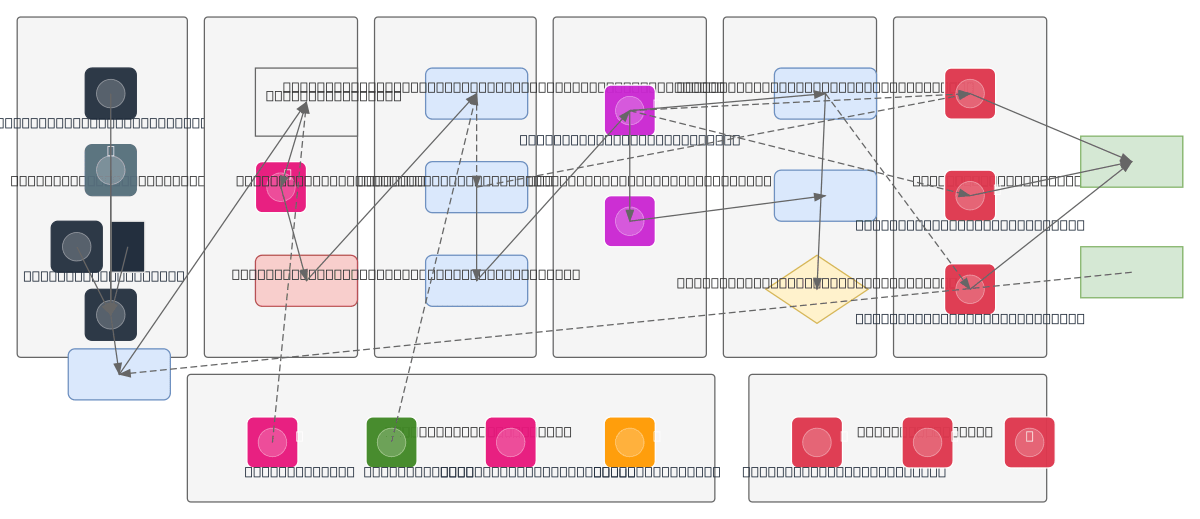
Biometric Authentication Data Pipeline
About This Architecture
End-to-end biometric authentication pipeline on AWS ingests fingerprint, facial, and voice data through dedicated capture modules, then processes signals through noise removal, enhancement, and feature extraction stages. The Data Acquisition Module feeds into Pre-processing and Feature Engineering layers, which extract minutiae, landmarks, and voice patterns before template generation and encrypted storage. Matching Engine compares live input against enrolled templates with threshold-based decision logic, routing to Authentication Server for access grant/deny, while X-Ray tracing, WAF, Shield DDoS protection, and AES encryption secure the entire flow. Fork this diagram on Diagrams.so to customize sensor inputs, adjust matching thresholds, or integrate with your AWS IAM and Cognito services. Liveness detection anti-spoofing and Activity Logs with Failed Attempts Monitor provide audit trails and fraud prevention critical for regulated identity verification workloads.
People also ask
How do you build a secure biometric authentication system on AWS that processes fingerprint, face, and voice data with anti-spoofing protection?
This diagram shows a complete AWS biometric pipeline: User Input flows through Data Acquisition (Fingerprint Scanner, Camera, Microphone) → Pre-processing (noise removal, enhancement) → Feature Extraction (minutiae, landmarks, voice patterns) → Template Generator → Encrypted Template Database. During authentication, the Matching Engine compares live features against enrolled templates, the Decisio
- Domain:
- Data Engineering
- Audience:
- AWS solutions architects designing secure biometric authentication systems
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.