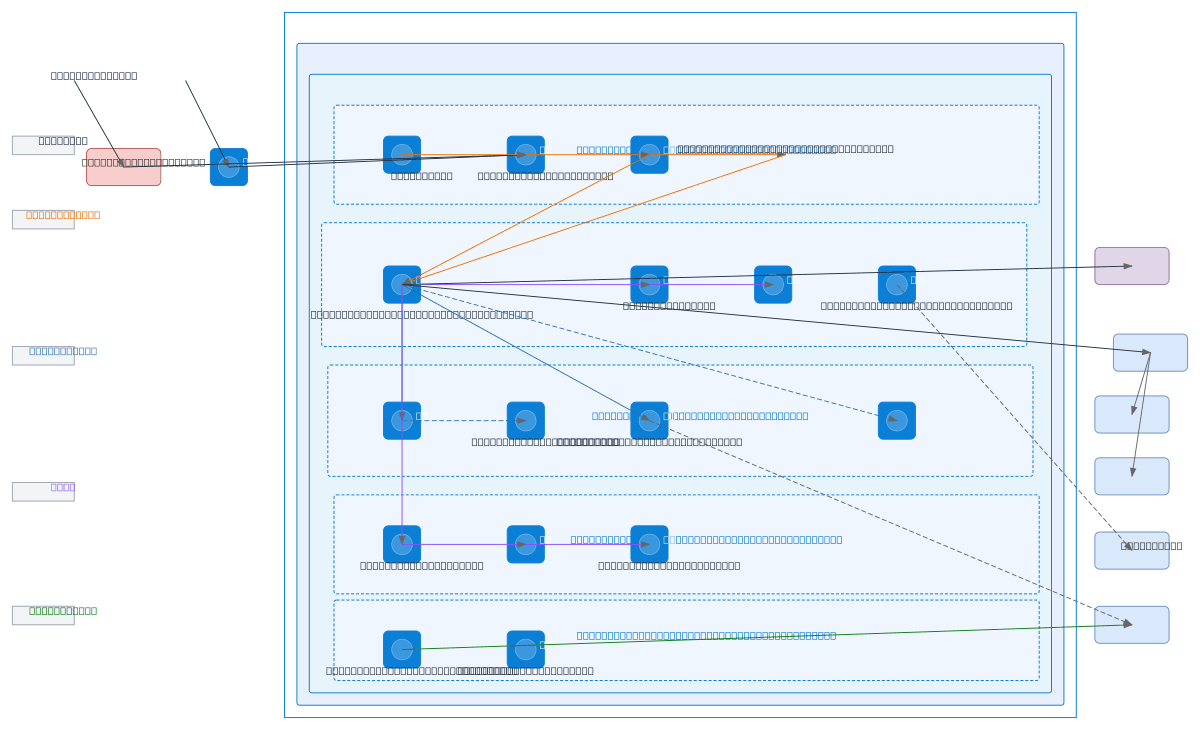
Azure Three-Tier Application with External
About This Architecture
Azure three-tier application architecture integrating Okta and Azure AD for identity, Azure Front Door with WAF for edge protection, and App Service hosting a Blazor WebAssembly frontend with DotNet Core API backend. Data flows through Azure SQL Database with read replicas, Azure Blob Storage, Redis cache, and Service Bus, while Azure Key Vault and Managed Identity enforce least-privilege access across all tiers. Observability is centralized via Application Insights and Log Analytics, with Azure Functions handling scheduled CIS tasks and Private Link enabling secure on-premises SFTP and Oracle Fusion integration. Fork this diagram to customize subnets, add additional App Service instances, or adjust WAF rules for your compliance requirements.
People also ask
How do I design a secure three-tier Azure application with Okta and Azure AD authentication, SQL Database, and on-premises integration?
This diagram shows a production-ready Azure architecture using Azure Front Door and WAF for edge security, App Service for Blazor and DotNet Core tiers, Azure SQL with read replicas for data, and Private Link for secure on-premises connectivity. Identity is federated through Okta for external users and Azure AD for internal users, with Key Vault and Managed Identity enforcing least-privilege acces
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing secure, multi-tier enterprise applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.