricted.
People also ask
How do I design a zero-trust DevSecOps platform that ingests SBOMs and CVE data while maintaining air-gapped offline capabilities for high-security environments?
This diagram shows a seven-layer architecture where SBOM files and vulnerability feeds flow through normalization, mapping, and risk classification services into an encrypted PostgreSQL backend, with an air-gapped offline module enabling secure import/export without internet access. Zero-trust is enforced via mTLS between core services, JWT at the API gateway, and RBAC across user personas, while
- Domain:
- Security
- Audience:
- Security architects designing defense-grade DevSecOps platforms with zero-trust and air-gapped compliance requirements
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.