Cloudflare WAF and Palo Alto Hub-and-Spoke AWS
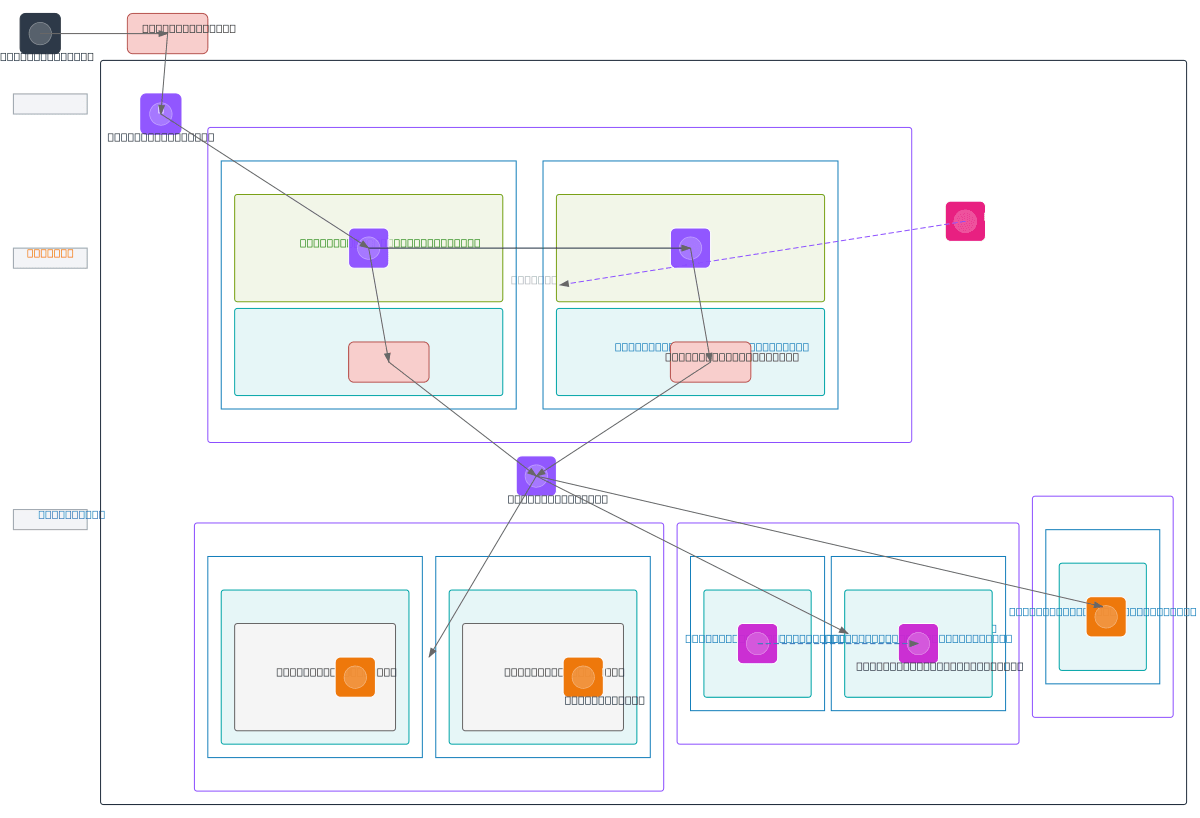
About This Architecture
Cloudflare WAF and Palo Alto NGFW hub-and-spoke architecture secures multi-VPC AWS deployments with layered defense across Internet Gateway, AWS WAF, and dual-AZ Palo Alto firewalls in the hub. Internet traffic flows through Cloudflare WAF to the Internet Gateway, then AWS WAF and Application Load Balancers, before reaching Palo Alto NGFW instances in AZ-1 and AZ-2 that inspect and route traffic via Transit Gateway to three spoke VPCs: App (EC2), Data (RDS), and Shared Services (Lambda, AWS WAF, AWS Shield, CloudWatch, GuardDuty). This architecture implements defense-in-depth with DDoS mitigation, application-layer filtering, and network-layer inspection while maintaining high availability and compliance visibility. Fork this diagram on Diagrams.so to customize CIDR ranges, add additional spokes, or integrate with your existing Terraform or CloudFormation pipelines. The Network Firewall component provides stateful inspection at the network perimeter, complementing Palo Alto NGFW for comprehensive threat detection.
People also ask
How do I design a secure multi-VPC AWS architecture with Cloudflare WAF and Palo Alto firewalls?
This diagram shows a hub-and-spoke pattern where Cloudflare WAF filters Internet traffic, AWS WAF and ALBs provide application-layer protection, and dual-AZ Palo Alto NGFW instances in the hub VPC inspect and route traffic to three spoke VPCs via Transit Gateway. The architecture layers DDoS mitigation, WAF rules, and stateful firewall inspection for defense-in-depth security across App, Data, and
- Domain:
- Cloud Multi
- Audience:
- AWS solutions architects designing multi-VPC security architectures with centralized threat protection
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.