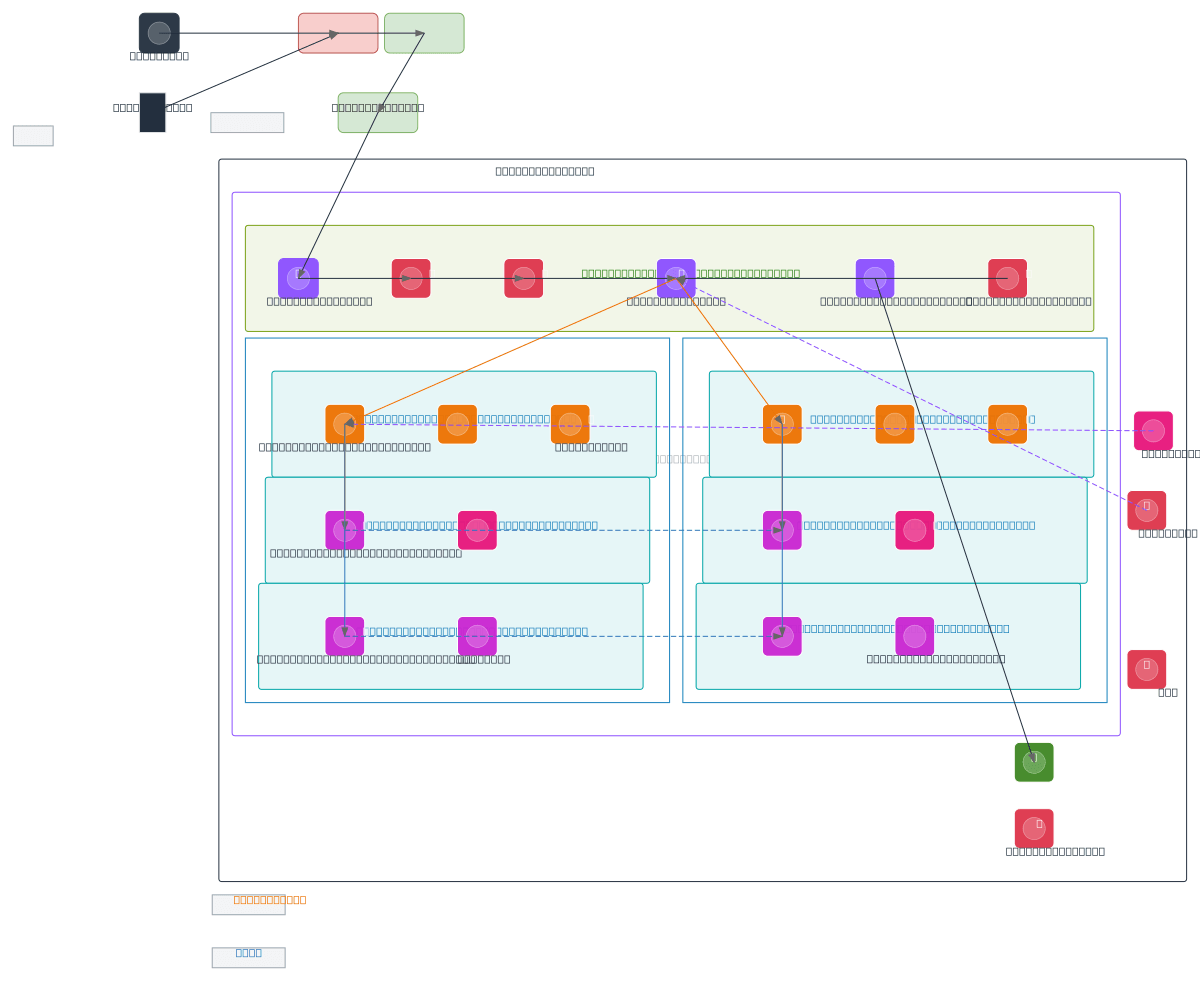
Cloudflare WAF to AWS Multi-AZ Secure Architecture
About This Architecture
Cloudflare WAF to AWS multi-AZ secure architecture combines edge protection with AWS native defenses across two availability zones. End users and mobile clients route through Cloudflare WAF, CDN, and DNS before reaching an Internet Gateway, AWS WAF, and Shield Advanced protecting an Application Load Balancer. Nginx EC2 instances in private app subnets across AZ-1 and AZ-2 scale automatically, connecting to ElastiCache clusters, RDS Aurora primary/standby databases, and DynamoDB for resilient data access. This design demonstrates defense-in-depth with layered WAF rules, multi-AZ failover, encrypted secrets management, and continuous monitoring via CloudWatch and GuardDuty. Fork this diagram on Diagrams.so to customize subnets, instance types, or add additional AWS services like Lambda or API Gateway. The architecture prioritizes availability and security by isolating compute, cache, and data tiers across private subnets while maintaining zero-trust principles.
People also ask
How do I design a highly available, secure AWS multi-AZ architecture with Cloudflare WAF and RDS Aurora failover?
This diagram shows a production-ready multi-AZ AWS architecture where Cloudflare WAF provides edge-level DDoS and threat protection, routing traffic through AWS WAF and Shield Advanced to an ALB. Nginx EC2 instances in private subnets across AZ-1 and AZ-2 auto-scale and connect to ElastiCache for caching and RDS Aurora primary/standby for database failover, ensuring zero-downtime deployments and a
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available, secure multi-AZ web applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.