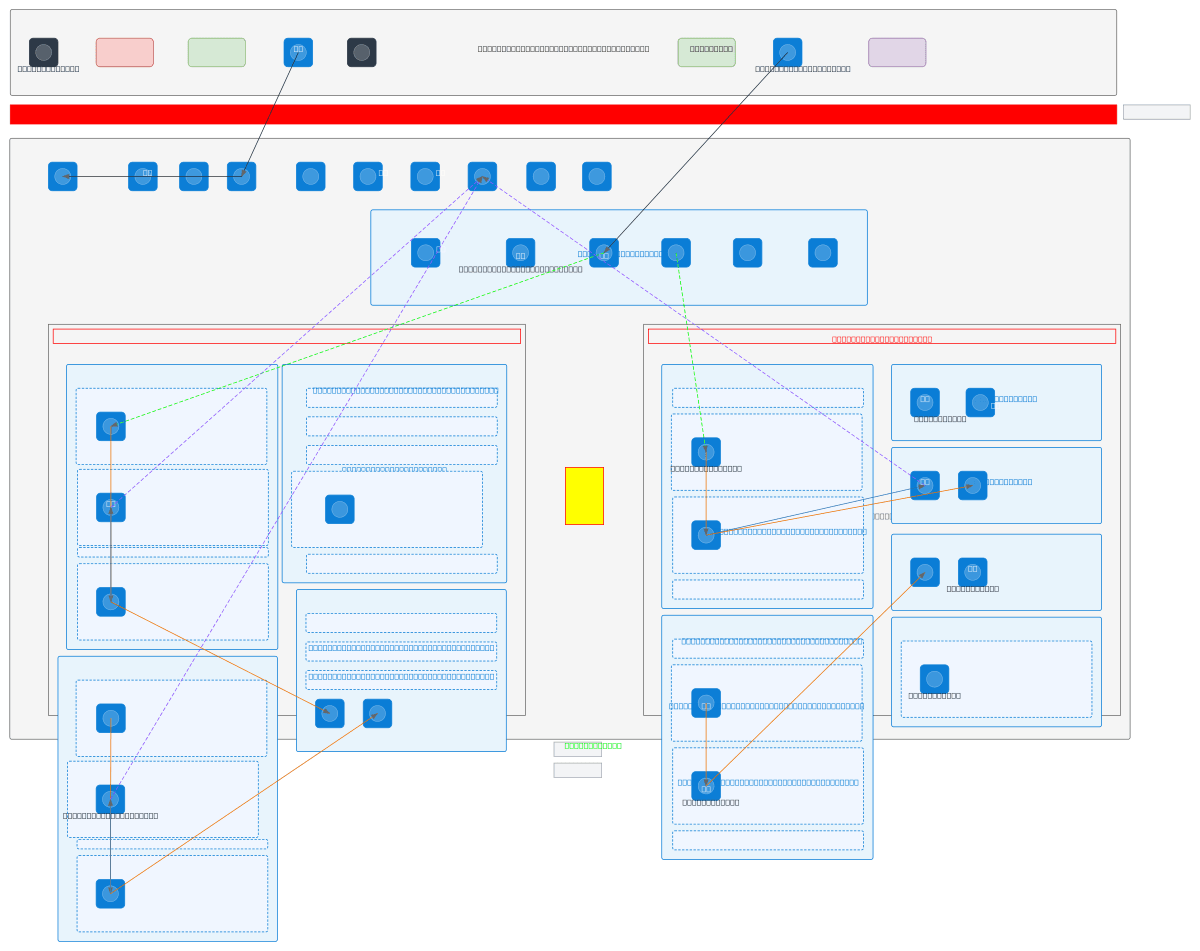
USACE Azure IL4 and IL5 Combined Authorization Boundary
About This Architecture
Multi-region Azure Government authorization boundary architecture segregating DoD Impact Level 4 (IL4) and Impact Level 5 (IL5) workloads across Azure Gov Virginia, Texas, DoD East, and DoD Central regions. ExpressRoute circuits connect on-premises USACE Active Directory and NIPRNET users through JRSS security stack to hub-spoke VNet topology with centralized Azure Firewall, Private DNS Resolver, and Log Analytics in transit hubs. IL4 zone deploys App Service Environments, SQL Managed Instance, and VMSS web tiers behind Application Gateway WAF with CAC authentication via Entra ID Conditional Access and PIM, while IL5 zone isolates AKS clusters, Cosmos DB, and Function Apps with separate trust boundaries enforced by Azure Policy and Defender for Cloud. This reference architecture demonstrates USACE compliance with DISA BCAP requirements and CUI data protection mandates for federal agencies. Fork this diagram on Diagrams.so to customize subnets, add your agency's security controls, or export as .drawio for RMF documentation packages.
People also ask
How do I architect separate Azure authorization boundaries for DoD Impact Level 4 and Impact Level 5 workloads with ExpressRoute connectivity to on-premises NIPRNET?
Deploy hub-spoke VNet topology across Azure Gov and DoD regions with centralized Azure Firewall and Log Analytics in transit hubs. Use separate VNets and Azure Policy enforcement for IL4 and IL5 zones with no direct trust between them. Connect on-premises USACE AD via ExpressRoute through JRSS security stack, enforce CAC authentication with Entra ID Conditional Access, and monitor with Sentinel an
- Domain:
- Cloud Azure
- Audience:
- DoD cloud architects and USACE security engineers implementing FedRAMP High and DoD IL4/IL5 compliance
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.