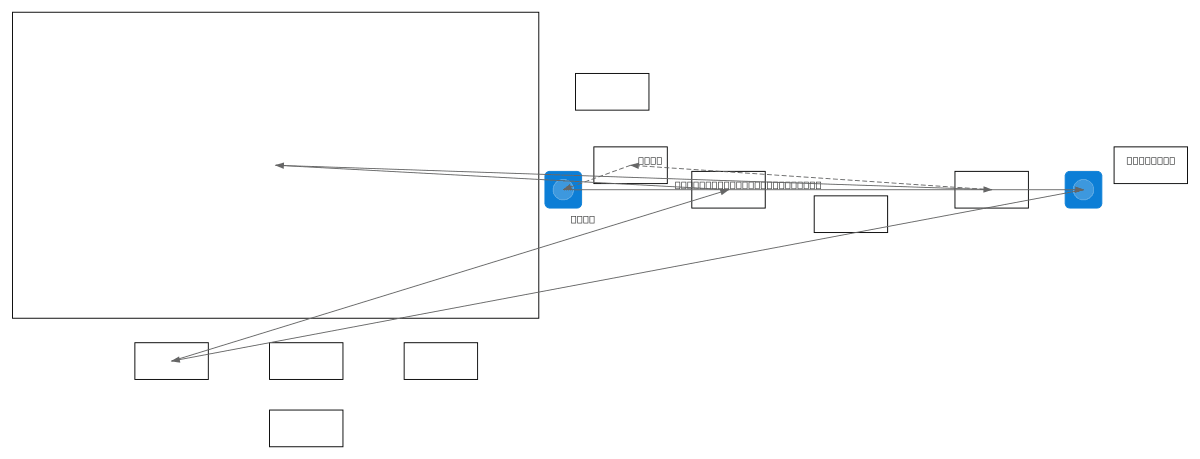
Azure PIM vs Permanent Access Flow
About This Architecture
Azure Privileged Identity Management (PIM) versus permanent access control flow demonstrates just-in-time role activation versus always-on role assignment. PIM flow routes user authentication through Azure AD/Entra ID to Azure PIM, where approvers validate requests before time-bound role activation with automatic access expiration and audit logging to Azure Monitor. Permanent access assigns roles directly without expiration, creating persistent security risks and compliance violations. This architecture illustrates why PIM reduces attack surface and enforces least-privilege access compared to legacy permanent role models. Fork this diagram to customize approval workflows, add conditional access policies, or integrate with your organization's governance framework.
People also ask
What is the difference between Azure PIM just-in-time access and permanent role assignment?
Azure PIM enforces just-in-time role activation through user authentication, approver validation, and time-bound assignments with automatic expiration and audit logging to Azure Monitor. Permanent access assigns roles directly without expiration, creating persistent security risks. PIM reduces attack surface by limiting privilege duration and enforcing least-privilege principles.
- Domain:
- Security
- Audience:
- Azure security architects implementing zero-trust identity governance
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.