Azure Proplan Multi-Tenant App Architecture
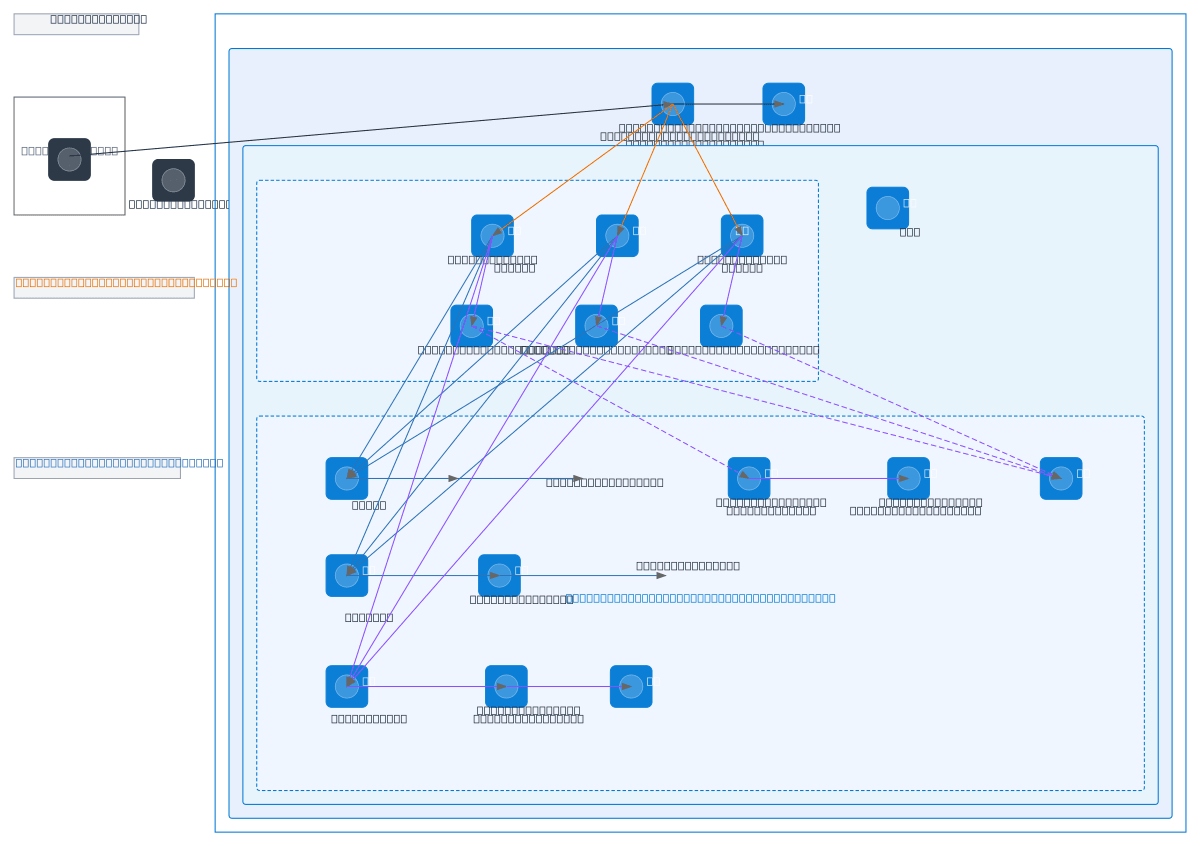
About This Architecture
Multi-tenant SaaS architecture on Azure using Front Door WAF, App Service Plan with three instances, and private endpoints for secure data access. Traffic flows from clients through Azure Front Door with WAF policies to load-balanced App Services in a virtual network, which connect via private endpoints to Azure SQL Elastic Pool, Storage Account, Key Vault, and Log Analytics. This architecture isolates each tenant's database and blob storage while maintaining shared compute and secrets management, reducing blast radius and improving compliance. Fork this diagram on Diagrams.so to customize subnets, scale App Service instances, or adjust WAF rules for your multi-tenant workload. The private endpoint layer ensures zero-internet exposure for backend services while Managed Identity provides secure authentication without credential storage.
People also ask
How do I architect a secure multi-tenant SaaS application on Azure with isolated customer data and private backend access?
This diagram shows a production-ready multi-tenant architecture using Azure Front Door with WAF for traffic filtering, three App Service instances for compute, and private endpoints connecting to Azure SQL Elastic Pool (one database per customer), Storage Account (per-customer blob containers), Key Vault, and Log Analytics. Managed Identity eliminates credential management while NSGs and private s
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing multi-tenant SaaS applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.