Corporate Two-Building Network — Logical Topology
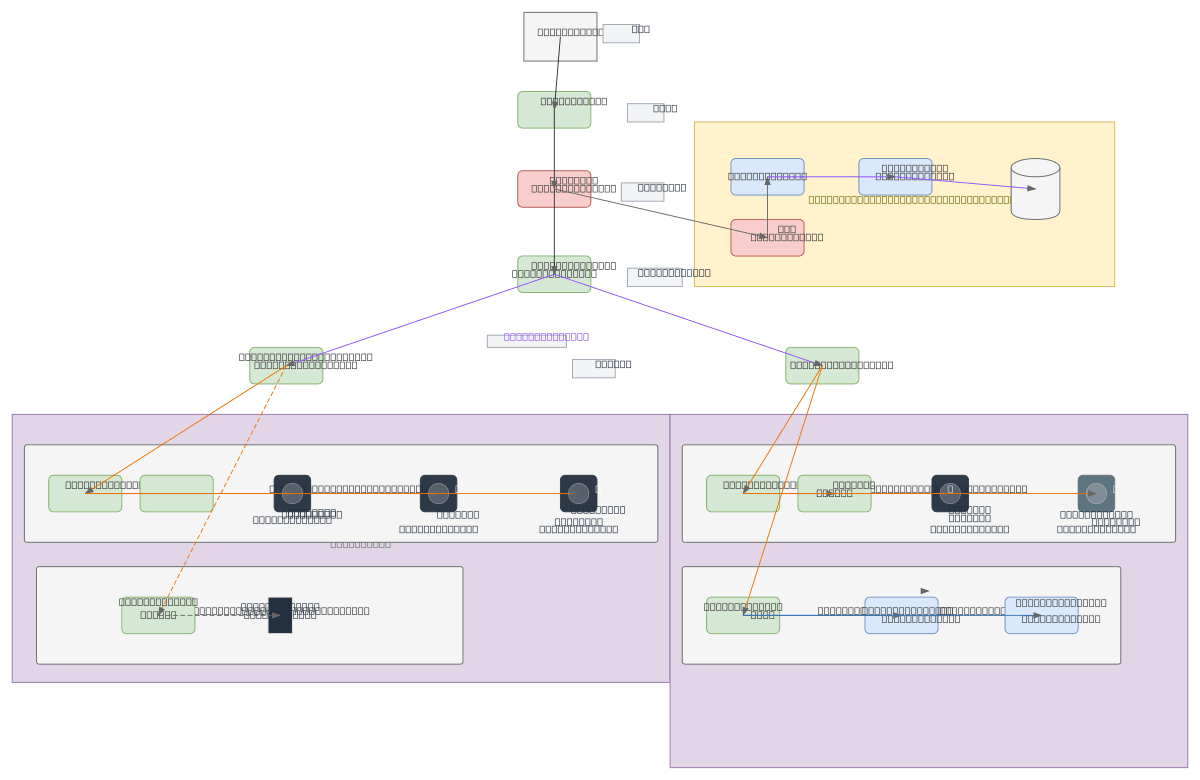
About This Architecture
Multi-building enterprise network with DMZ, four VLANs, and fiber backbone connecting two distribution switches across buildings. Traffic flows from Internet through Core Router and Firewall to DMZ servers, then to L3 Core Switch distributing to Building 1 (Office, Guest WiFi) and Building 2 (IT, Production) via fiber backbone. Each building uses L3 Distribution Switches and Cat6 Access Switches to segment departments by VLAN—Management, Finance, Marketing in Building 1; IT, Software Dev, Production, Quality Control in Building 2—with wireless APs for each VLAN. This architecture demonstrates defense-in-depth with perimeter security, network segmentation by function, and scalable access layer design for 100+ users across two sites. Fork this diagram on Diagrams.so to customize IP ranges, add additional VLANs, or adapt for your campus network topology.
People also ask
How do you design a secure multi-building corporate network with VLAN segmentation and a DMZ?
This diagram shows a hierarchical network with a perimeter Firewall protecting a DMZ containing Web, File, and Database Servers, then routing internal traffic through an L3 Core Switch to Building 1 and Building 2 via fiber backbone. Each building uses L3 Distribution Switches and Cat6 Access Switches to isolate departments (Management, Finance, Marketing, IT, Production, Quality Control) into sep
- Domain:
- Networking
- Audience:
- Network architects designing multi-building enterprise LANs with VLAN segmentation
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.