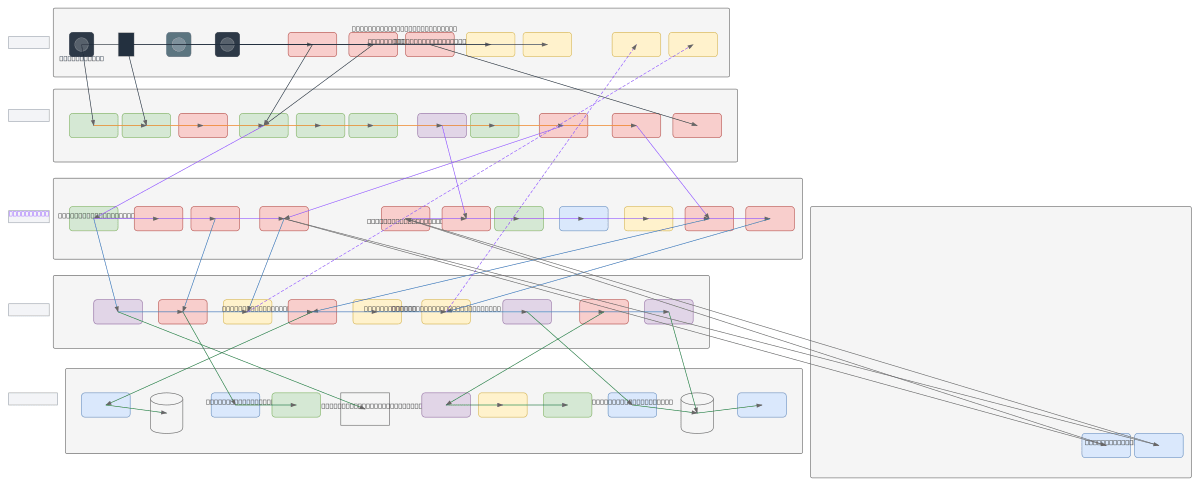
Comprehensive ZTNA and SASE Architecture
About This Architecture
Zero-trust network access (ZTNA) and secure access service edge (SASE) architecture unifies identity verification, endpoint posture checks, and multi-layer threat protection across remote users, mobile devices, managed laptops, and IoT endpoints. Traffic flows through an identity and endpoint tier for authentication and device compliance, then through a SASE cloud security stack delivering DNS filtering, web gateway, CASB, DLP, threat protection, and sandboxing before reaching protected resources on-premises, in cloud, or SaaS. A zero-trust policy engine continuously evaluates risk scores, enforces micro-segmentation, and orchestrates access decisions based on identity, device posture, and behavioral analytics. This architecture eliminates implicit trust, reduces attack surface, and ensures least-privilege access regardless of user location or device type. Fork this diagram on Diagrams.so to customize policies, add provider-specific gateways, or integrate your identity and threat intelligence platforms. Advanced deployments may layer SD-WAN gateways, next-gen firewalls, and DDoS protection for hybrid and multi-cloud environments.
People also ask
How do ZTNA and SASE architectures work together to enforce zero-trust access control?
ZTNA and SASE combine identity verification (IdP, MFA, PKI), endpoint posture checks (EDR, UEM, device compliance), and a SASE cloud security stack (SWG, CASB, DLP, threat protection) to authenticate and inspect all traffic before granting access. A zero-trust policy engine continuously scores risk, enforces micro-segmentation, and orchestrates access decisions based on identity, device health, an
- Domain:
- Security
- Audience:
- Security architects designing zero-trust network access (ZTNA) and secure access service edge (SASE) implementations
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.