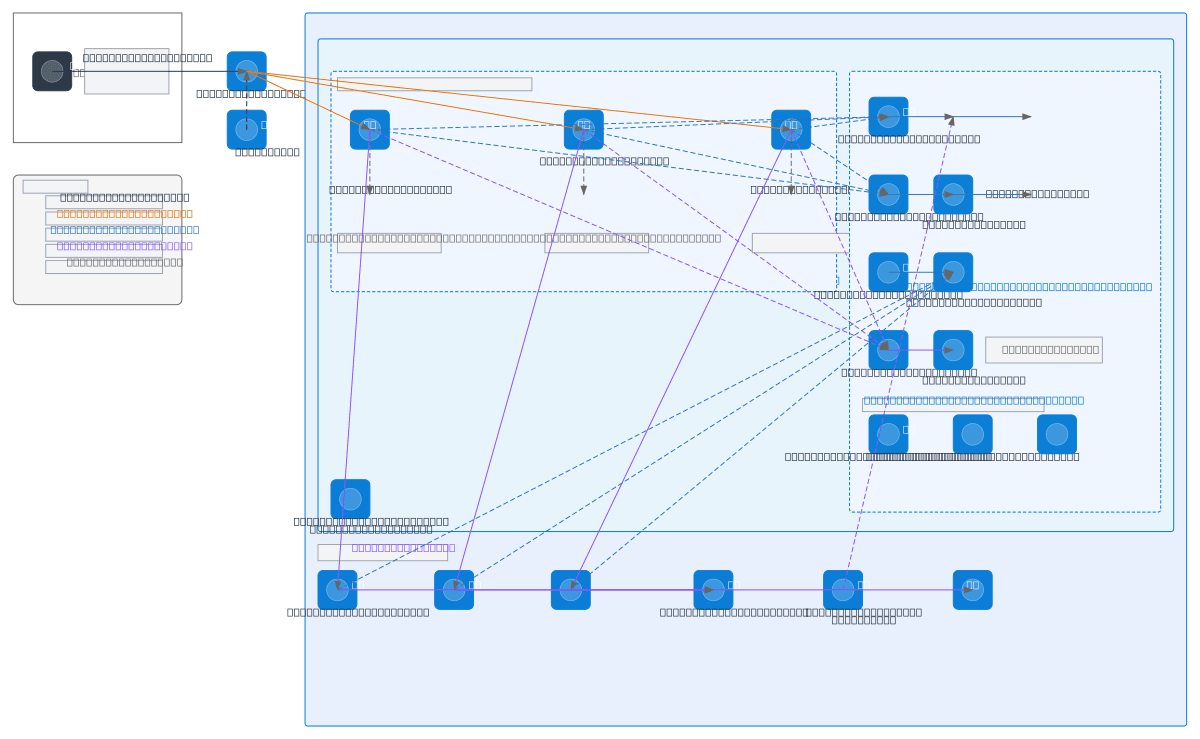
Azure Multi-Tenant SaaS - Front Door + Private
About This Architecture
Multi-tenant SaaS architecture on Azure using Front Door WAF for global traffic routing, three App Service instances with staging slots for zero-downtime deployments, and private endpoints securing all data access. App Services authenticate via System-Assigned Managed Identities to Azure SQL Server elastic pools, Storage Account blob containers, and Key Vault secrets—all isolated within a single VNet using private DNS zones and NSGs. Application Insights and Log Analytics provide unified monitoring across all tenant workloads. This pattern demonstrates Azure best practices for isolation, compliance, and operational excellence in production SaaS environments. Fork this diagram on Diagrams.so to customize resource names, regions, or add additional App Services and storage tiers. Consider adding Azure API Management or Traffic Manager for advanced routing and failover scenarios.
People also ask
How do I architect a secure multi-tenant SaaS application on Azure with private endpoints and managed identities?
This diagram shows a production Azure SaaS architecture where Azure Front Door with WAF routes HTTPS traffic to three App Service instances, each with staging slots for safe deployments. All backend services—Azure SQL Server, Storage Account, and Key Vault—are accessed via private endpoints using System-Assigned Managed Identities, eliminating public exposure and enforcing least-privilege access t
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing multi-tenant SaaS platforms
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.