corredor_ecs_updated
About This Architecture
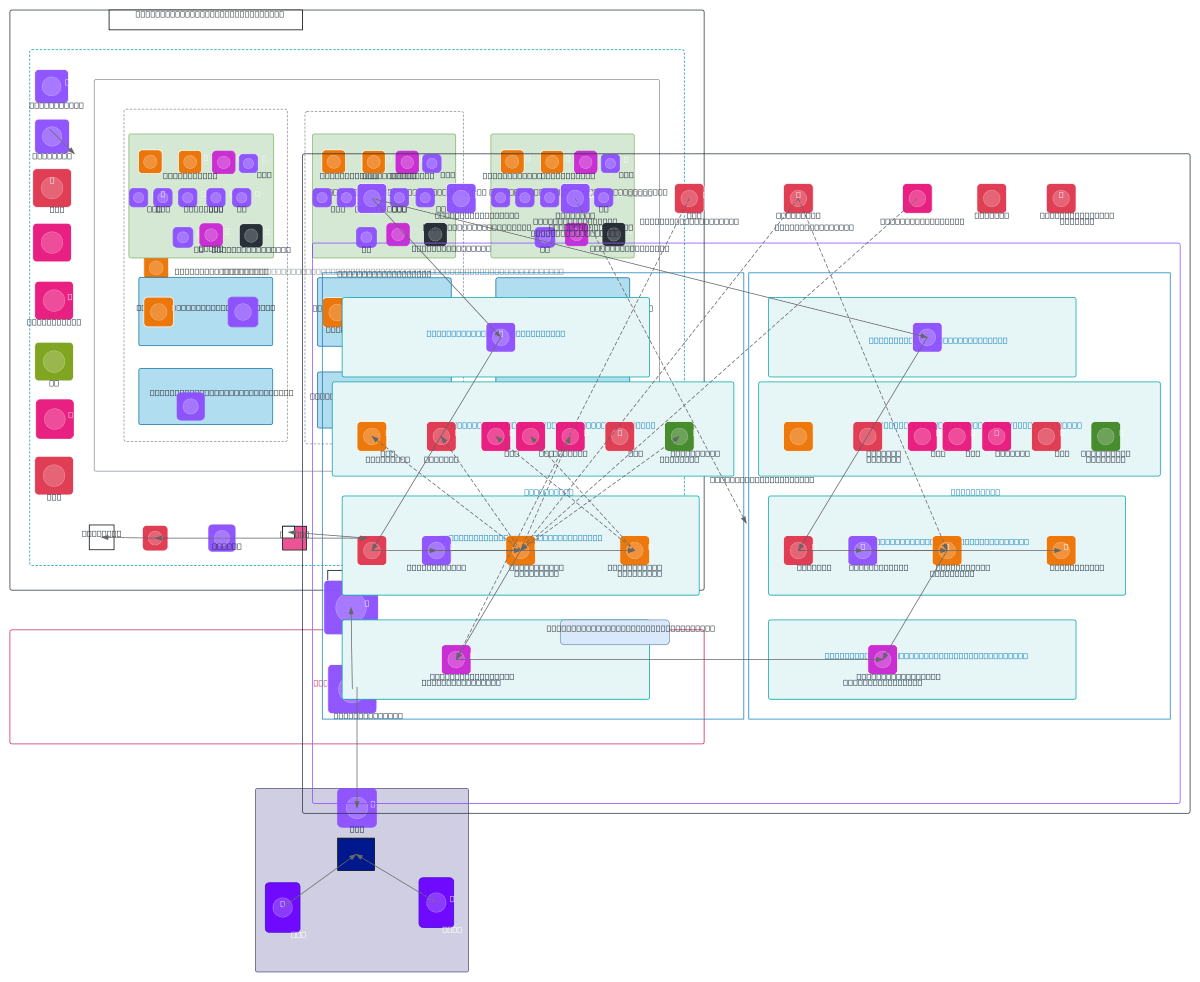
Multi-availability zone ECS Fargate architecture spanning eu-west-2 with dual routable and non-routable subnets, integrating AI microservices, vector databases, and Kafka event streaming. Traffic flows through Route 53, API Gateway, and AWS WAF to internal ALB, then to ECS tasks across AZ1 and AZ2 with Istio service mesh orchestration. The design implements least-privilege network segmentation using routable CIDR 10.59.0.0/24 and non-routable CIDR 100.100.0.0/16, with egress firewall controls and Direct Connect hybrid connectivity to NatWest DC. This architecture demonstrates enterprise-grade isolation, observability via CloudWatch and CloudTrail, and secure secret management through SSM Parameter Store and Secrets Manager. Fork this diagram on Diagrams.so to customize subnets, add additional AZs, or adapt the Istio mesh configuration for your workload.
People also ask
How do I design a production AWS ECS Fargate architecture across multiple availability zones with service mesh, hybrid networking, and AI workloads?
This diagram shows a multi-AZ ECS Fargate deployment in eu-west-2 using routable (10.59.0.0/24) and non-routable (100.100.0.0/16) subnets, with Istio orchestrating microservices and Kafka enabling event streaming. Traffic enters via Route 53 and API Gateway through AWS WAF, routes to internal ALB, then to ECS tasks running AI services with vector DB and Textract, while Direct Connect provides secu
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing multi-AZ ECS Fargate deployments with hybrid network connectivity
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.